Hi @Jenny Feng
Thanks for your reply!
Sorry but I not undestand some steps:
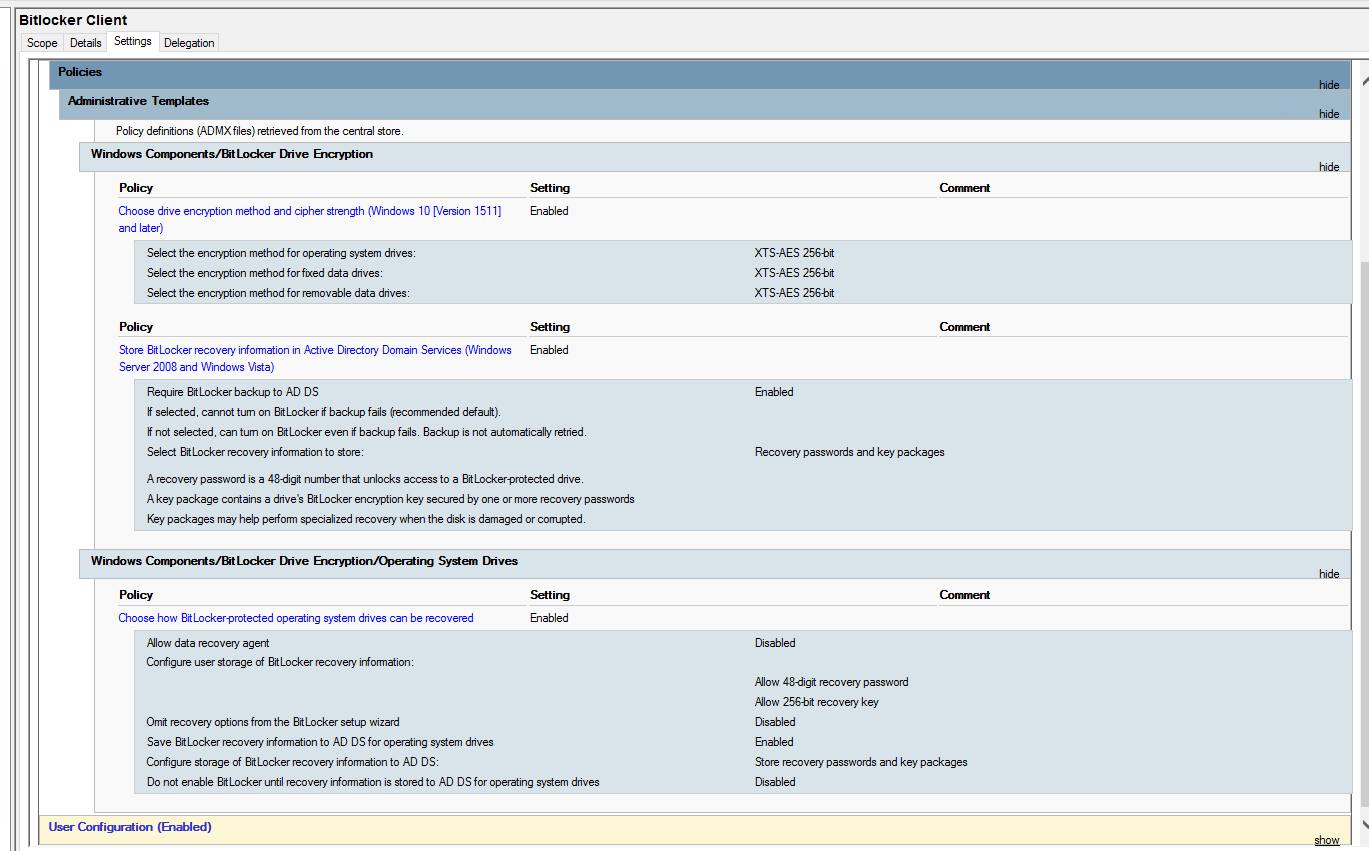
You set the options through GPO but to actually enable you need to run a script.
Until yesterday, Bitlocker Windows 10 function was always manually enabled on PCs after joining them to the domain.
Activation has always been done by:
Start> Manage Bitlocker
I admit that the bitlocker was often activated usung
- "Encrypt used disk space only"
- "New encryption mode"
I usually save recovery key on a document file.
Should I run the script to convert bitlocker mode (from Encrypt used disk space only to Encrypt entire drive)?
Domain administrators can view the BitLocker recovery password by
using the BitLocker Recovery Password Viewer.
I already enabled it from Server Manager (I installed roles about bitlocker on Domain Controller).
If a Group Policy setting was changed after the initial BitLocker deployment in
your organization, and then the setting was applied to previously encrypted
drives), no change can be made to the BitLocker configuration of that drive
except a change that will bring it into compliance.
Ok.
In my case I have all laptop encrypted manually from Control Panel menu.
From now I would avoid to it manually, but automatically.
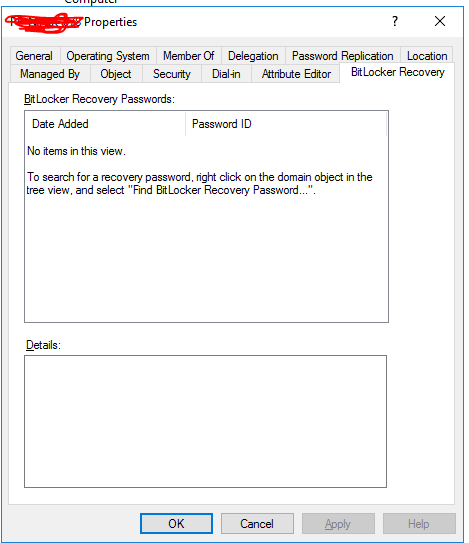
After that I would see actual recovery key of all laptop inside Active Directory.
In this moment, all computer tab about Bitlocker is empty (I did not apply GPO yet).
Is there a way that permit me to have inside Active Directory, all computer recovery key already encrypted by BitLocker?
I hope to be clear.
Federico