Hello @kluangguy ,
Thank you for posting here.
To better understand our question, please confim the following information at your convenience:
1.Is your PDC physical machine or virtual machine? Or is your PDC hosted on Vmware/Hyper-V?
2.Is your AD environment single forest with single domain?
3.How many DCs in your Domain? Are they physical machine or virtual machine?
4.Did this problem happen suddenly? Or did we make any changes before the problem occurred?
5.Based on "We noticed all the server time (AD server, and domain member)", do you mean time on all the machines including all DCs and all workstations(member servers and domain clients) is auto adjusted with 8 hours ahead?
6.When the issue occurs, does the time on your internal NTP server normal?
Meanwhile, please check if the time configurations on all the machines are correct.
===PDC===
HLM\SYSTEM\CurrentControlSet\services\w32time\TimeProviders\VMICTimeProvider
Name: Enabled
Type: REG_DWORD
Data:0
Only if your PDC is virtual machine, you need to set the first entry.
Path: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\W32Time\Config
Key Name: AnnounceFlags
Type: REG_DWORD (DWORD Value )
Data: 0x5
Path: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\W32Time\Parameters\Type
Key Name: Type
Type: REG_SZ(String Value)
Data: NTP
Path: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\W32Time\Parameters
Key Name: NtpServer
Type: REG_SZ(String Value)
Data: time.windows.com,0x9
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\W32Time\TimeProviders\NtpServer
Key Name: Enabled
Type: REG_DWORD
Data: 1
===other DCs & domain clients & member servers===
Path: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\W32Time\Parameters\Type
Key Name: Type
Type: REG_SZ(String Value)
Data: NT5DS
Path: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\W32Time\Config
Key Name: AnnounceFlags
Type: REG_DWORD (DWORD Value )
Data: 0xa
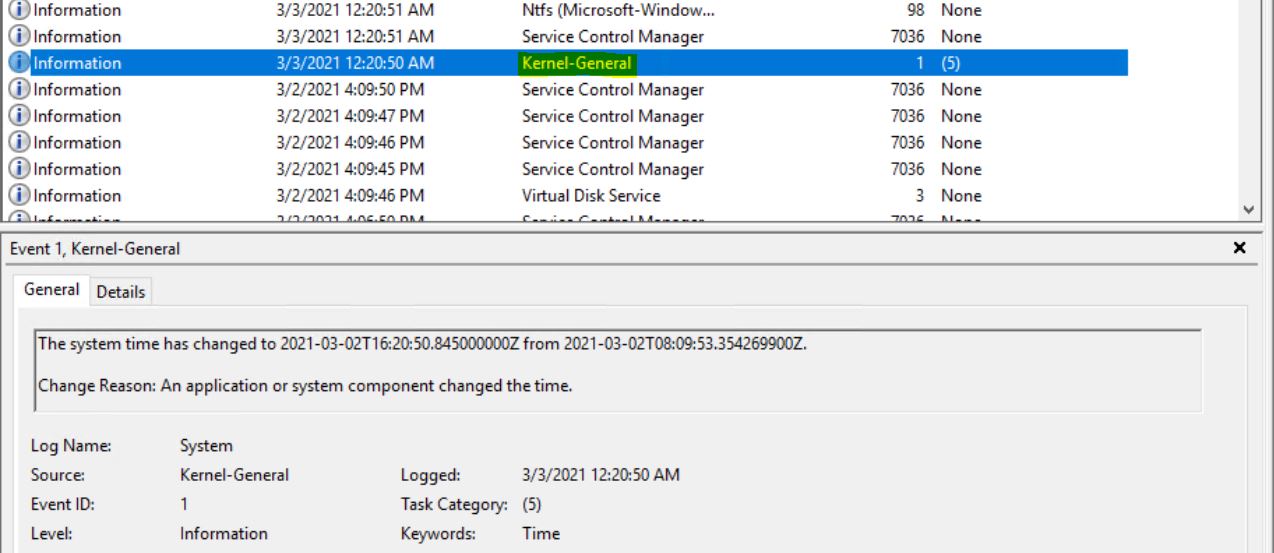
If time configurations are OK, we can configure audit policy for one/some/all the server that time (AD server, and domain member) is auto adjusted with 8 hours ahead.
Create GPO and link it to the OU with machines above and edit GPO as below:
Legacy audit policy:
Computer Configuration\Windows settings\security settings\local policies\audit policy\audit system events – Success and Failure
Or use advanced audit policies
(Tip: by default, once any advanced audit policy setting is configured, audit policies will overwrite all Legacy audit policies,so if you have not configured any advanced audit policy setting so far, please configure Legacy audit policy ):
Computer Configuration\Windows settings\security settings\Advanced Audit Policy Configuration\System\Audit Security State Change – Success and Failure
We can run the following commands on the domain controller to force the refresh policy and check whether the related audit policy settings are enabled:
gpupdate /force
auditpol /get /category:*
Then if the issue reoccurs, we can check the event ID 4616 via Security log\Event Viewer, check if there is any information we can get.
Reference
4616(S): The system time was changed.
https://learn.microsoft.com/en-us/windows/security/threat-protection/auditing/event-4616
Hope the information above is helpful.
Should you have any question or concern, please feel free to let us know.
Best Regards,
Daisy Zhou