Hi @SUNOJ KUMAR YELURU ,
Thank you for your answer - I'm sorry it has taken me this long to reply.
I have tried to assign both roles Azure Kubernetes Service Cluster Admin Role + Azure Kubernetes Service Cluster User Role to my user in order to access the namespace when creating the Kubernetes Service Connection - the roles were added successfully by following the commands on the link suggested:
Get the resource ID of your AKS cluster
AKS_CLUSTER=$(az aks show --resource-group myResourceGroup --name myAKSCluster --query id -o tsv)
Get the account credentials for the logged in user
ACCOUNT_UPN=$(az account show --query user.name -o tsv)
ACCOUNT_ID=$(az ad user show --id $ACCOUNT_UPN --query objectId -o tsv)
Assign the 'Cluster Admin' role to the user
az role assignment create \
--assignee $ACCOUNT_ID \
--scope $AKS_CLUSTER \
--role "Azure Kubernetes Service Cluster Admin Role"
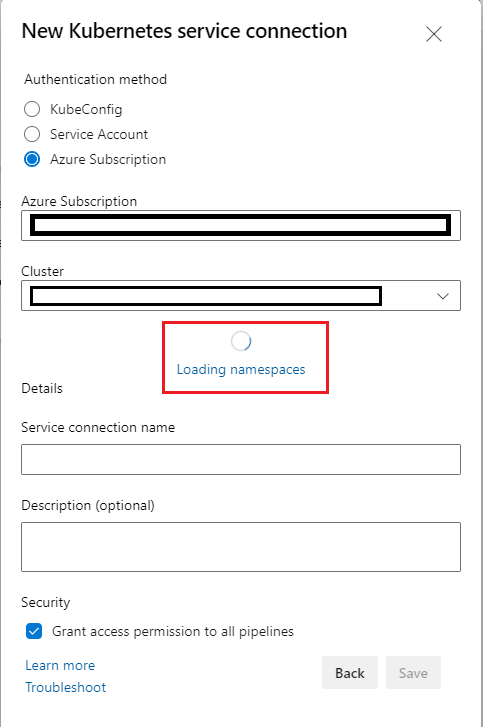
However, the issue persists, and I'm still getting the error:
Uncaught (in promise) TFS.WebApi.Exception: Error while fetching cluster credentials. Make sure you have clusterAdmin permissions on the cluster. Error from external server: Failed to query service connection API: 'https://management.azure.com/subscriptions/xxxx/resourcegroups/xxxx/providers/Microsoft.ContainerService/managedClusters/xxxx/accessProfiles/clusterAdmin/listCredential?api-version=2018-03-31'. Status Code: 'BadRequest', Response from server: '{
"code": "BadRequest",
"message": "Getting static credential is not allowed because this cluster is set to disable local accounts.",
"subcode": ""
}'