Hello,
I was trying to connect the "Microsoft Defender XDR" connector with "Microsoft Sentinel", but I am facing the below error. I am not sure why Sentinel is not allowing to establish the XDR connector. As I am the Owner of the Azure Subscription which is reside in the same Tenant where I am the Global Administrator.
As per my research, I found that the App ID belongs to the Microsoft Owned Enterprise Application and when this application is trying to authenticate with the SIEM connector it gets restricted which can be verify under Non-interactive sign-in logs of the GA user.
Can anyone support me to resolve this error.
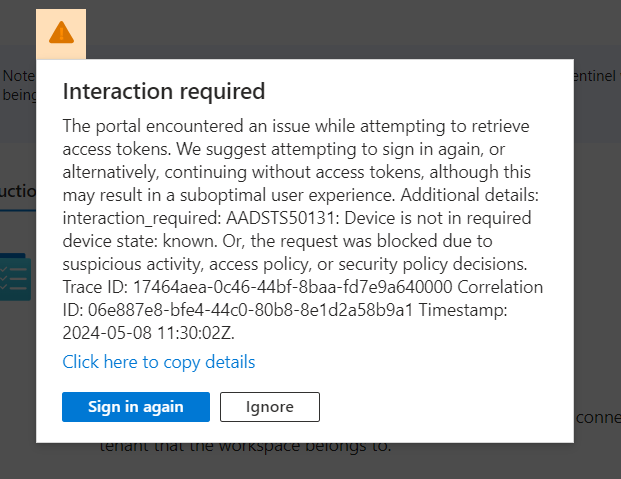
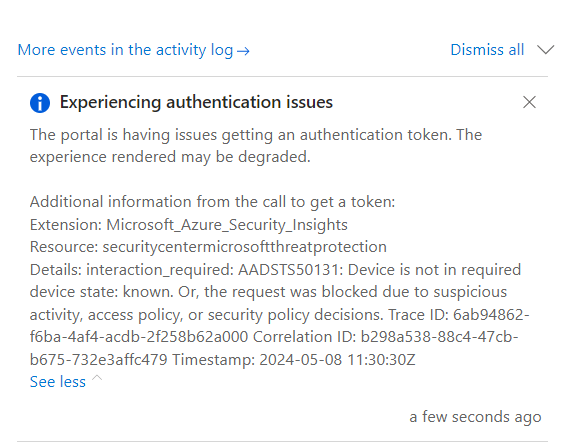
Error:
"The portal is having issues getting an authentication token. The experience rendered may be degraded. Additional information from the call to get a token: Extension: Microsoft_Azure_Security_Insights Resource: securitycentermicrosoftthreatprotection Details: interaction_required: AADSTS50131: Device is not in required device state: known. Or, the request was blocked due to suspicious activity, access policy, or security policy decisions. Trace ID: d504c379-5e36-4e75-b856-7fe436ba4c00 Correlation ID: 69c34683-6857-45c1-b856-13d352c53ac9 Timestamp: 2024-05-07 11:58:00Z"