I'd recommend creating a security group that you can then apply to manage the group object in AD. The script (PowerShell) can be found on the following article:
How do I set permissions to manage Active Directory group membership? (by Kamal in 2019)
Cited from https://hkeylocalmachine.com/?p=769
# Define the $owner that will be able to manage the members of $group
$owner = "kamal";
$group = "citrix users";
# Try to get objects from AD
try {
$ownerobject = get-aduser $owner;
$groupobject = get-adgroup $group;
# If AD could not be read
} catch {
write-host "Could not get user/group information from Active Directory";
break;
}
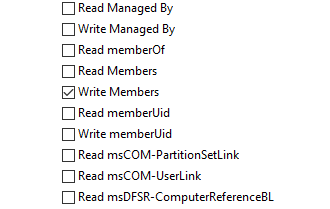
# Try to set "write members" rights on the group
try {
$ldapstring = "LDAP://" + $groupobject.distinguishedname;
$ldapgroup = [ADSI]$ldapstring;
[System.DirectoryServices.DirectoryEntryConfiguration]$secoptions = $ldapgroup.get_Options();
$secoptions.SecurityMasks = [System.DirectoryServices.SecurityMasks]'Dacl';
# Get SID
$identityref = $ownerobject.sid.value;
$sid = new-object System.Security.Principal.SecurityIdentifier ($identityref);
# Define rights to be applied
$adrights = [System.DirectoryServices.ActiveDirectoryRights]::WriteProperty;
$type = [System.Security.AccessControl.AccessControlType]::Allow;
# Define permission attribute to modify (writeMembers)
$objectguid = [Guid]"bf9679c0-0de6-11d0-a285-00aa003049e2";
$adrule = new-object System.DirectoryServices.ActiveDirectoryAccessRule ($sid, $adrights, $type, $objectguid);
# Apply new ACL
$ldapgroup.get_ObjectSecurity().AddAccessRule($adrule);
$ldapgroup.CommitChanges();
write-host ("ACLs updated for group: " + $group);
# If permissions could not be set
} catch {
write-host ("Could not set new ACLs on group: " + $group);
break;
}
I haven't seen many scripts for this, but it is the only one I've come across.
----------------------------------
If this is helpful please accept answer.