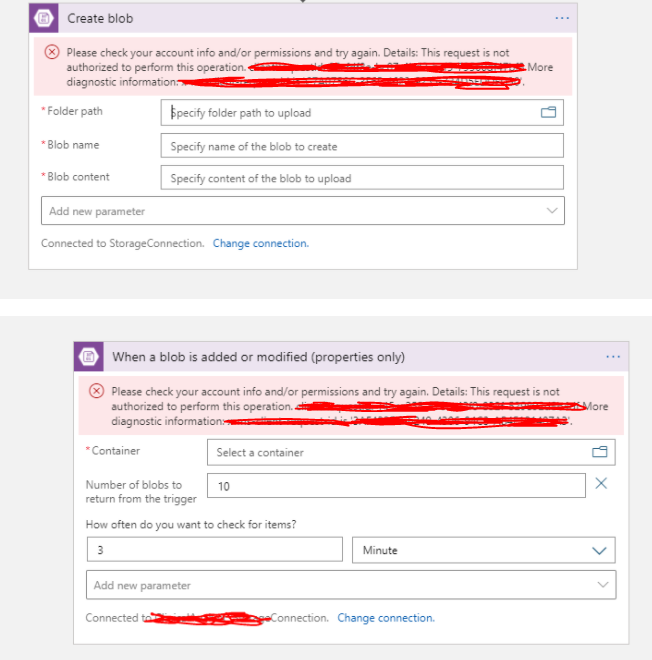
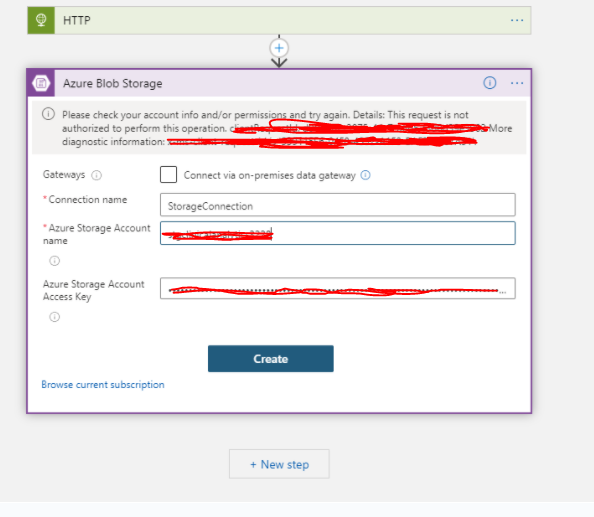
@Sarah C Benjamin Logic apps can't directly access storage accounts behind firewalls when they're both in the same region. As a workaround, put your logic apps in a region that differs from your storage account and give access to the outbound IP addresses for the managed connectors in your region, and the same is mentioned in this document.
This article talks about how you can communicate with storage REST services as the Local communication in the datacenter abstracts the internal IP addresses, so you can't set up firewall rules with IP restrictions and the same is mentioned in this document and the other solution for this scenario is mentioned on the same section of the article.
In nutshell, you cannot use a storage connector behind the firewall for the same region. The workaround is mentioned here and another article takes the about the same. If the storage account is in a different region behind the firewall then you need to give access to the access to the [outbound IP addresses for the managed connectors in your region.
You either need to use an HTTP trigger way to access the storage using storage REST API from the logic app within the same region. For different regions make sure you have added the outbound IP in your storage account.
Hope the above helps you to resolve the issue. Feel free to reach out to me if you need any assistance.
Please 'Accept as answer' and ‘Upvote’ if it helped so that it can help others in the community looking for help on similar topics.