I have set up a CMG recently and I am having trouble trying to install the SCCM agent over the internet using token based authentication. The errors I am seeing seem to indicate a certificate trust issue but there should be no need for certs for this to work. My test PC is in a workgroup and has never touched the domain. I have tested the CMG with a domain joined PC and I verified it works (I can deploy applications and software updates.)
I am running SCCM 2010 and to test this, I am following this MS doc https://learn.microsoft.com/en-us/mem/configmgr/core/clients/deploy/deploy-clients-cmg-token. I ran the bulk enrollment utility to generate the token and here is my installation command line:
ccmsetup.exe /mp:https://myCMG.CLOUDAPP.NET/CCM_Proxy_MutualAuth/72057594037927939 CCMHOSTNAME=myCMG.CLOUDAPP.NET/CCM_Proxy_MutualAuth/72057594037927939 SMSSiteCode=GOR SMSMP=https://myMP.myDomain.com /regtoken:eyJ0eXAiOiJKV1QiLCJhbGciOiJSUzI1NiIsIng1dCI6InpkZnpZMVNGM.....
The installation fails with these errors in ccmsetup.log:
[CCMHTTP] AsyncCallback(): ------------------------- ccmsetup 3/2/2021 10:53:37 PM 10656 (0x29A0)
[CCMHTTP] AsyncCallback(): WINHTTP_CALLBACK_STATUS_SECURE_FAILURE Encountered ccmsetup 3/2/2021 10:53:37 PM 10656 (0x29A0)
[CCMHTTP] : dwStatusInformationLength is 4 ccmsetup 3/2/2021 10:53:37 PM 10656 (0x29A0)
[CCMHTTP] : *lpvStatusInformation is 0x9 ccmsetup 3/2/2021 10:53:37 PM 10656 (0x29A0)
[CCMHTTP] : WINHTTP_CALLBACK_STATUS_FLAG_CERT_REV_FAILED is set ccmsetup 3/2/2021 10:53:37 PM 10656 (0x29A0)
[CCMHTTP] : WINHTTP_CALLBACK_STATUS_FLAG_INVALID_CA is set ccmsetup 3/2/2021 10:53:37 PM 10656 (0x29A0)
[CCMHTTP] AsyncCallback(): ----------------------------------------------------------------- ccmsetup 3/2/2021 10:53:37 PM 10656 (0x29A0)
Failed in WinHttpSendRequest API, ErrorCode = 0x2f8f ccmsetup 3/2/2021 10:53:37 PM 10656 (0x29A0)
RetrieveTokenFromStsServerImpl failed with error 0x80072f8f ccmsetup 3/2/2021 10:53:37 PM 10656 (0x29A0)
Failed to create SMS client object. Error 0x80040154 ccmsetup 3/2/2021 10:53:37 PM 10656 (0x29A0)
Failed to get CCM access token and client doesn't have PKI issued cert to use SSL. Error 0x80070002 ccmsetup 3/2/2021 10:53:37 PM 10656 (0x29A0)
CcmSetup failed with error code 0x87d00455
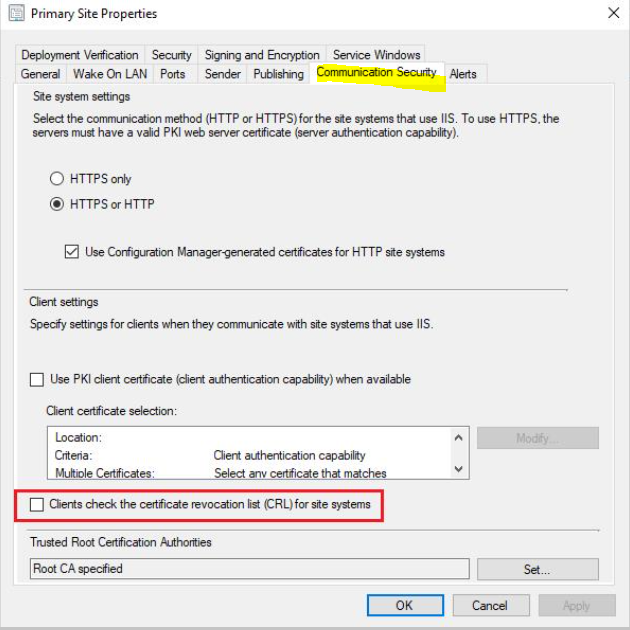
I imported the RootCA from my domain tried to reinstall. It errored again with the same messages except for WINHTTP_CALLBACK_STATUS_FLAG_INVALID_CA is set which makes sense. However the the RootCA or any certs should not be needed if I am understanding how the bulk token is supposed to work. I added /nocrlcheck to the command line and this allowed the SCCM agent to complete. Unfortunately after it finished installing the agent is refusing to communicate with the CMG as I get the same error messages in locationservices.log that I posted above.
I've read a lot of blogs and how-tos for this and I am doing exactly the same procedure. Does anyone have any thoughts about this? Thanks.
73946-ccmsetup-copy.log