Hi,
Please try to run a Task Sequence or Powershell Script.
Add a Run PowerShell Script step, enter “Invoke-MBamClientDeployment.ps1” as the script name and select the MBAM Deployment Script package. Now enter the following parameters;
-RecoveryServiceEndpoint “https://%YOURSERVER%/SMS_MP_MBAM/CoreService.svc” -EncryptionMethod “XTSAES256” -EncryptAndEscrowDataVolume -IgnoreEscrowOwnerAuthFailure -IgnoreReportStatusFailure -WaitForEncryptionToComplete

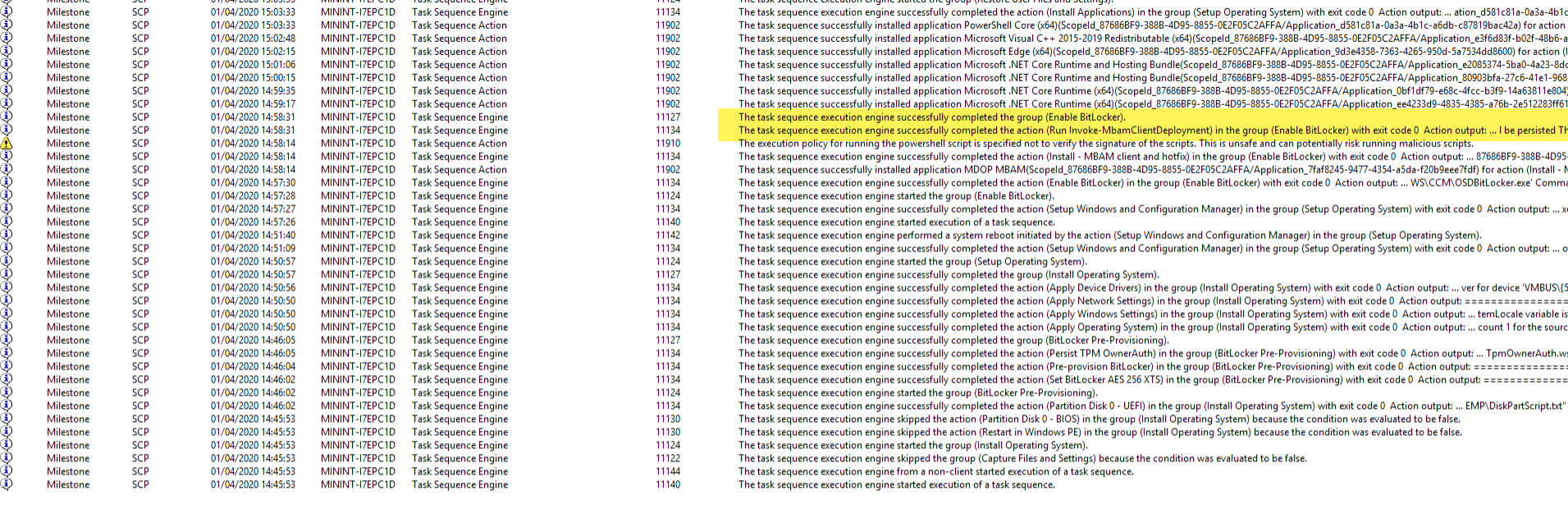
Monitoring the deployment via the status messages for the deployment, we can see the key was successfully escrowed to the Configuration Manager database.
For a complete description of the steps mentioned above, check out this article: