Dear all,
we are using LTSC version with Windows 10 1809 in our company. Among other things, we have configured Windows Defender so that users cannot disable the real-time protection, i.e. the GPO "Microsoft Defender AntiVirus" -> "Real-time protection" -> "Disable real-time protection" is set to "Disabled".
With Windows LTSC 1809 everything works fine.
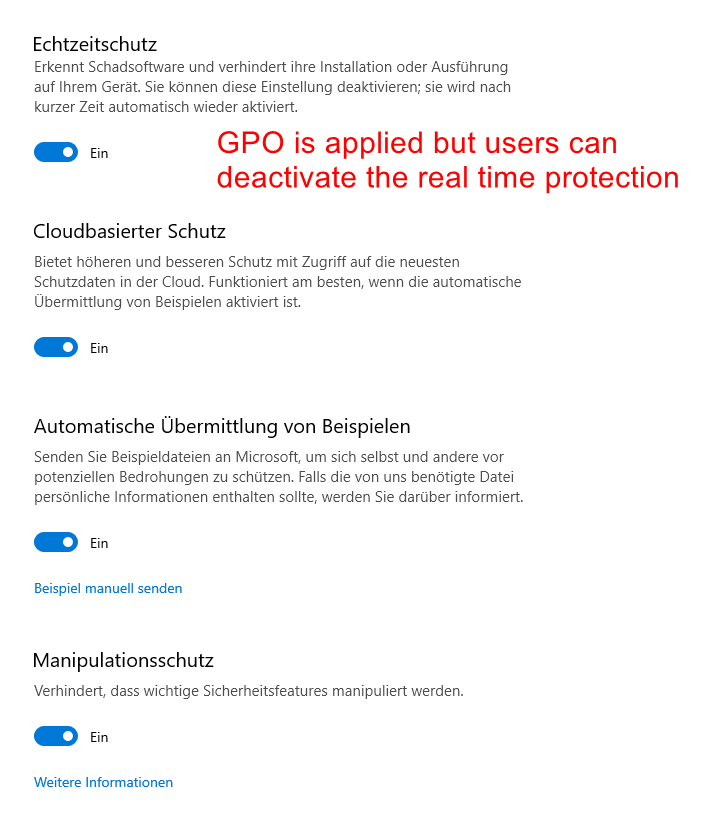
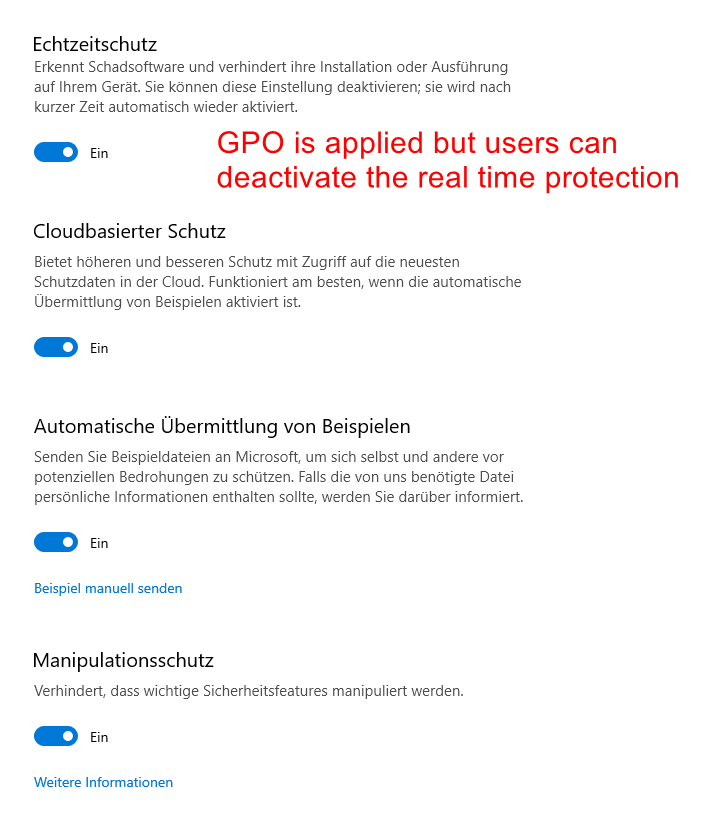
Now we have some clients with Windows 10 21H2 in use. Same Defender GPO is applied on the clients (is checked by me). With 21H2, tamper protection is turned on by default (we didn't configure it). This causes the above GPO stop working, i.e. users can disable real-time protection. This looks like this:
If a user deactivates the realtime protection it will be reactivated automatically by the tamper protection after a few minutes or after a reboot. This is nice but still problematic, because there seems to be a (security) hole here, because the realtime protection is disabled for the period (is also checked by us).
