Hi,
I would like to configure a setting for all laptops in my organization where the Windows Firewall turns on when the laptop is out of our network/cannot reach a domain controller. I thought I could do this via group policy and local security policy, but it doesn't seem like it is working. From my understanding this is how precedence takes place by default: Local → site → Domain → OU → Child OU. I think that I am misunderstanding how this works so any help would really be appreciated.
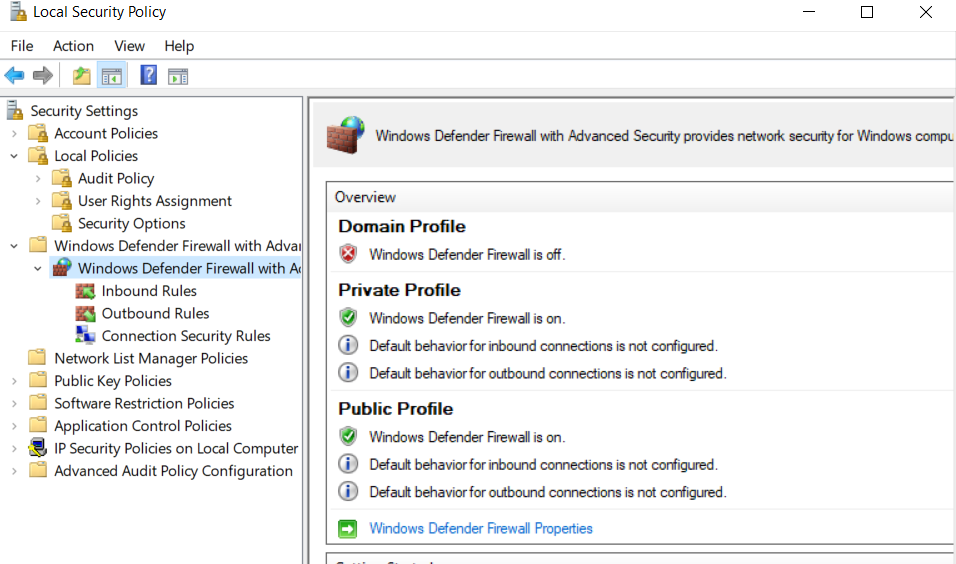
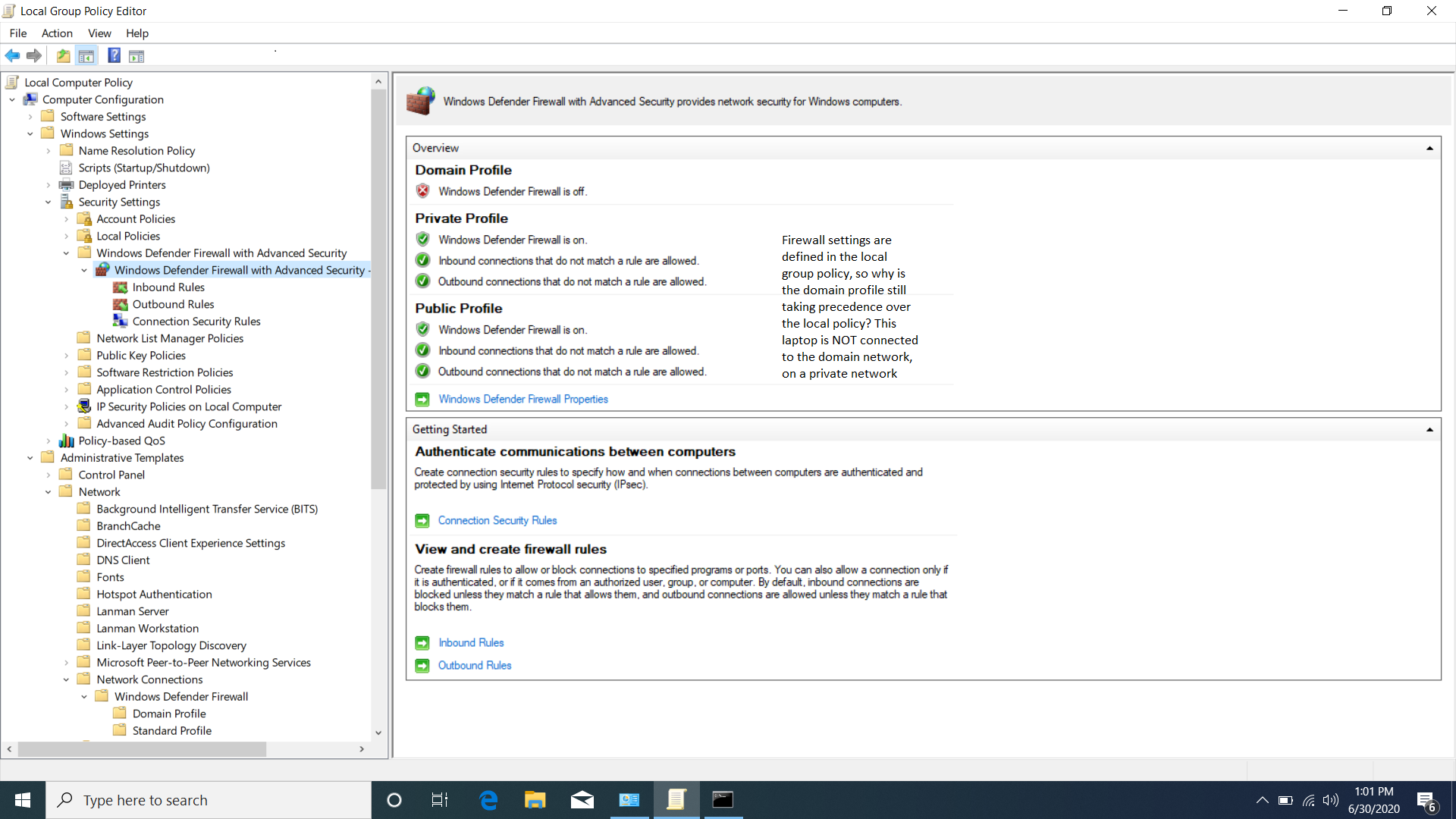
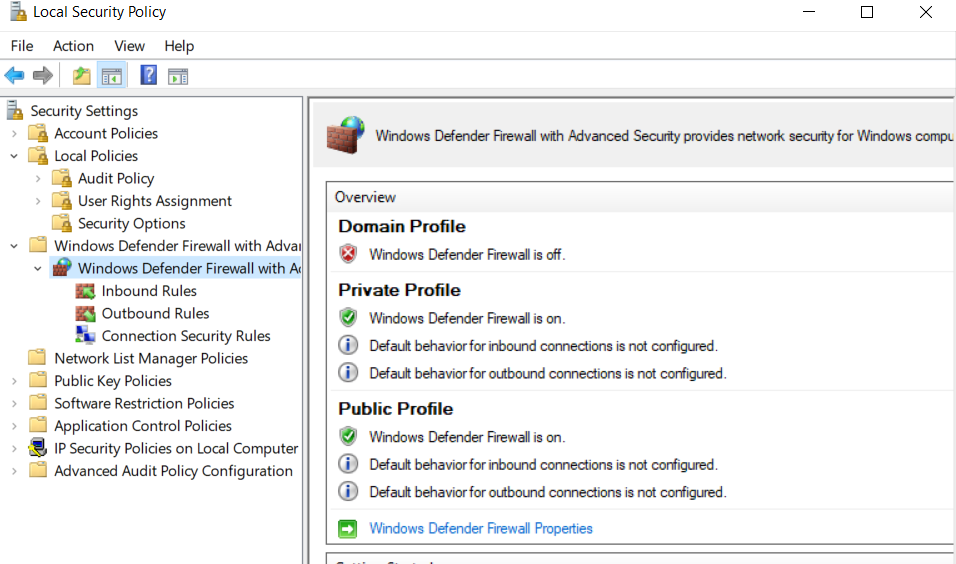
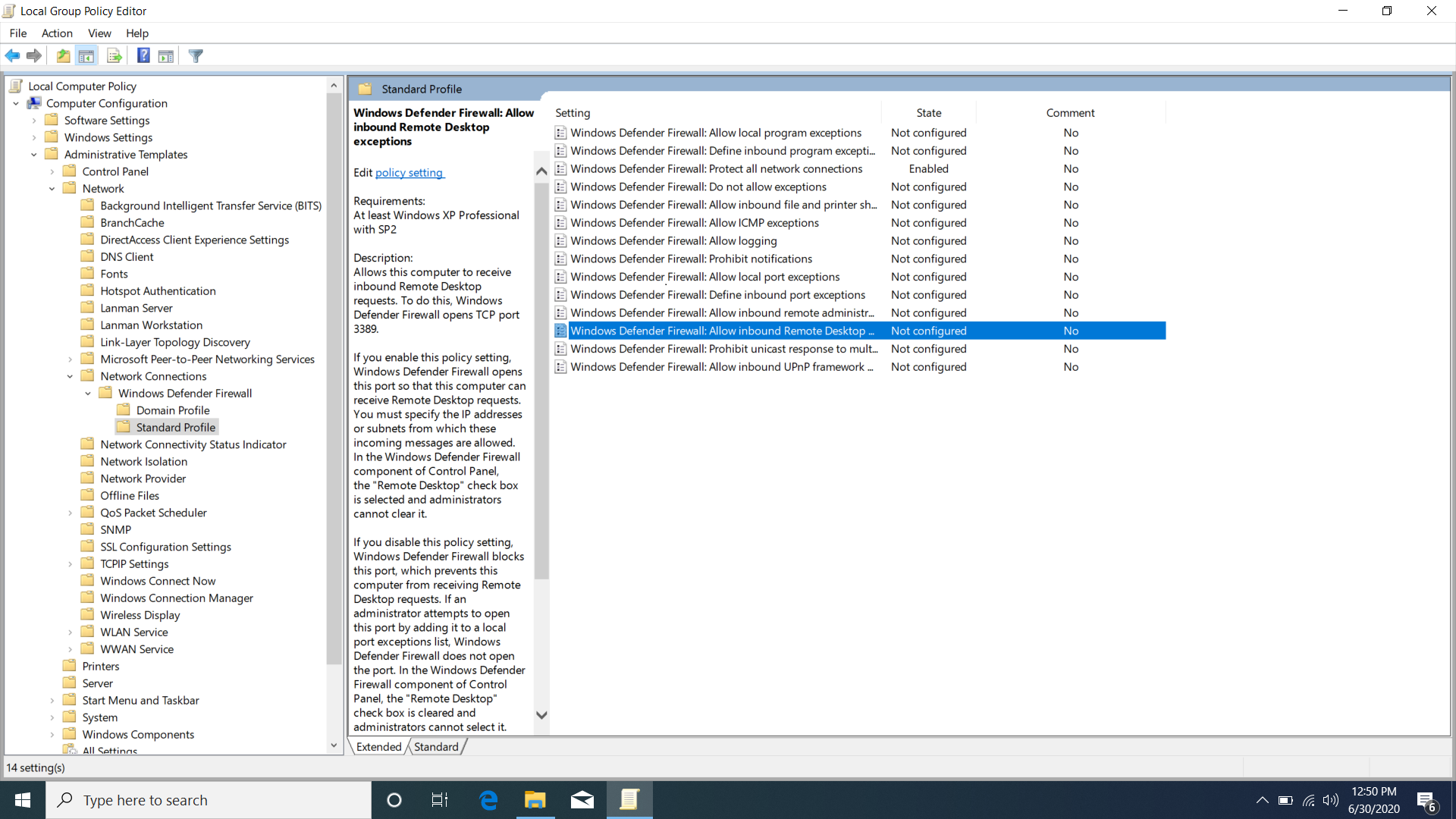
I configured the local security policy as follows, very basic for