Hello fellas.
Usually I try not to bother anyone and try to find the solution on my own, but this time I got stuck.
I am developping the LogicApp to do some stuff in the Defender for Cloud. The issue I am facing is obtaining token from the AAD. This is how I call POST method from LogicApp: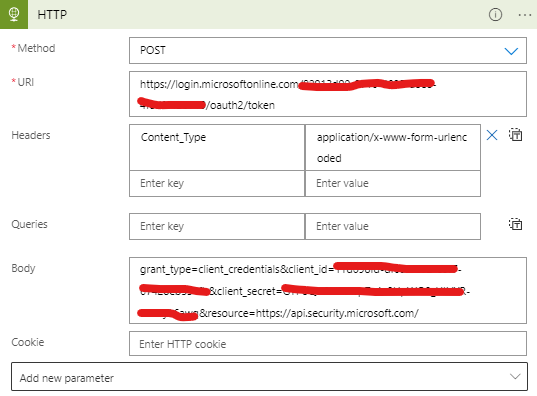
I read somewhene that "resource" should not be a part of the body, but I get same result w/ or w/o it.
When I execute this method, I get en error:
{
"error": "invalid_request",
"error_description": "AADSTS900144: The request body must contain the following parameter: 'grant_type'.\r\nTrace ID: a0fb2806-95b8-491e-9927-bf4b7e0b0e00\r\nCorrelation ID: d6971532-4e0a-4457-87d6-0bc7c7ba0bd6\r\nTimestamp: 2023-07-28 09:06:32Z",
"error_codes": [
900144
],
"timestamp": "2023-07-28 09:06:32Z",
"trace_id": "a0fb2806-95b8-491e-9927-bf4b7e0b0e00",
"correlation_id": "d6971532-4e0a-4457-87d6-0bc7c7ba0bd6",
"error_uri": "https://login.microsoftonline.com/error?code=900144"
}
Funny thing is that there is 'grant_type' in the body.
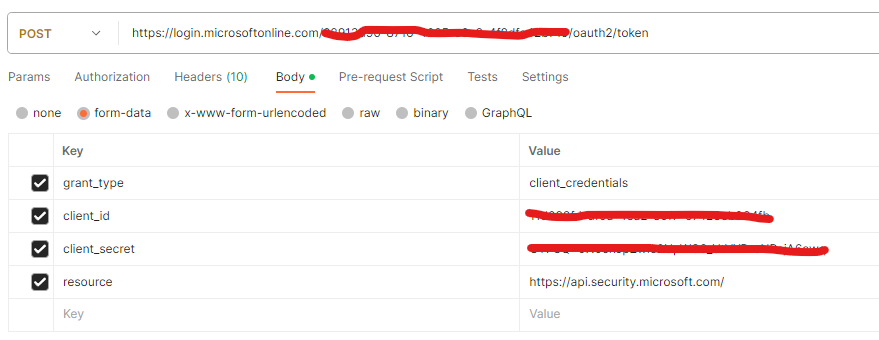
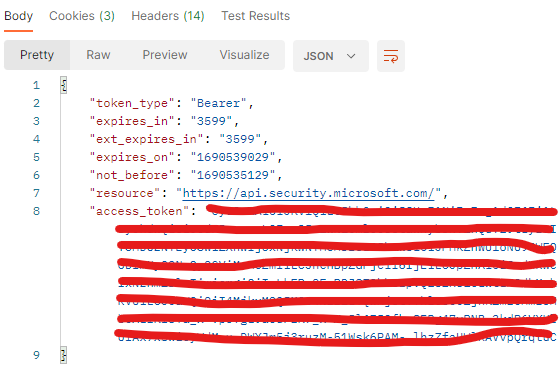
Even more funny thing is that the method invoked from Postman, using same parameters and values work just fine:
Obviously I am missing something, but what?
Any help much appreciated!
Sascha
