Hm, it is acting strange from my point of view.
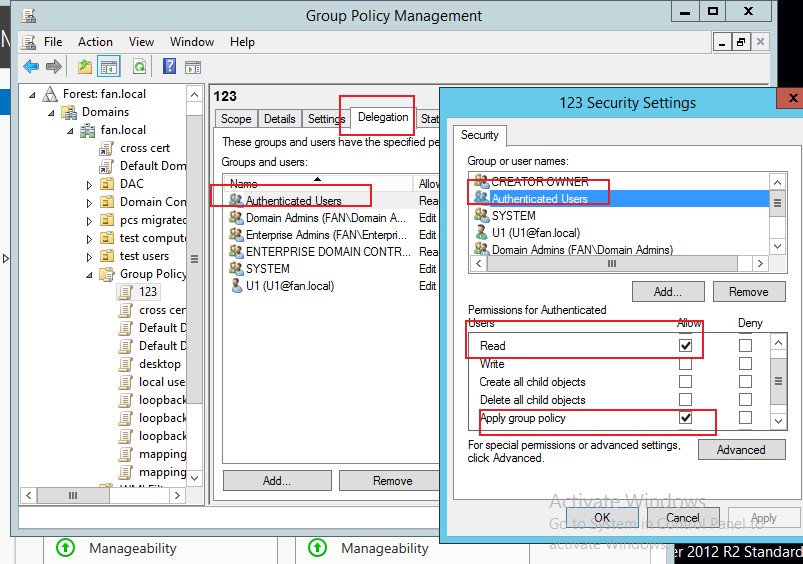
Little info about this policy - it contains User configuration and Computer configuration. Under Computer configuration I have Firewall rules. This policy has Authenticated Users under Scope and under Delegation also Authenticated Users with Read and Apply Group Policy permissions.
Problem:
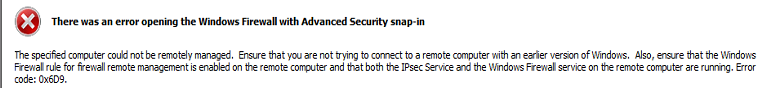
This policy has two settings for firewall rules- one rule is made long time ago and it is applied and second rule is the rule that is not applied. This second rule is created on my computer couple of days ago because I can't create it on DC because this error I mentioned earlier shows.
What is strange is that that second rule is applied on some computers and on other it is not applied. When I run Group Policy Results wizard on computer that has not applied the second rule (only first is applied) it shows me no errors, it just doesn't see configuration for the second rule under Details tab of Group Policy Result wizard.
Also what I have noticed is that for that GPO shows this message "AD / SYSVOL Version Mismatch" on Details tab when I run it on that computer and also I can see under Revision of that policy this mismatch AD (72), SYSVOL (68). Don't know why it shows like this (this computer is Windows 10 and DC is on WS2008R2). Also when I run this wizard od computer (also Windows 10) that successfully applied both rules it doesn't show this mismatch info.
Replication between DC is OK.
Best regards!