Container App Secrets Vs Key Vault
I'm looking to have a "container app" with a PHP Laravel web application open on port 80/443.
The application will need to connect to a MySQL database, it of course needs a host, database, username, and password.
Would the "Container App: Secrets" be considered secure enough to store the database password, and further is it safe to pass this to the container through the "Reference a secret" feature when defining the environment variables for the container?
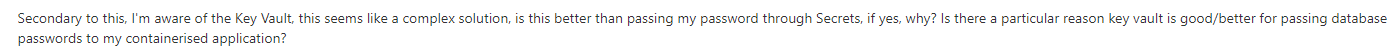
Secondary to this, I'm aware of the Key Vault, this seems like a complex solution, is this better than passing my password through Secrets, if yes, why? Is there a particular reason key vault is good/better for passing database passwords to my containerised application?
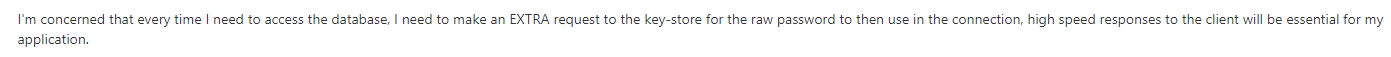
I'm concerned that every time I need to access the database, I need to make an EXTRA request to the key-store for the raw password to then use in the connection, high speed responses to the client will be essential for my application.
Perhaps this is more of a docker question, but are there security vulnerabilities with storing the database password at the single app container root and my app retrieving this from the container root during runtime? Or is it just not advised so passwords can be rotated?
This is all theory and research for now.
Thanks
Shea