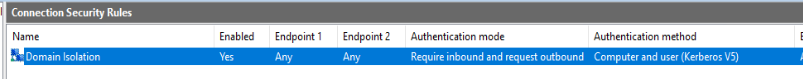
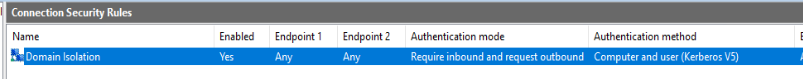
I've configured Connection Security Rules to require inbound authentication using Kerberos:
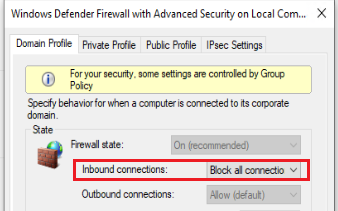
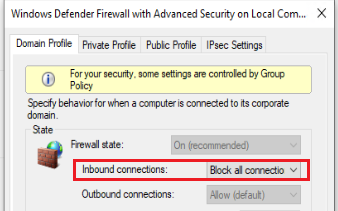
I've configured Windows Firewall to block all incoming connections:
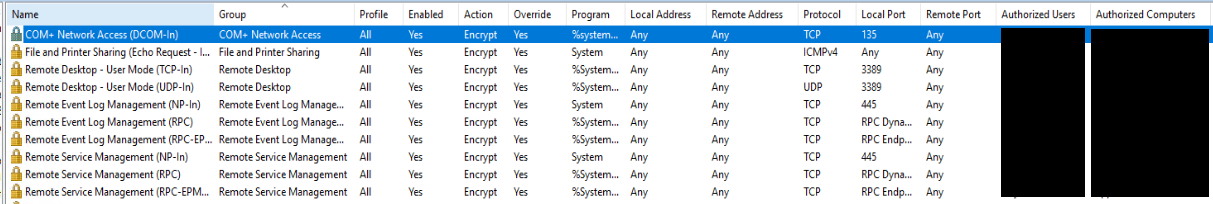
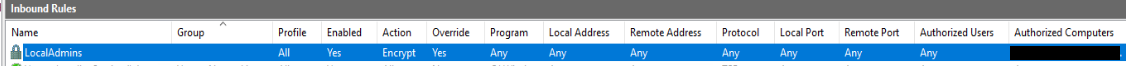
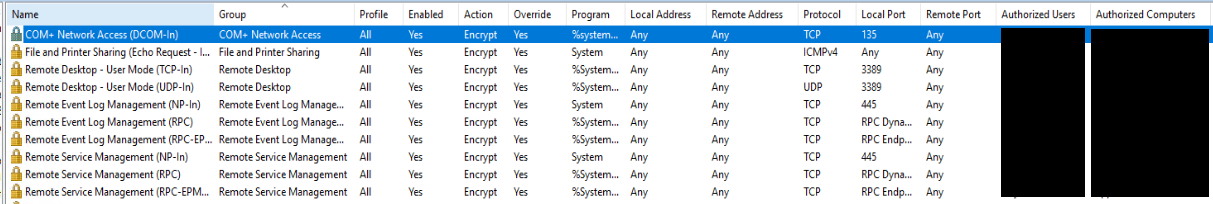
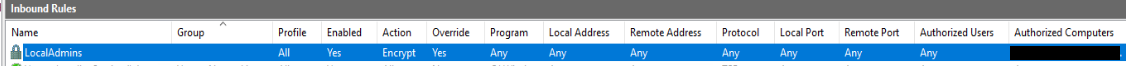
And I've configured various exceptions to allow incoming connections for required services from authorized users and computers:
