
Give this a try.
https://learn-powershell.net/2015/06/03/managing-privileges-using-poshprivilege
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
Not able to grant user rights assignment in group policy object using PowerShell
Is there any way or command to add user rights in group policy?
Manual steps:

Hi @ArpitShivhare-6858
I've had to do something similar in the past with automatic GPO generation, and the below was the only way I could find to do so. It basically creates the GPO manually, but it should work for your purposes
#Get details of user(s)
$user = Get-ADUser *username*
#Create text required for GptTmpl.inf file for the GPO, inserting the SIDs of the user(s) found previously
$text = "[Unicode]
Unicode=yes
[Version]
signature=`"`$CHICAGO$`"
Revision=1
[Privilege Rights]
SeTcbPrivilege = *$($user.SID)
SeIncreaseQuotaPrivilege = *$($user.SID)
SeChangeNotifyPrivilege = *$($user.SID)
SeBatchLogonRight = *$($user.SID)
SeServiceLogonRight = *$($user.SID)
SeManageVolumePrivilege = *$($user.SID)
SeAssignPrimaryTokenPrivilege = *$($user.SID)"
#Get domain controller to run all commands against
$dc = Get-ADDomainController
#Create new GPO
$newGPO = New-GPO -Name "Your GPO Name" -Server $dc
#Create new SecEdit directory in the GPO folder in SYSVOL
New-Item "\\EXAMPLE.COM\SYSVOL\EXAMPLE.COM\Policies\{$($newGPO.id)}\Machine\Microsoft\Windows NT\SecEdit" -ItemType Directory
#Create GptTmpl.inf file in SecEdit folder
$text | Out-File "\\EXAMPLE.COM\SYSVOL\EXAMPLE.COM\Policies\{$($newGPO.id)}\Machine\Microsoft\Windows NT\SecEdit\GptTmpl.inf"
#Set CSEs for new GPO - NB! otherwise settings won't be picked up by either the Group Policy Management console or the client
Set-ADObject "CN={$($newGPO.id)},CN=Policies,CN=System,DC=EXAMPLE,DC=COM" -Replace @{gPCMachineExtensionNames="[{827D319E-6EAC-11D2-A4EA-00C04F79F83A}{803E14A0-B4FB-11D0-A0D0-00A0C90F574B}]"} -Server $dc
#Force AD to process new GPO
$newGPO | Set-GPRegistryValue -Key HKLM\SOFTWARE -ValueName "Default" -Value "" -Type String -Server $dc
$newGPO | Remove-GPRegistryValue -Key HKLM\SOFTWARE -ValueName "Default" -Server $dc
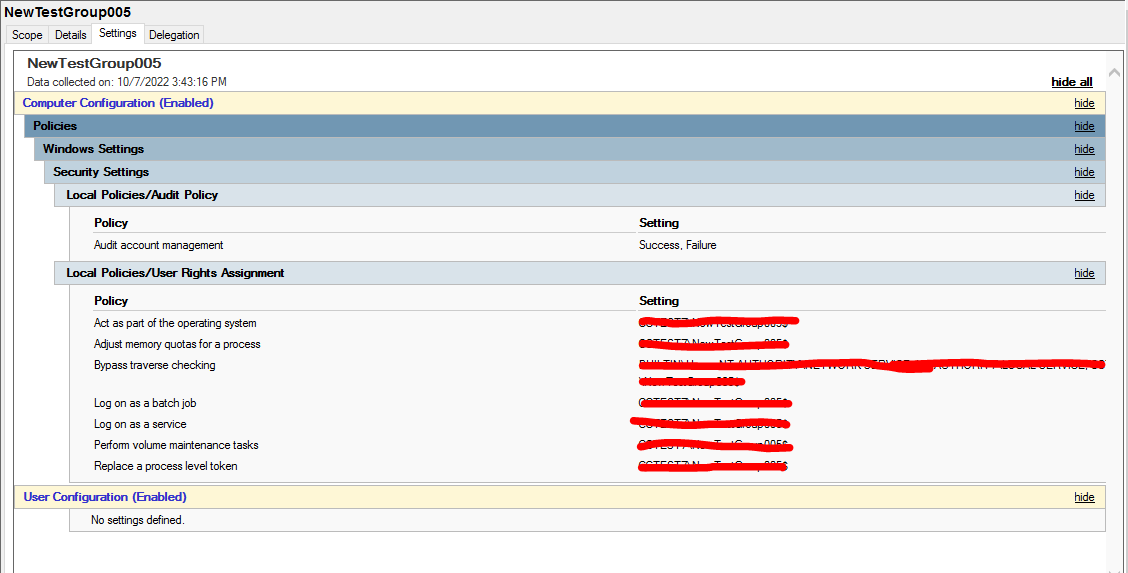
To add additional fields or users to the Local User Rights Assignments, I would recommend creating the GPO manually, then taking a look at the GptTmpl.inf file to see what format, values and syntax of the fields required. From my testing it uses SIDs, not the SamAccountName value, so you will have to pull the SID for each user that you need to add