Hello,
Thank you so much for posting here.
Whatever hash algorithm you choose under the Select the hash algorithm for signing certificates issued by this CA determines how the root CA's own CA certificate is signed and how it will, by default, sign other certificates and CRLs it issues. The hash algorithm was determined by the selection when install the CAs as following.
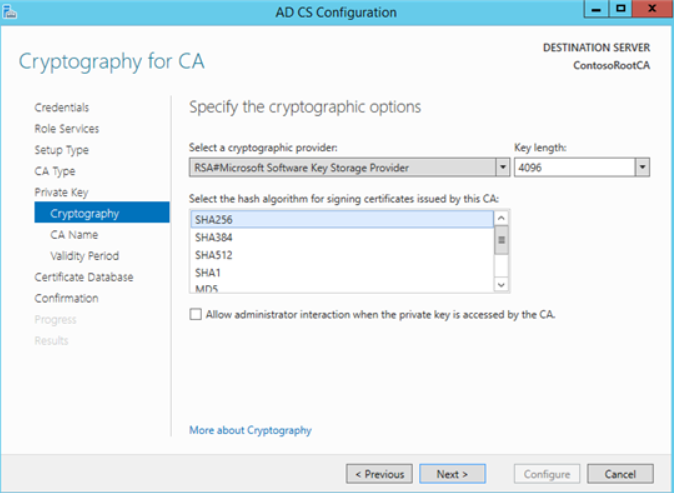
For the two tier PKI, The hash algorithm chosen on the root CA determines how the Subordinate CA's certificate is signed; During the Subordinate CA install, the hash algorithm you select under the Select the hash algorithm for signing certificates used by this CA determines how the certificates and CRLs issued by the Subordinate CA are signed.
The strength of the hash algorithm used by a CA to sign certificates is at least as strong as the hash algorithm used by its subordinate CAs. For example, if a CA uses SHA-256 to sign a subordinate CA certificate, then that subordinate CA must not use SHA-384 to sign certificates it issues. While planning a PKI deployment, ensure that the CA hierarchy uses consistent asymmetric cryptographic algorithms and key lengths when issuing certificates.
For more information, we could refer to:
Implementing SHA-2 in Active Directory Certificate Services
https://social.technet.microsoft.com/wiki/contents/articles/31296.implementing-sha-2-in-active-directory-certificate-services.aspx
Securing PKI: Planning Certificate Algorithms and Usages
https://learn.microsoft.com/en-us/previous-versions/windows/it-pro/windows-server-2012-r2-and-2012/dn786428(v=ws.11)
Hope the information is helpful. For any question, please feel free to contact us.
Best regards,
Hannah Xiong