I am trying to get some mailbox related script working due to the basic auth disablement, and getting the titled error
This is the script I am calling (it's not the complete script, just testing access to the Azure app registration)
#Connect to GRAPH API
$tokenBody = @{
Grant_Type = "client_credentials"
Scope = "https://graph.microsoft.com/.default"
Client_Id = $clientId
Client_Secret = $clientSecret
}
$tokenResponse = Invoke-RestMethod -Uri "https://login.microsoftonline.com/$tenantID/oauth2/v2.0/token" -Method POST -Body $tokenBody
$headers = @{
"Authorization" = "Bearer $($tokenResponse.access_token)"
"Content-type" = "application/json"
}
#Send Mail
$URLsend = "https://graph.microsoft.com/v1.0/users/$MailSender/mailfolders/Inbox/messages"
#Invoke-RestMethod -Method POST -Uri $URLsend -Headers $headers
$resp_2 = Invoke-RestMethod -Method get -Uri $URLsend -ContentType "application/json" -Headers $headers
print $resp_2
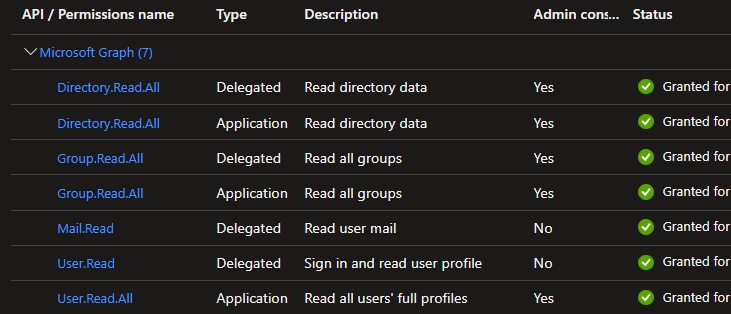
The issue seems to be related to the API permissions, this is what I currently have set
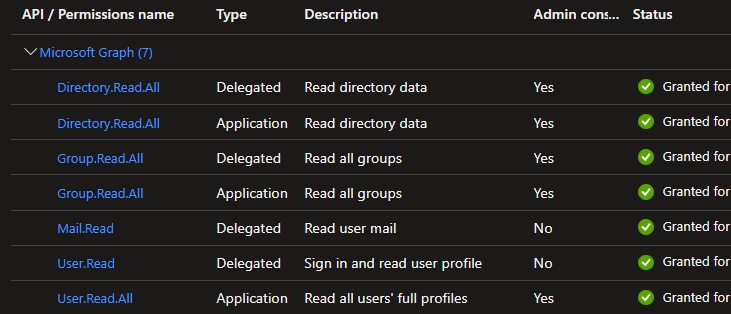
When I add an application permission for "Mail.Read" and consent it, it works, but this seems to allow any user to connect to any mailbox when the permission is approved, It ran calling the mailbox of a user in the $MailSender value who was not explicity listed as a user of this app registration and it still worked. For the Delegated permissions, the Mail.Read property states "Reads the signed-in users mailbox". When using the same permission under Application, it says "Reads ALL user mailboxes". Most of the equivalent app permissions appear much broader than their delagated counterpart.
How can I set minimum permissions for an account to read and delete mail from only the mailbox belonging to the service account thats defined in the $MailSender property?