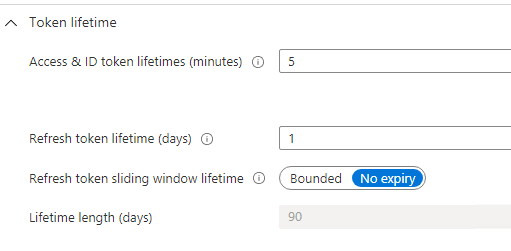
Hello @Trouble1 , thank you for reaching out. The Refresh token has a sliding window that is valid for 14 days and refresh token's validity is for 90 days. What the above statement means is, let's say you log in today using AAD, and AAD issues you a pair of tokens (access-token and refresh token) after successful authentication. Now, this access-token is valid for 1 hour (by default) and the issued refresh token is valid for 90 days. If this refresh token is used constantly to fetch new access tokens then the refresh token's life keeps on increasing as with each new request to AAD to fetch a new access-token, AAD, issues a pair of tokens (access-tokens and refresh-tokens). If using MSAL, the library discards the old refresh-token and uses the newly issued refresh-token for the next request to access-token from AAD in the second cycle.
Now let's say, the user logs in only once and remain active for 30 minutes and then closes the app, the user never comes back to access this application ever. Now in this case, what happens is that, since the sessions are no longer active, hence refresh token is not used by the application to renew the access-token after 1 hour. But the refresh token is still valid but remains in inactive state. Refresh token has a window of 14 days and waits for the user to access to the app so that the refresh-token can get renewed along with a new access-token. Now the refresh token keeps increasing this 14 days windows being in inactive state until it reaches 90 days. Once it reaches the 90th day, the refresh token gets invalidated. What that means is, if the user now tries to access the app after the 90th day, the user would be asked to enter the credentials and a new pair of access-token and refresh-token would be issued to the app after successful auth of the user.
For Refresh tokens it's the MaxInactiveTime which is by default set to 90 days and the maximum limit for that is 90 days too. You can get more details here.
------------------------------------------------------------------------------------------------------------------------------------------------------------------------
Note: As of January 30, 2021 you can not configure refresh and session token lifetimes. Azure Active Directory no longer honors refresh and session token configuration in existing policies. New tokens issued after existing tokens have expired are now set to the default configuration. You can still configure access, SAML, and ID token lifetimes after the refresh and session token configuration retirement.
Existing token’s lifetime will not be changed. After they expire, a new token will be issued based on the default value.
If you need to continue to define the time period before a user is asked to sign in again, configure sign-in frequency in Conditional Access. To learn more about Conditional Access, read Configure authentication session management with Conditional Access.
------------------------------------------------------------------------------------------------------------------------------------------------------------------------
Hope this helps.
Do let us know if this helps and if there are any more queries around this, please do let us know so that we can help you further. Also, please do not forget to accept the response as Answer; if the above response helped in answering your query.