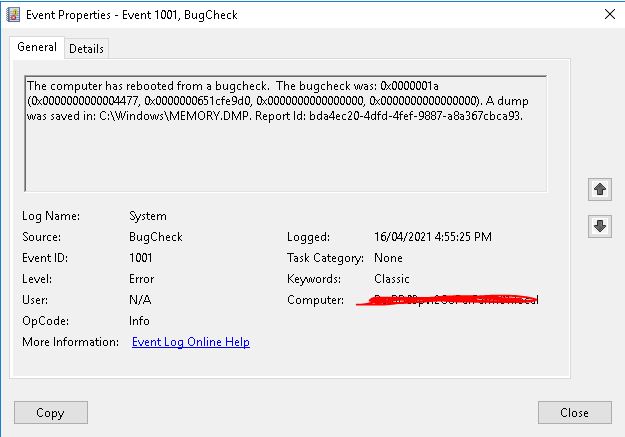
As title, our RD VM faced this problem twice with same bugcheck error.
It is a VM with Windows Server 2016. I've searched this error and found some case, but it won't like mine.
So I use WinDbg to analyst the dump with this accident, get the result as below:
Can anyone help me to identify the error and advise any suggestion? Thanks.
5: kd> !analyze -v
**
Bugcheck Analysis
**
MEMORY_MANAGEMENT (1a)
# Any other values for parameter 1 must be individually examined.
Arguments:
Arg1: 0000000000004477, A driver tried to write to an unallocated address in the
user space of the system process. Parameter 2 contains the
address of the attempted write.
Arg2: 0000000651cfe9d0
Arg3: 0000000000000000
Arg4: 0000000000000000
Debugging Details:
------------------
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 1874
Key : Analysis.DebugAnalysisManager
Value: Create
Key : Analysis.Elapsed.mSec
Value: 13988
Key : Analysis.Init.CPU.mSec
Value: 1483
Key : Analysis.Init.Elapsed.mSec
Value: 30074
Key : Analysis.Memory.CommitPeak.Mb
Value: 86
Key : WER.OS.Branch
Value: rs1_release
Key : WER.OS.Timestamp
Value: 2020-08-05T13:27:00Z
Key : WER.OS.Version
Value: 10.0.14393.3866
VIRTUAL_MACHINE: VMware
BUGCHECK_CODE: 1a
BUGCHECK_P1: 4477
BUGCHECK_P2: 651cfe9d0
BUGCHECK_P3: 0
BUGCHECK_P4: 0
PROCESS_NAME: System
TRAP_FRAME: ffffde80806a5540 -- (.trap 0xffffde80806a5540)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=0000000000000090 rbx=0000000000000000 rcx=0000000651cfe9f0
rdx=ffffaa80cbf3a9c4 rsi=0000000000000000 rdi=0000000000000000
rip=fffff80ac6ec35af rsp=ffffde80806a56d8 rbp=ffffde80806a57a0
r8=0000000000000010 r9=0000000000000004 r10=ffffc0815eeef4d0
r11=0000000651cfe9d0 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei pl nz na po nc
rdpdr+0x35af:
fffff80ac6ec35af 660f7f41e0 movdqa xmmword ptr [rcx-20h],xmm0 ds:0000000651cfe9d0=????????????????????????????????
Resetting default scope
STACK_TEXT:
ffffde80806a5278 fffff802ba8d1904 : 000000000000001a 0000000000004477 0000000651cfe9d0 0000000000000000 : nt!KeBugCheckEx
ffffde80806a5280 fffff802ba8d031f : 0000000000000002 ffffc0814cc99600 ffffde80806a54a8 0000000000000000 : nt!MiResolvePageTablePage+0x694
ffffde80806a5340 fffff802ba9ea661 : ffffc081504fd940 00000000000000ff ffffc08100000001 ffffc0814f314d78 : nt!MmAccessFault+0x61f
ffffde80806a5540 fffff80ac6ec35af : fffff80ac6eeaeee fffff80ac6ecc000 fffff80ac6eeb868 ffffc08160dc7cc0 : nt!KiPageFault+0x321
ffffde80806a56d8 fffff80ac6eeaeee : fffff80ac6ecc000 fffff80ac6eeb868 ffffc08160dc7cc0 0000000000000000 : rdpdr+0x35af
ffffde80806a56e0 fffff80ac6eeb432 : ffffc08164cd5470 fffff80200000090 0000000000000090 ffffde80806a58d0 : rdpdr+0x2aeee
ffffde80806a5760 fffff80ac6ee8ded : 00000000000000a4 0000000000000005 ffffde80806a58d0 ffffde80806a58d0 : rdpdr+0x2b432
ffffde80806a57d0 fffff80ac6ee8d2b : ffffc0815eae42e0 ffffc08159d12d70 fffff80ac6ecc000 ffffc08166e6556b : rdpdr+0x28ded
ffffde80806a5820 fffff80ac6ed93a9 : fffff802babb8702 ffffc0815eae42e0 ffffc0815eae42e0 fffff802ba8a7500 : rdpdr+0x28d2b
ffffde80806a5850 fffff80ac6ed8b96 : 0000000000000001 ffffc08166e65450 ffffde80806a59b9 ffffc0815eae42e0 : rdpdr+0x193a9
ffffde80806a58d0 fffff802ba8e5992 : ffffc08166e65450 0000000000000000 000000007246704e 00000000000000f0 : rdpdr+0x18b96
ffffde80806a5900 fffff80ac749b042 : ffffaa870ec16140 ffffaa870ec161e8 0000000000000000 fffff802baca7900 : nt!IopfCompleteRequest+0x112
ffffde80806a5a20 fffff80ac4833172 : ffffc0814da2edf0 fffff80200000c80 00000000000000a4 ffffaa871dc39380 : Npfs!NpFsdRead+0x202
ffffde80806a5ad0 fffff80ac6ed5c0b : 0000000000000000 0000000000000003 ffffc0816409a802 0000000000000202 : FLTMGR!FltpDispatch+0xe2
ffffde80806a5b30 fffff80ac6ec259a : ffffc0816409a860 ffffc08100000c80 0000000000000000 fffff80200000000 : rdpdr+0x15c0b
ffffde80806a5bc0 fffff802ba98a1cd : ffffc0815050d080 0000000000000080 fffff80ac6ec24d0 ffffc0814f314cf0 : rdpdr+0x259a
ffffde80806a5c10 fffff802ba9e4836 : ffffde807c058180 ffffc0815050d080 fffff802ba98a18c 0000000000000000 : nt!PspSystemThreadStartup+0x41
ffffde80806a5c60 0000000000000000 : ffffde80806a6000 ffffde80806a0000 0000000000000000 0000000000000000 : nt!KiStartSystemThread+0x16
SYMBOL_NAME: rdpdr+35af
MODULE_NAME: rdpdr
IMAGE_NAME: rdpdr.sys
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 35af
FAILURE_BUCKET_ID: 0x1a_4477_rdpdr!unknown_function
OS_VERSION: 10.0.14393.3866
BUILDLAB_STR: rs1_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {a9de405d-a06e-b156-1e3d-083f7440b64d}
Followup: MachineOwner
---------