now when I am testing, just turn on the firewall for private and public profiles:
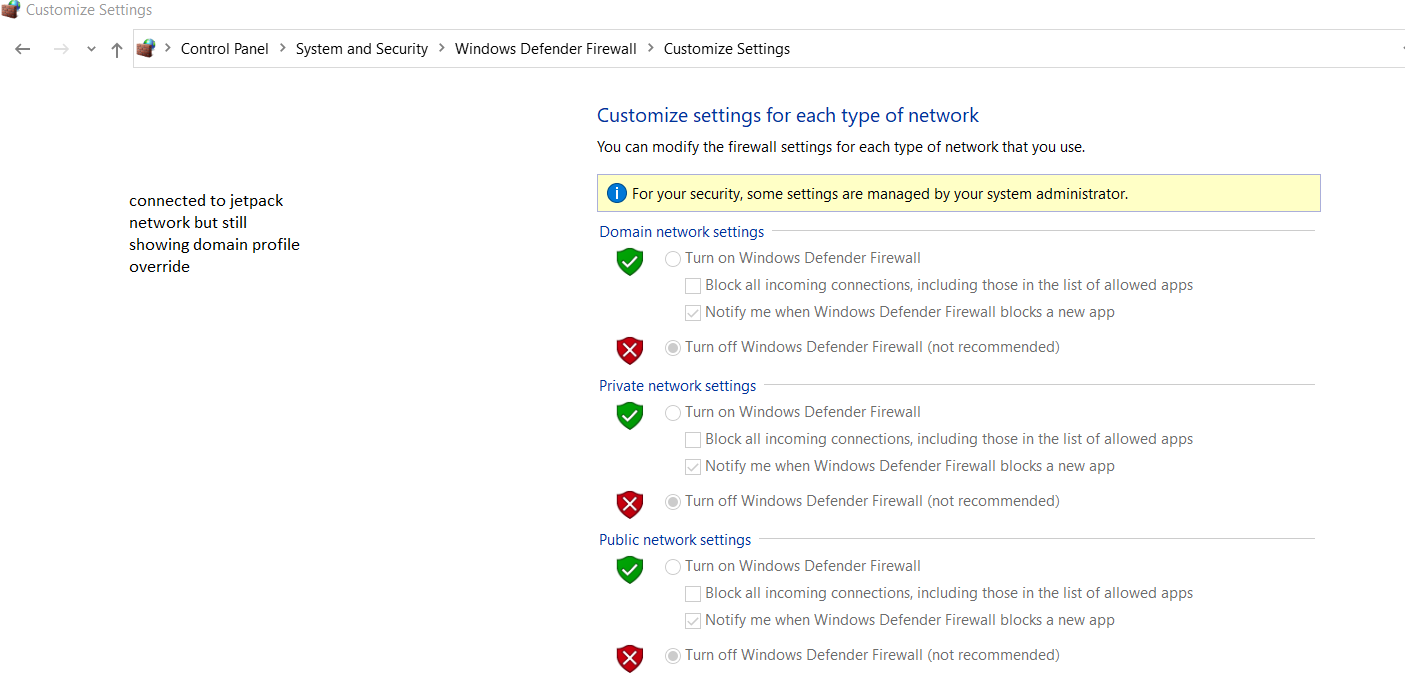
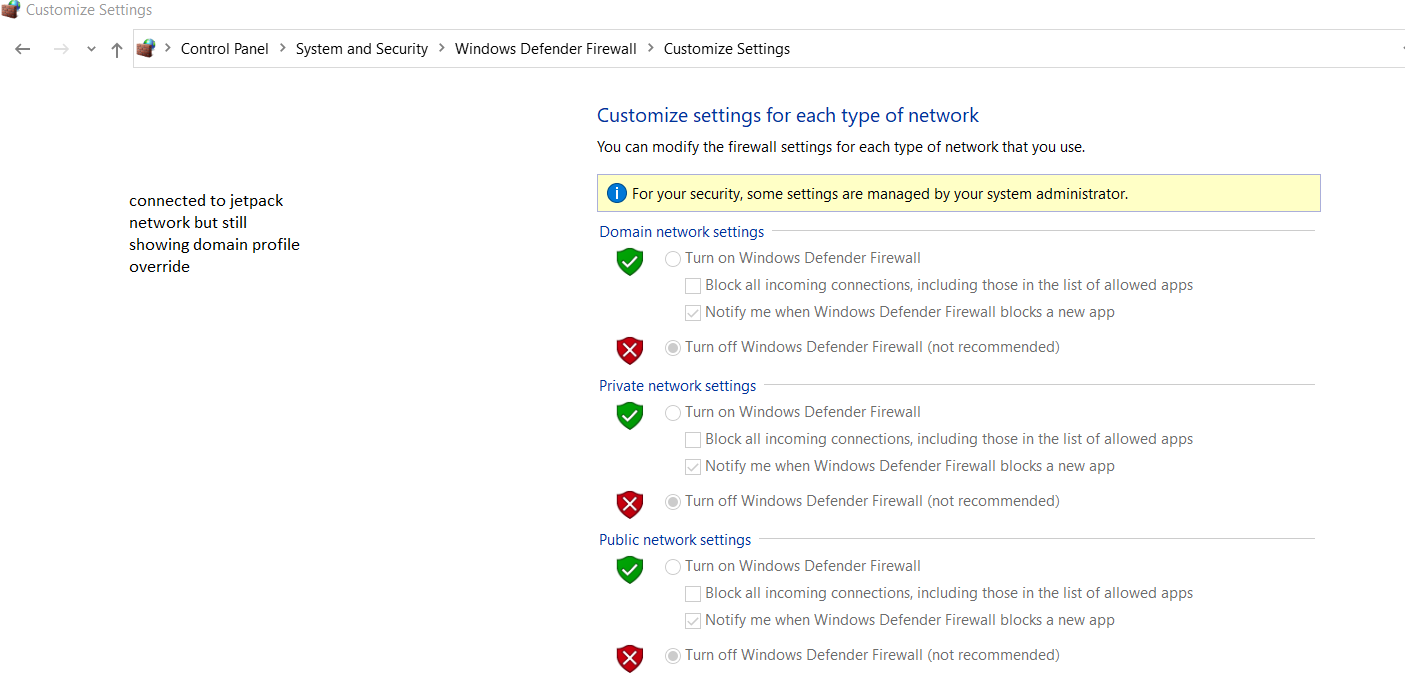
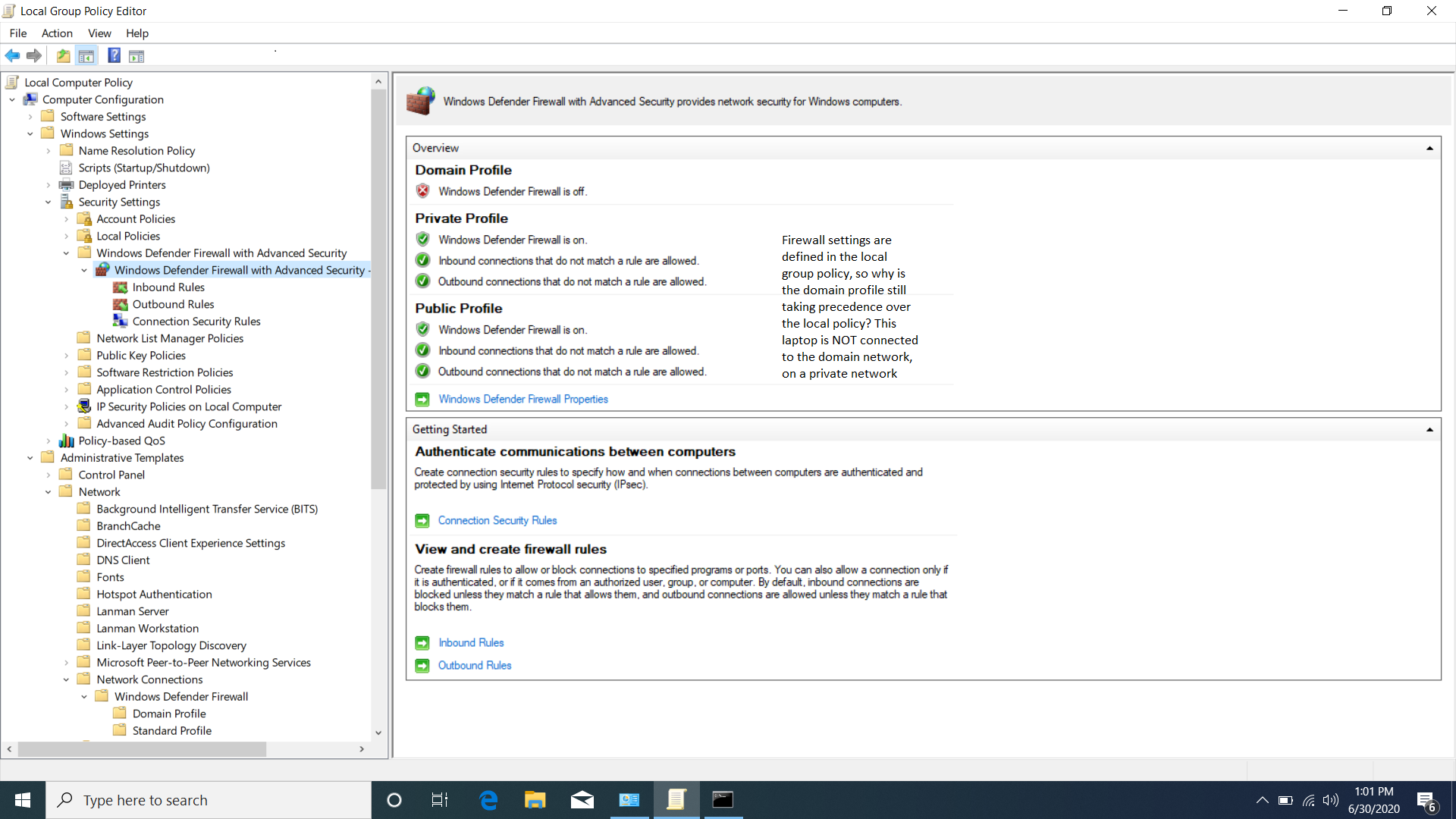
