@Oury Ba-MSFT , The networking screenshot above (private access) is for the Azure SQL Server , which has one Azure SQL DB (Reporting DB) and one dedicated SQL Pool. There are two firewall rules under public tab, which is intentionally locked down. If your follow up comment is going to be a suggestion to add the IP of the Elastic Agent job then I do not know how to get that IP for the Elastic Agent. I followed the Microsoft documentation (linked below) to create the private end point to link the Azure SQL and Elastic jobs. It is running smoothly for the Azure SQL DB (Reporting DB) but getting the 'Failed to connect to the target database: Login failed for user '<token-identified principal>' for dedicated SQL POOL, which I don't understand. Both are linked to the same Azure SQL Server, where I set up the private endpoint shown in the Networking screenshot above.
'Configure Azure SQL elastic jobs private endpoint: Creating an elastic jobs private endpoint establishes a private link between the elastic job and the target server. Once configured, all communication between the elastic job agent and the target server will occur through the private endpoint
https://learn.microsoft.com/en-us/azure/azure-sql/database/elastic-jobs-tutorial?view=azuresql.'
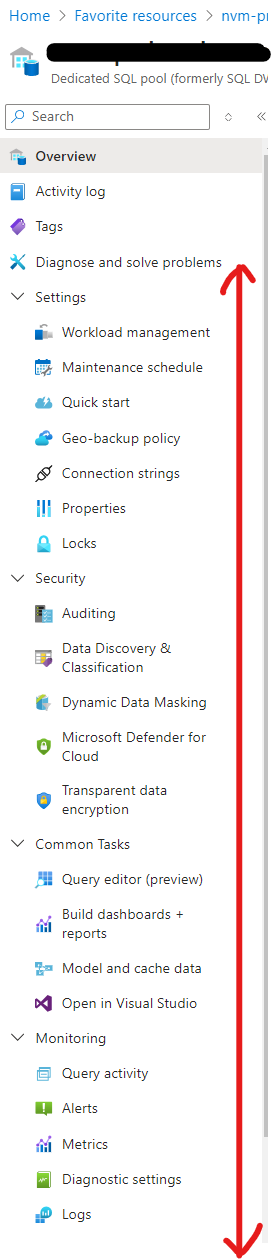
This is the screenshot of the Dedicated SQL Pool, which is probably using the Networking setup of the Azure SQL Server as I don't see Networking tab.