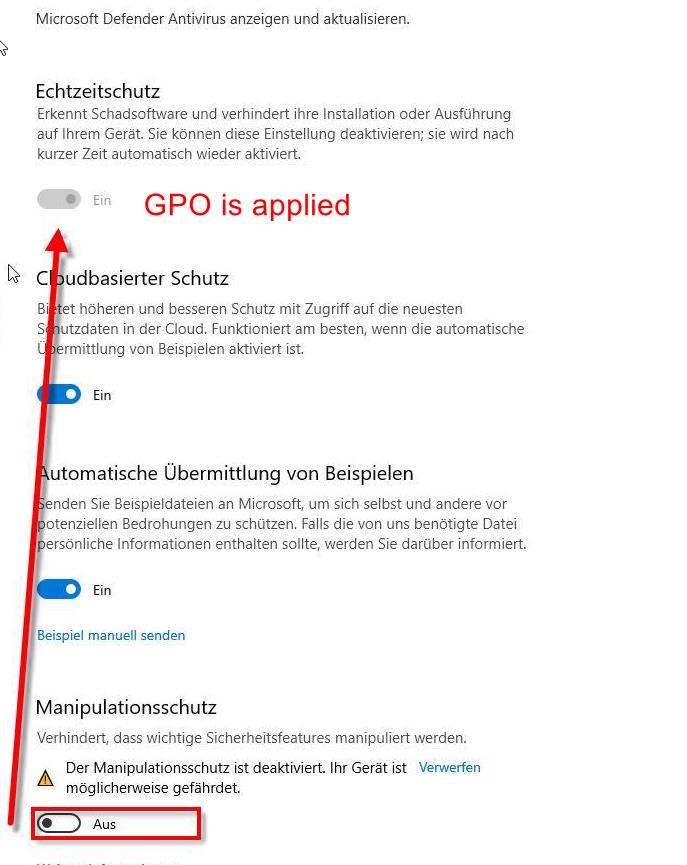
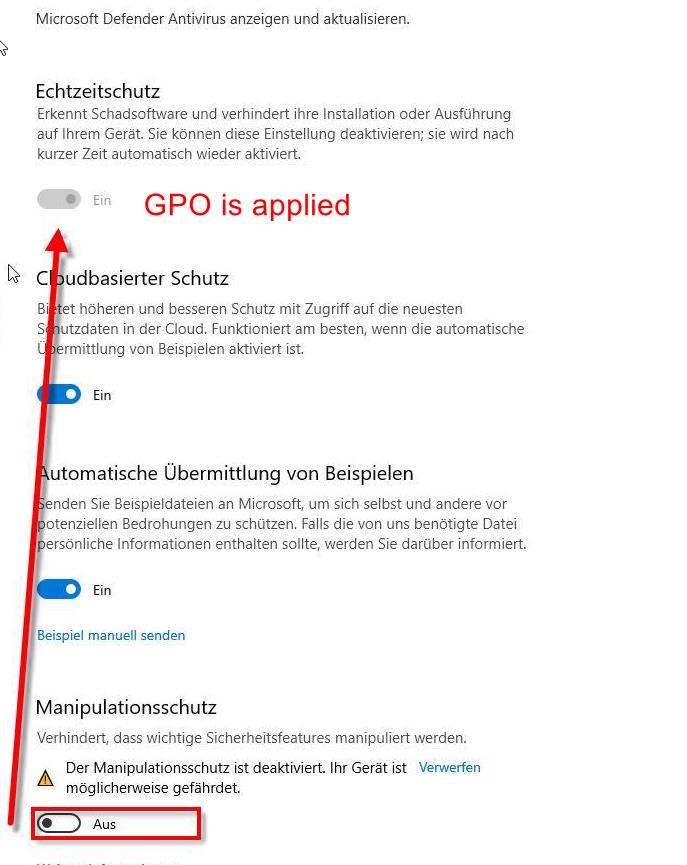
If I now deactivate the tamper protection (via mouse click - otherwise it is not possible) then the GPO seems to take effect immediately and the real-time protection can no longer be deactivated. It then looks like this:
Unfortunately, you can not disable tamper protection without Intune, MDM, so that the GPO always takes effect. I don't want to disable the tamper protection either. I basically just want to configure it that employees can never disable real-time protection (via UI or e.g. via Powershell aso), no matter what state the tamper protection has.
From my point of view this looks like a security gap as it is currently designed by MS, because I'we as admin can not specify that the real-time protection can never not be deactivated. Or did I miss something here? How do you solve this problem?
Best regards
Rainer