Issue:
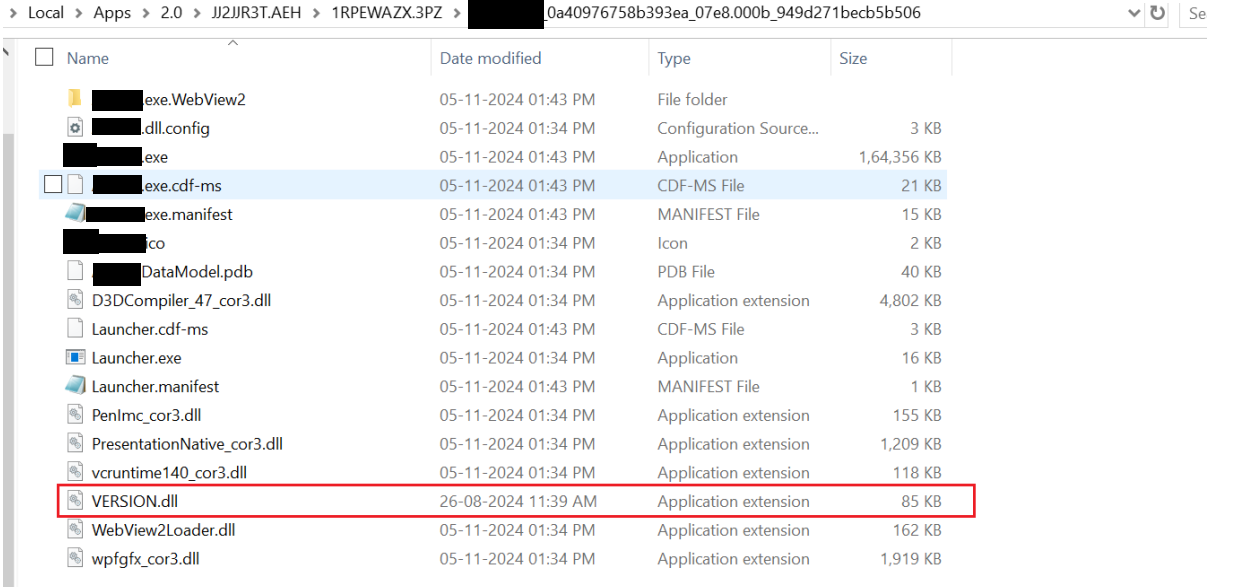
A WPF application targeting .NET 9 is published via ClickOnce. During a security test done security team, a malicious DLL named “VERSION.DLL” was placed in the application installation folder as shown in below image, which opens a calculator. Upon relaunching the application, this malicious DLL executed instead of the legitimate one.
Investigation Analysis:
Version.dll is a non core system dll present in System32 folder. The operating system first looks at the application installation folder and then looks in System32 folder as part of DLL search path during the app initialization.
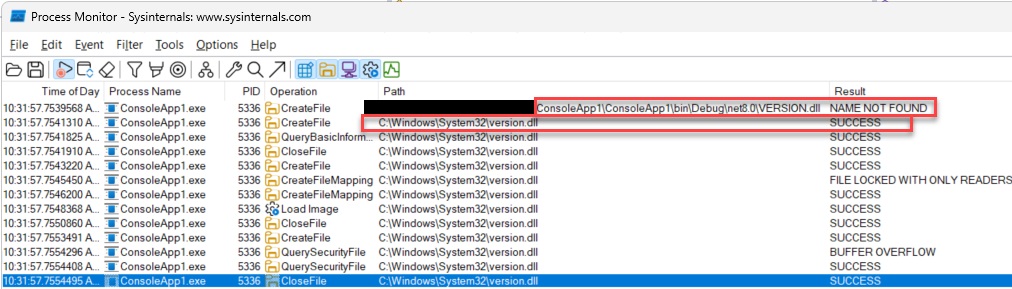
In an ideal scenario, the Version.dll from the System32 folder would load, as observed in the Process Monitor image below:
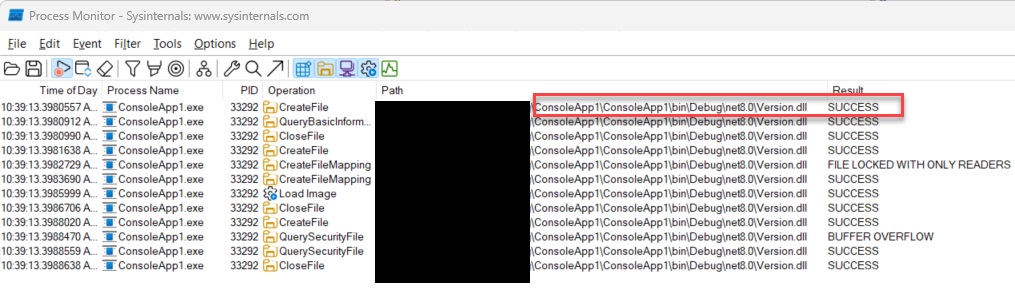
However, if a malicious DLL with the same name is present in the working directory, it gets loaded instead, as shown in the Process Monitor image below:
This behavior was reproduced with a simple console application targeting .NET 8 or .NET 9.
Operating System - Microsoft Windows [Version 10.0.22631.5189]
Steps to reproduce:
- Create a console application targeting .NET 8 or .NET 9.
- Place a rogue DLL named VERSION.dll in the bin\debug folder.
- Start the application via the executable.
- Result: The VERSION.dll gets loaded and executed, causing the application to fail to load.
- Expected Result: The VERSION.dll from the System32 folder should load, and the application should start normally.
Solutions tried but didn't work:
- Attempted to remove the current working directory from the DLL search path in the main() method. This did not work as the issue occurs before control reaches the Main method.
- Used a C/C++ bootstrapper to modify the DLL search path before calling the C# application. This solution also did not work.
Is there a way to prevent a malicious DLL with the same name as a non-core system DLL from being loaded? Feedback on this issue would be appreciated.