I apologize that it's been so long since I've encountered this issue that I may have forgotten some important details. Further, checking my e-mail history, not all of what was done on the institutional AD admin side was ever made clear to me.
As far as I can tell looking at the Active Directory application (which in my case was an instance of HAPI FHIR connecting to PowerBI's FHIR connector), this is what needs to happen:
In Azure AD App Registrations:
- Under "Branding and Properties", set your Home Page URL to, e.g., https://yourapplication.yourdomain.com
- Again under "Branding and Properties," go to Publisher Verification. Hit "Verify a New Domain" and get your domain verified by your institution's AD admin.
- Under "Authentication", set the appropriate callback URLs.
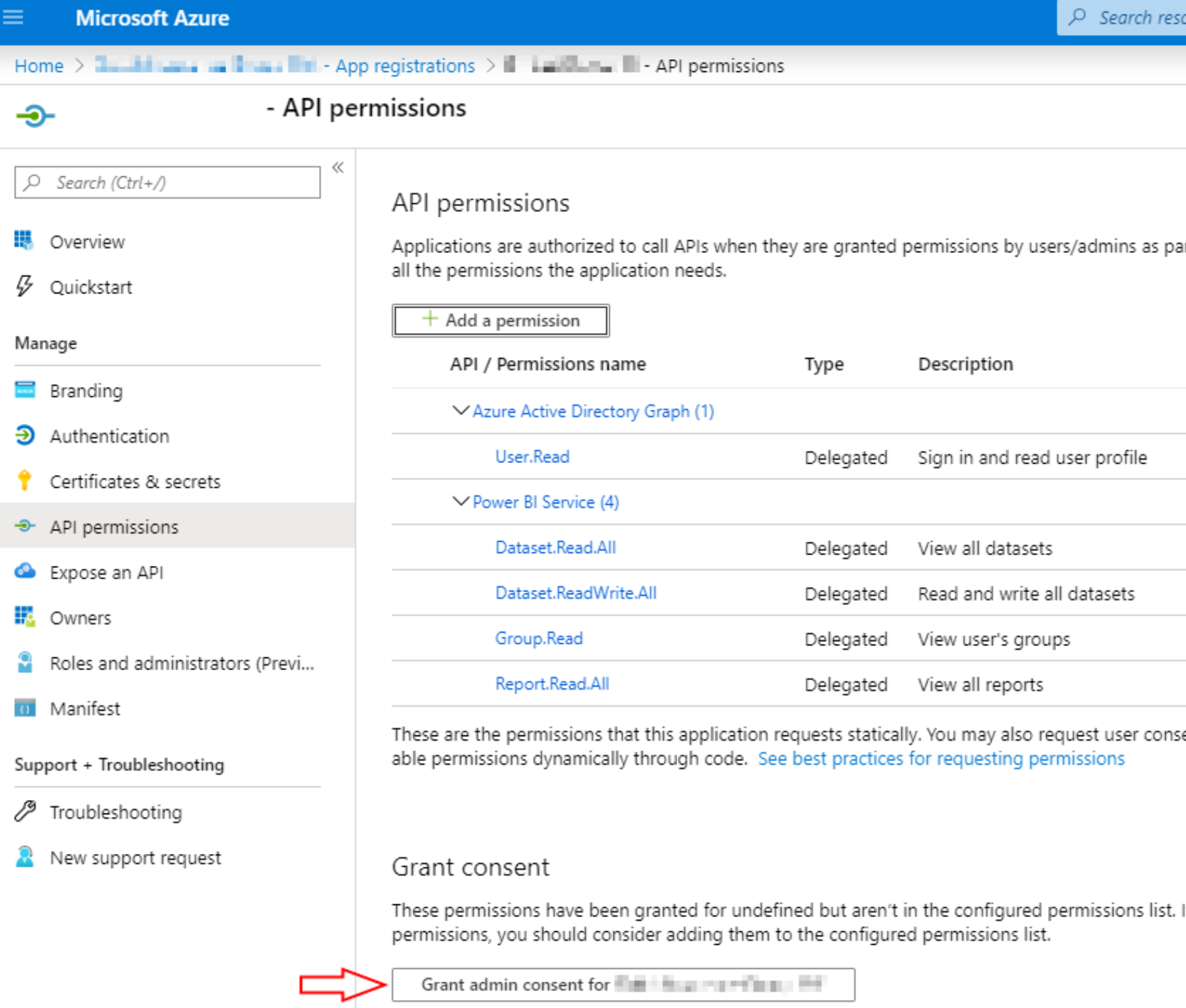
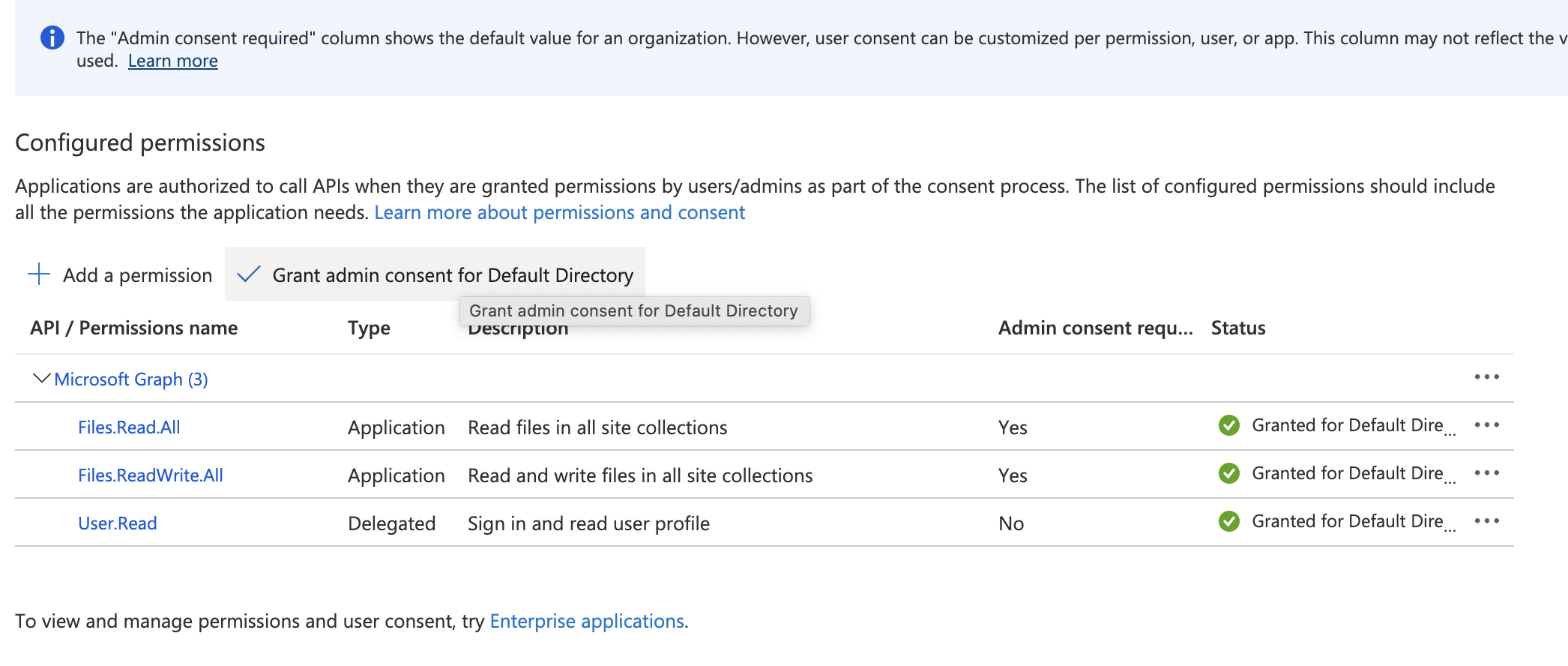
- Under "API Permissions," get admin consent for Microsoft. Graph > Directory.Read.All, email, openid, profile, and User.Read
- Under "Expose an API", get admin consent for https://yourapplication.yourdomain.com/user_impersonation
Not all of that may be strictly necessary, but those are the steps I can reconstruct from my e-mail and is all that is directly visible in my AD application.
If that still doesn't work, there was one additional note I found in the e-mail thread, which was that the AD admin had to consent for "Power Query for Excel" also. I can't find any evidence that this actually happened in Azure Portal, though, so your mileage there may vary.