Hi @Duane Wolford ,
Using powershell on your local system you can do:
Store the credentials in kube config
az aks get-credentials --resource-group rg-aks-nonprod-eastus-001 --name aks-nonprod-eastus-001 --admin -a
Rip credential secret token from kube config
kubectl -n kubernetes-dashboard describe secret $(kubectl -n kubernetes-dashboard get secret | sls admin-user | ForEach-Object { $_ -Split '\s+' } | Select -First 1)
Start local proxy
kubectl proxy
Open web browser to proxy url
http://localhost:8001/api/v1/namespaces/kubernetes-dashboard/services/https:kubernetes-dashboard:/proxy/
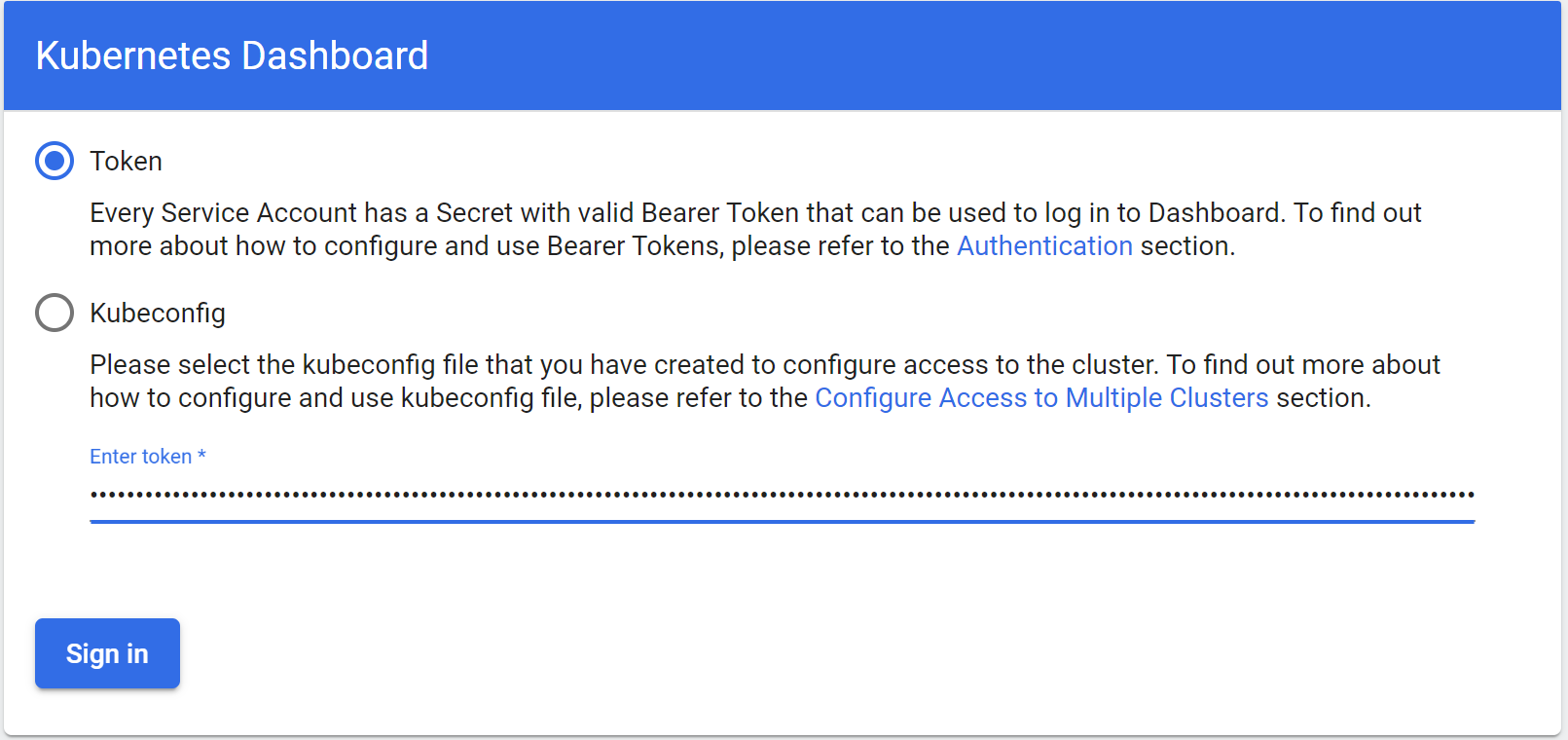
Paste in the cred secret token you dumped earlier from kube config
---
If this helps you solve your problem please mark this answer as accepted to help others with similar questions
