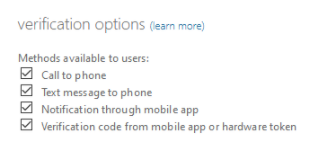
As far as I'm aware there's no way do this via Conditional Access if the option is enabled tenant-wide, but if you select only certain methods under verification options then it will force new users to use those methods.
If you want to force already registered users to register again, you can clear the StrongAuthenticationRequirements attribute using:
Set-MsolUser -UserPrincipalName username@yourtenant.onmicrosoft.com -StrongAuthenticationRequirements @()
Get-MsolUser -UserPrincipalName username@yourtenant.onmicrosoft.com | fl strong*
To reset MFA method for all users in the tenant, run:
Get-MsolUser | Set-MsolUser -StrongAuthenticationRequirements @()
You can also export users to a csv file and run the command with foreach loop, if you want to clear this attribute for limited users.
