Hello,
I am a brand new admin at an old org that has many 1803, 1903, and 1909 PCs. The previous admins did not keep up with updates to the 300 desktops here. They only updated MS Office on these PCs. After abandoning their old WSUS server and their old Group Policy, I began using a new server (2016 with 14393) and a new policy. The new WSUS server provided cumulative updates to my 1909 desktop and also provided the 20H2 Feature Update to my desktop. However, no other existing Win10 PCs (1803, 1809, 1903, and 1909) will download the 20H2 feature update, or any other feature update that I have tried. They continue to download MS Office updates normally.
- I have confirmed that only the most recent Feature Update is downloaded and applied to my upgrade group in WSUS.
- I have created a new, stripped down basic group policy and placed my test machines in an OU that is blocked from inheriting any policy except this new WSUS policy
- GPUpdate /force, reboots, and GPResult show that only this new policy is applied to the test PCs.
- I have run the AJ Tek suggested cleanup script many times. The computers appear in WSUS where the updates show up as "Install" but also as "Not Applicable."
- I have manually run the Servicing Stack update for the appropriate version of Windows on each test PC (version verified with WinVer.exe).
- Existing PCs are able to communicate with WSUS, because I can telnet to 8530 on WSUS from test PCs, and the existing PCs download MS Office updates normally.
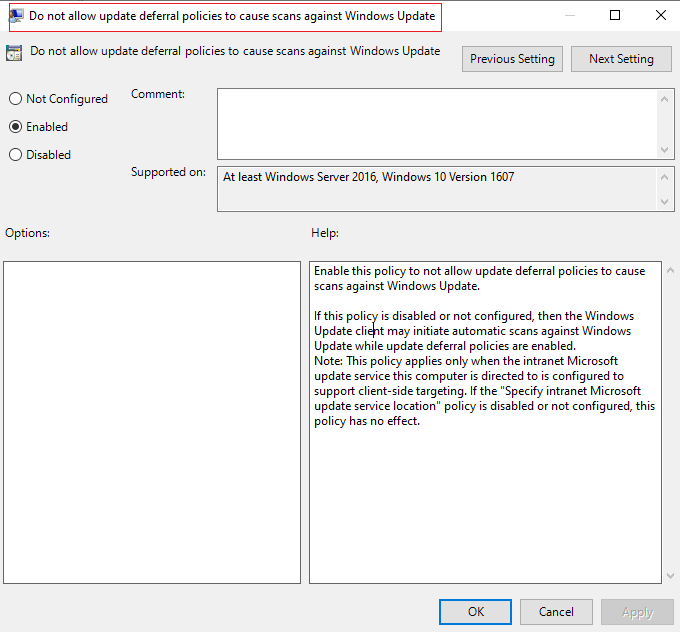
- I do get an "8024500C" error when I manually try to check for updates from the control panel, but I do not get that error when I use the PowerShell command to check for updates.
To make this more interesting, I have downloaded an 1803 ISO from Microsoft and used Rufus to create an installer. I then joined the test computers that I installed 1803 on to the domain and linked them to the new group policy. They immediately show up in the WSUS console, where I then add them to the upgrade group. These new installations show that they need 20H2 right away, and they download it alongside the most recent Defender definitions. By morning, the 20H2 update is installed and the computer is working fine. The newly upgraded PCs then reach out and download the 20H2 SSU and a .NET LCU from WSUS without a problem.
Any advice on getting my older, existing PCs to download and install the Feature Upgrades? I'm out of ideas. WSUS can be fussy, but I've never had this kind of trouble with it. I've attached a log from a PC that fails to download updates.
[56723-postable-logs.txt][3]