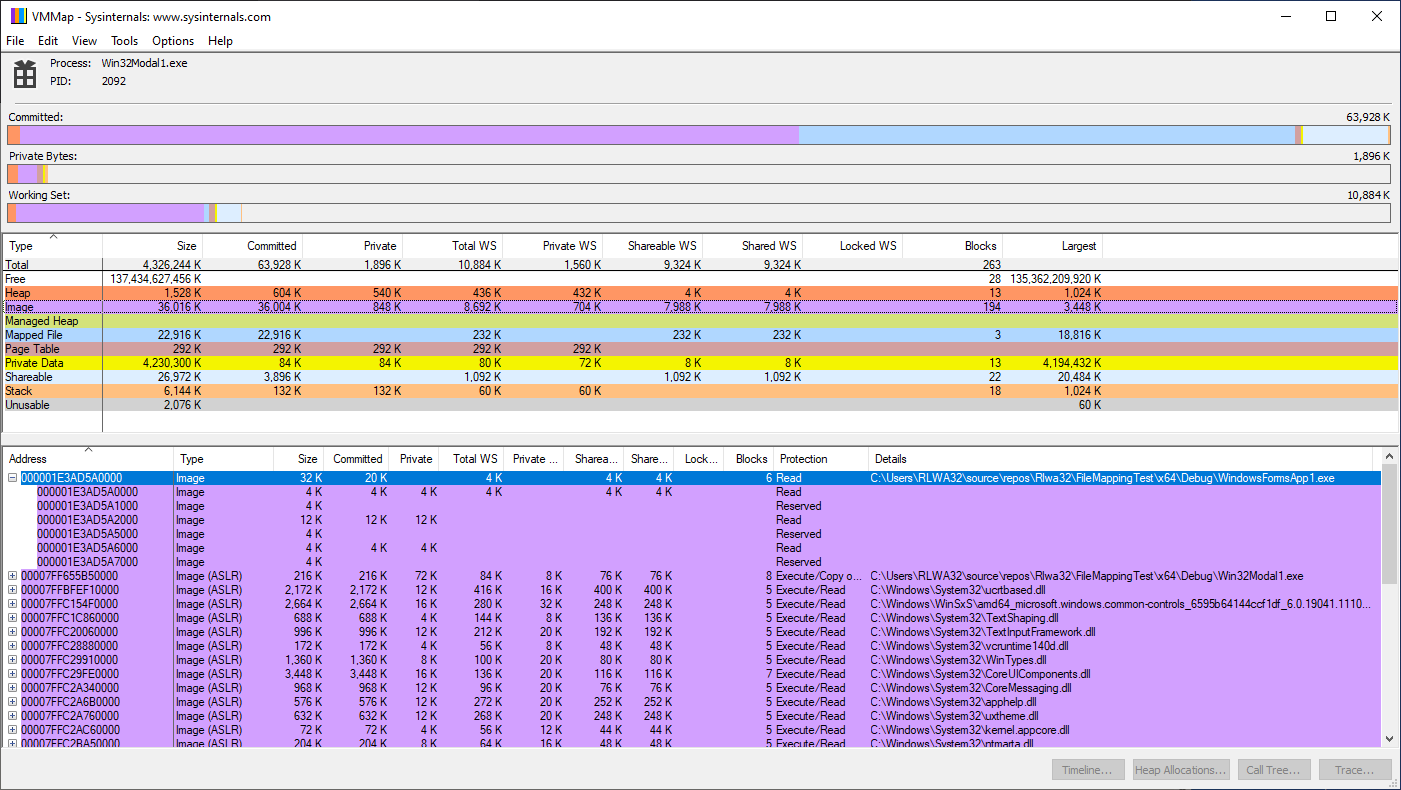
Following shows how VMMap has analyzed the address space of a process that has mapped a .Net executable using SEC_IMAGE. Note that VMMap shows serveral blocks, some of which are reserved and not committed. The first block is 4K and is committed memory.
