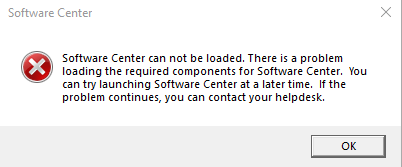
I can confirm that the solution posted by @Boopathi Subramaniam solved the issue for me as well. To ensure others are able to find this answer, I am posting the text of the log messages below so it will show up more readily in a web search.
The following is found in the mpcontrol.log file on the affected site server:
Call to HttpSendRequestSync failed for port 443 with status code 403, text: Forbidden SMS_MP_CONTROL_MANAGER 11/8/2020 11:12:47 AM 7020 (0x1B6C)
Http test request failed, status code is 403, 'Forbidden'. SMS_MP_CONTROL_MANAGER 11/8/2020 11:12:47 AM 7020 (0x1B6C)
The following may be found on the CcmNotificationAgent.log file on a client connecting to a Cloud Management Gateway:
[CCMHTTP] ERROR: URL=https://CONTOSO.CLOUDAPP.NET/CCM_Proxy_ServerAuth/72057594037927940/bgb/handler.ashx?RequestType=LogIn, Port=443, Options=1248, Code=0, Text=CCM_E_BAD_HTTP_STATUS_CODE BgbAgent 2020-11-08 11:15:31 AM 7220 (0x1C34)
[CCMHTTP] ERROR INFO: StatusCode=403 StatusText=CMGConnector_Forbidden BgbAgent 2020-11-08 11:15:31 AM 7220 (0x1C34)
Raising event:
instance of CCM_CcmHttp_Status
{
ClientID = "GUID:8A5350F6-613D-4FF1-BC44-99B4B0C6969E";
DateTime = "20201108191531.162000+000";
HostName = "CONTOSO.CLOUDAPP.NET";
HRESULT = "0x87d0027e";
ProcessID = 18388;
StatusCode = 403;
ThreadID = 7220;
};
BgbAgent 2020-11-08 11:15:31 AM 7220 (0x1C34)
Successfully queued RefreshSecuritySettingsEvent event. BgbAgent 2020-11-08 11:15:31 AM 7220 (0x1C34)
Successfully queued event on HTTP/HTTPS failure for server 'CONTOSO.CLOUDAPP.NET'. BgbAgent 2020-11-08 11:15:31 AM 7220 (0x1C34)
Failed to post Login with error code 87d0027e. BgbAgent 2020-11-08 11:15:31 AM 7220 (0x1C34)
Failed to signin bgb client with error = 87d0027e. BgbAgent 2020-11-08 11:15:31 AM 7220 (0x1C34)
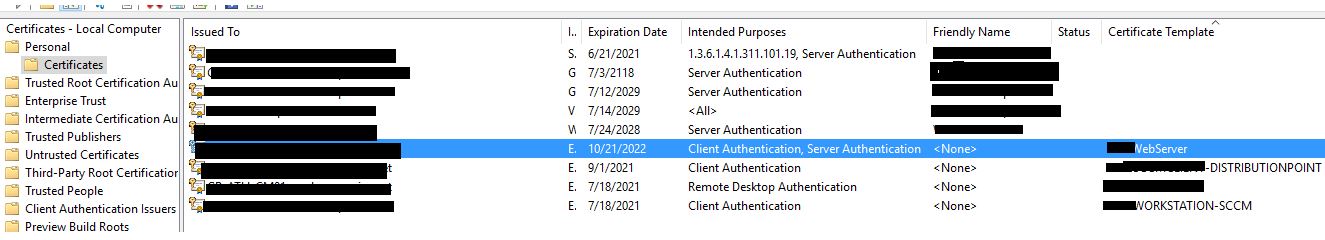
This issue may be affecting you if one or more certificates are returned after running the command below on your management point:
Get-Childitem cert:\LocalMachine\root -Recurse | Where-Object {$_.Issuer -ne $_.Subject} | Format-List
Once you have verified these root certificates are not needed, you can remove them by running this PowerShell command:
Get-Childitem cert:\LocalMachine\root -Recurse | Where-Object {$_.Issuer -ne $_.Subject} | Remove-Item