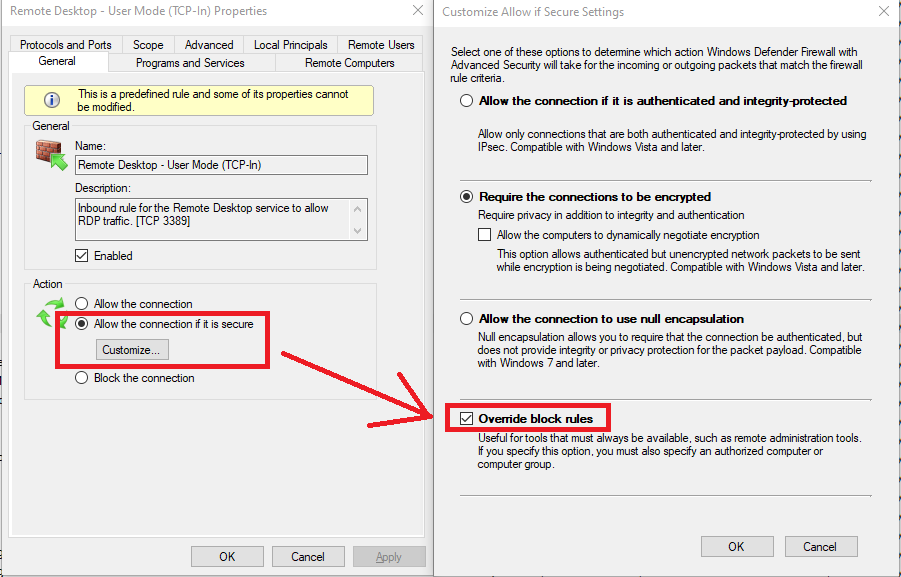
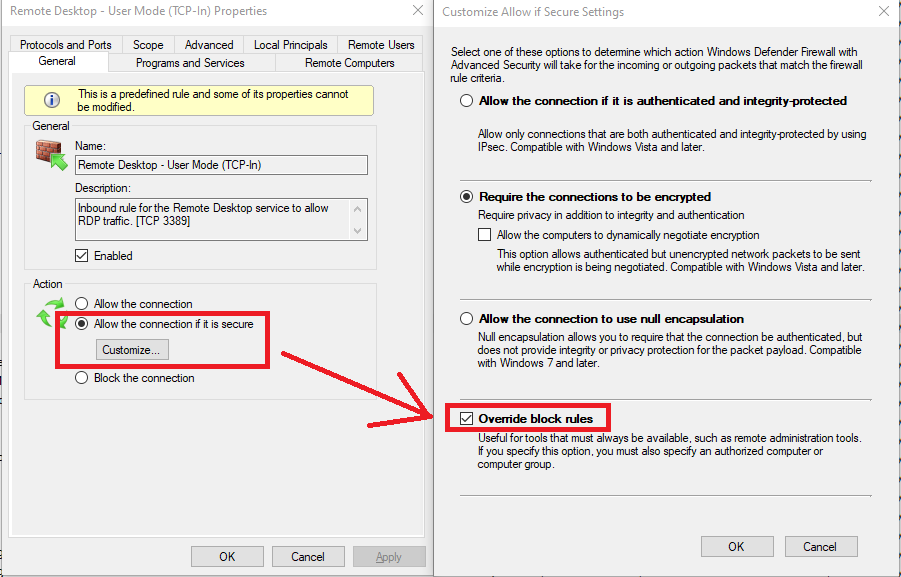
Each of these rules are configured to override the "Block all connections" default firewall setting mentioned earlier:
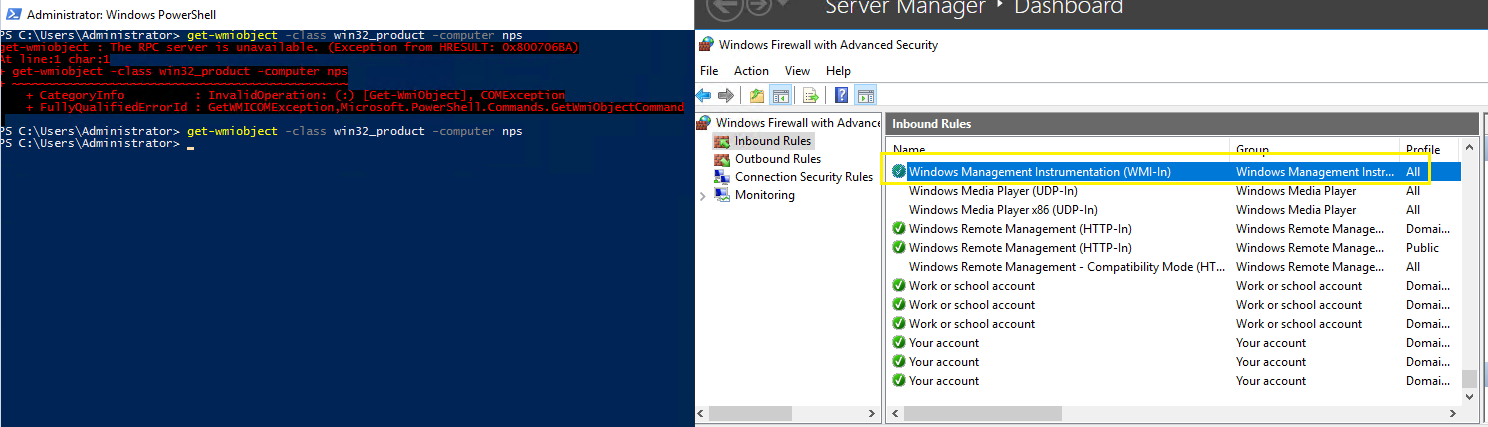
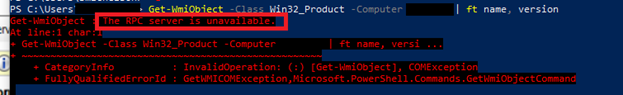
This all works fine with one exception...I cannot get remote PowerShell commands to work in this configuration:
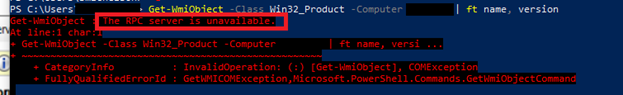
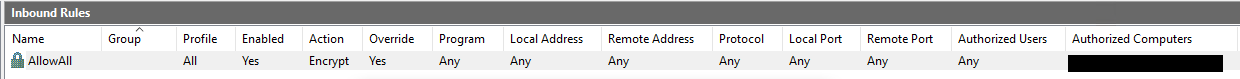
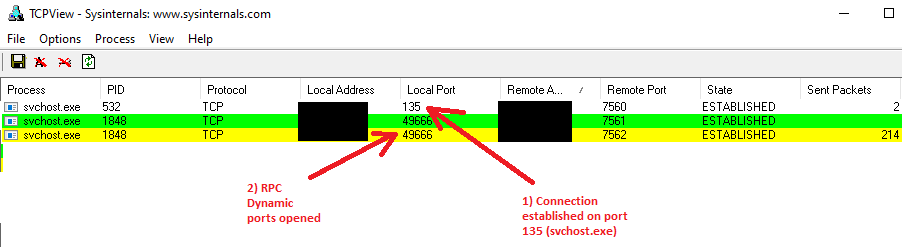
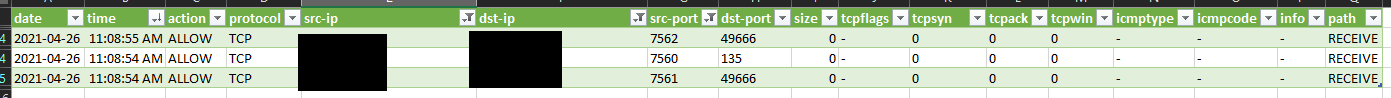
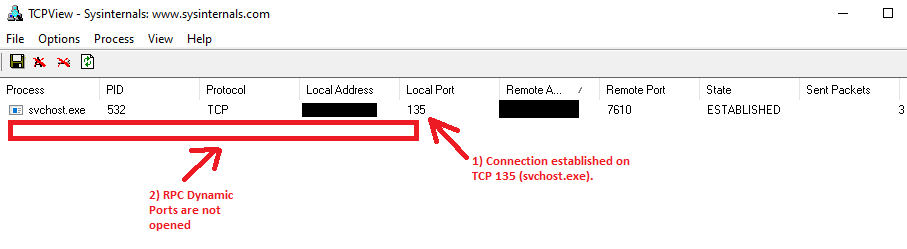
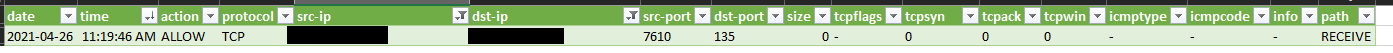
It seems the RPC Dynamic Ports don't open up on the remote PC when running a PowerShell command like "Get-WMIObject". It doesn't matter what kind of exceptions I put in, it never works. I even created an exception that says "let everything in" from my authorized PCs and it still doesn't work:
Other similar inbound rules work fine (Like the default Remove Event Log Management (RPC) rule, which allows inbound connections for %SystemRoot%\System32\svchost.exe% to RPC Dynamic Ports). Something about remote PowerShell is unique and I can't figure out what, any thoughts from the community?