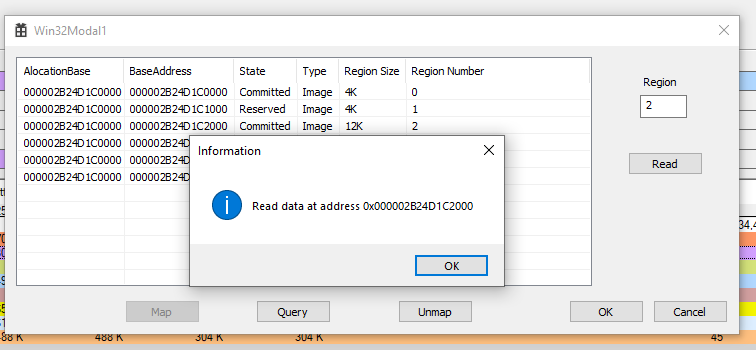
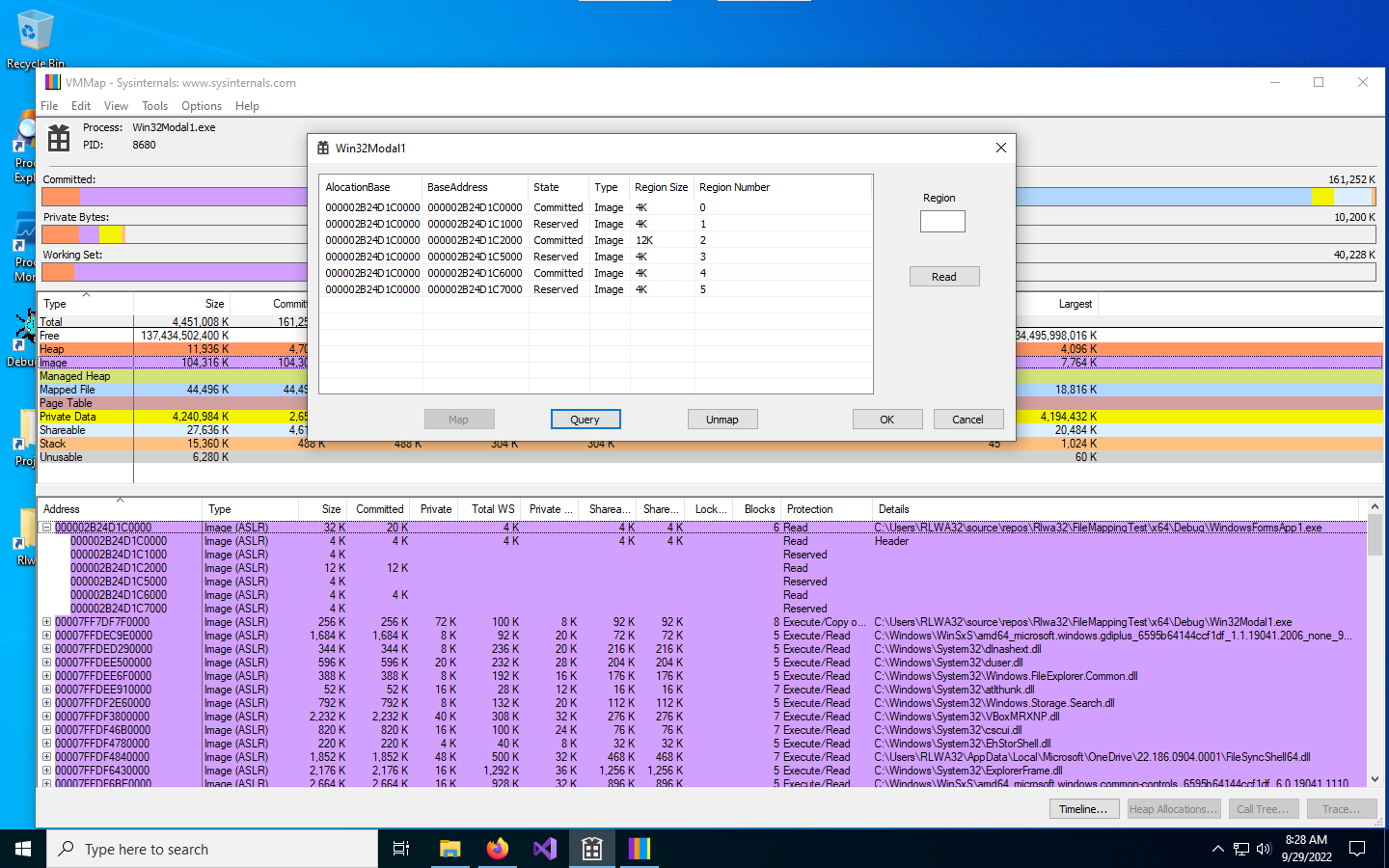
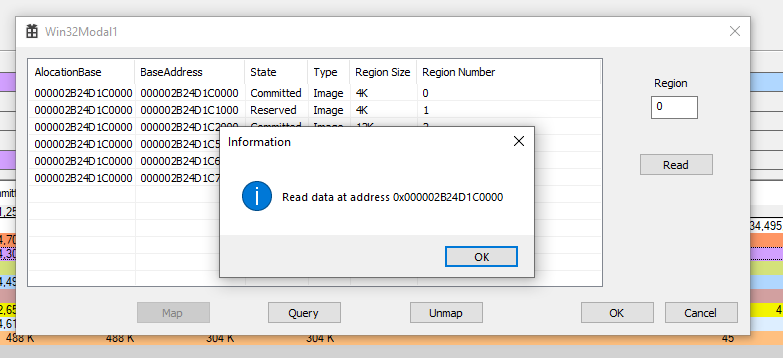
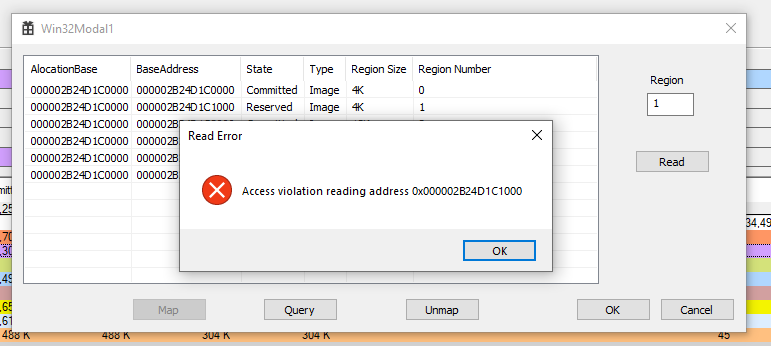
I updated the demo application to show the virtual memory mapping of the .Net executable. You can see that it corresponds to the information reported by VMMap. The following images show the result of attempting to read from committed blocks vs. reserved blocks.
VMMap and demo application
Committed block 0 -
Reserved block 1 -
Committed block 2 -