Hi, I am having all sorts of trouble deploying an Enterprise Wi-Fi profile (EAP-TLS) to fully managed Android (OS v13) devices via InTune. From what I have seen online recent security updates to Android now require additional information within Enterprise Wi-Fi profiles.
Specifically:
- DNS name that's used in the certificate presented by the Radius Server during client authentication to the Wi-Fi access point.
- Root certificate for server validation.
- Depending on your Android OS version and your Wi-Fi authentication infrastructure, the certificate requirements can vary. You may need to add your secure hash algorithm(s) (SHA) from the certificate used by your network policy server (NPS).
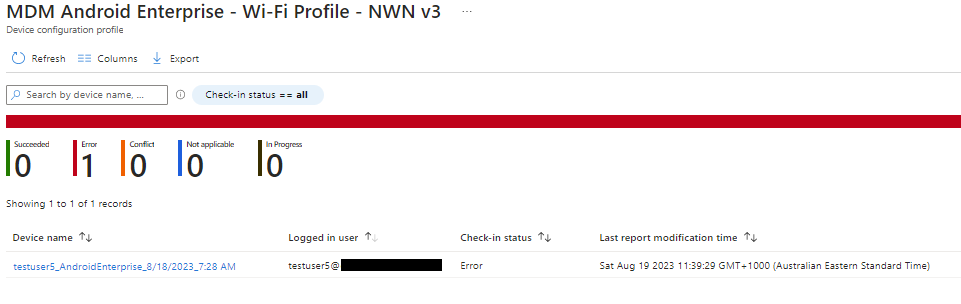
I have tried deploying profiles that meet all the required criteria, but InTune still reports an error when trying to deploy the profile to Android v13 devices. The Wi-Fi profile also can't be seen locally within Android Settings > User Certificates.
I can't be the only one facing this issue. Has anyone found a configuration which works?
I make sure to deploy a 'Trusted Root' profile first which installs my org's CA certificate on the device. Once that is installed I run the 'SCEP' profile to install a user certificate for Wi-Fi auth. Once those two profiles have succeeded, I deploy the Wi-Fi profile. To ensure each profile applies - and in the correct order - I deploy each profile using a separate security group (Step 1, Step 2, etc).
I am testing configurations with four Samsung devices. All four devices are running Android version 13. Two of the devices (Samsung Tab A's) are running the 1 July 2023 security patch. The other two devices (Samsung A22's) are running the 1 June 2023 security patch.
My latest Wi-Fi configuration was as follows (and failed):
SSID: (Keeping this Private)
Connect Automatically: Enable
Hidden Network: Disable
Proxy Settings: None
EAP Type: EAP-TLS
Radius Server Name: (FQDN of NPS server), (NPS Server Cert SHA-1 value), (NPS Server Cert SHA-256 value)
Root Certificate for Server Validation: (Linked to the Trusted Root CA profile I deploy prior to Wi-Fi config)
Authentication Method: Certificates
Certificates: (Linked to the SCEP profile I deploy prior to Wi-Fi config)
Identity privacy (outer identity): Not configured
References:
https://learn.microsoft.com/en-us/mem/intune/configuration/wi-fi-settings-android-enterprise#enterprise
https://developer.android.com/guide/topics/connectivity/wifi-enterprise
https://kb.vmware.com/s/article/92679