and I thought that it would "switch over" when the machine connected to a private or public network. I am using a jetpack hotspot to test with (external Verizon network) and I can clearly see in control panel that the firewall for all 3 profiles is still turned on, and that it is because of the organization's policy still being applied (domain policy I am assuming?):
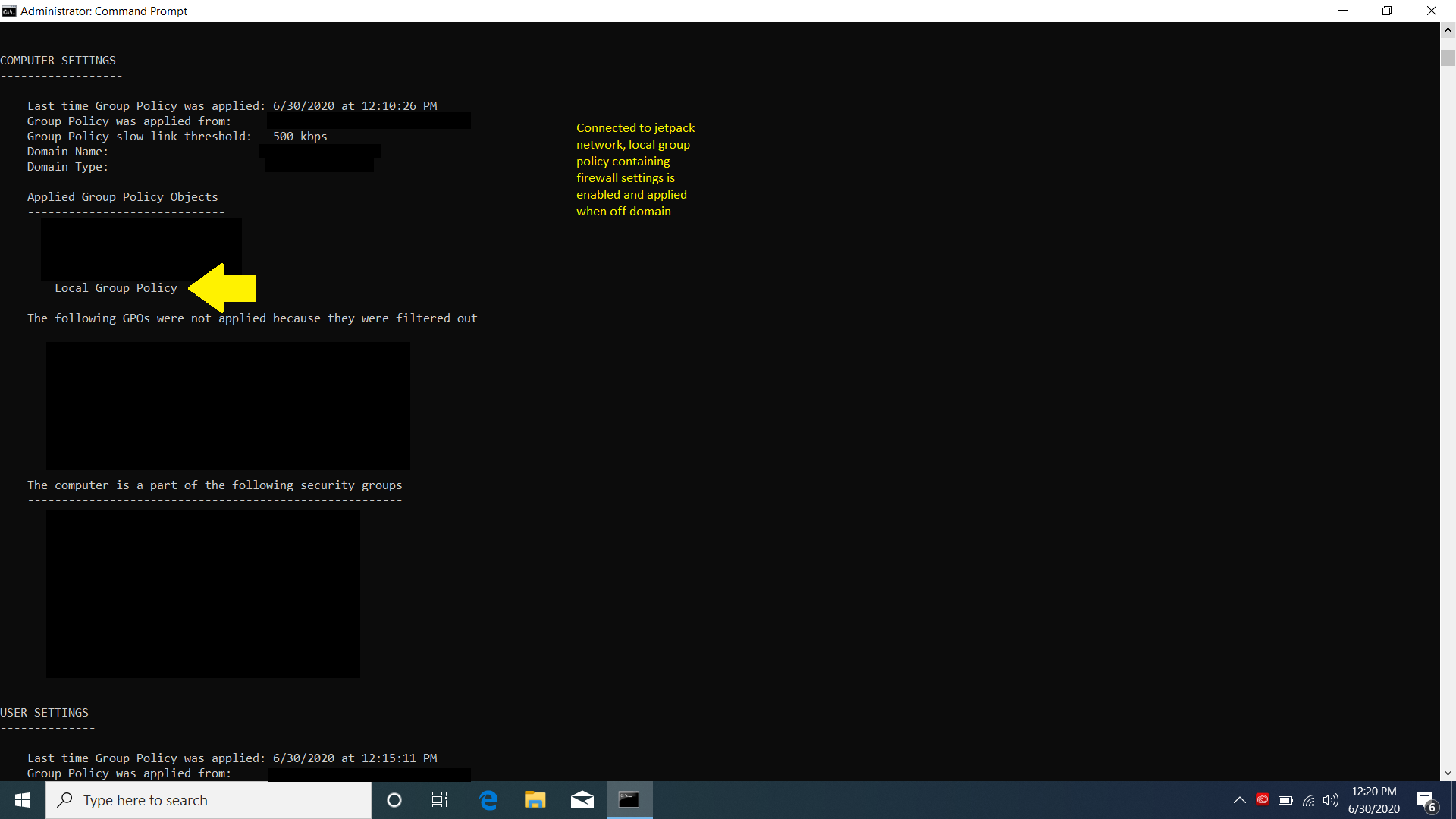
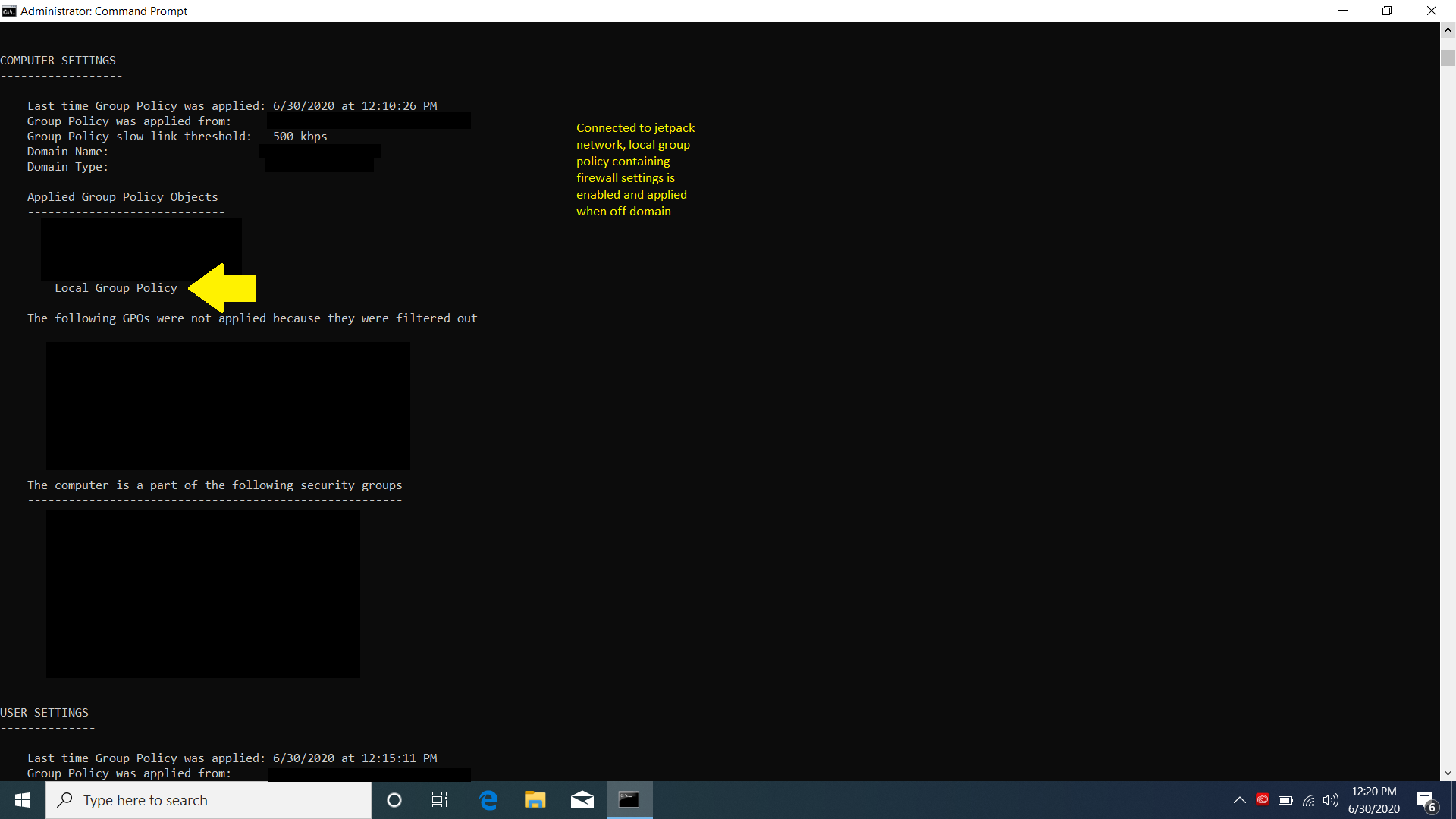
Here the laptop is connected to my jetpack hotspot (cannot see domain controllers or our network at all when it's connected to this hotspot), I see a local policy is being applied via gpresult, note I did not remove this from the domain rather I connected it to a private network with the jetpack hotspot:
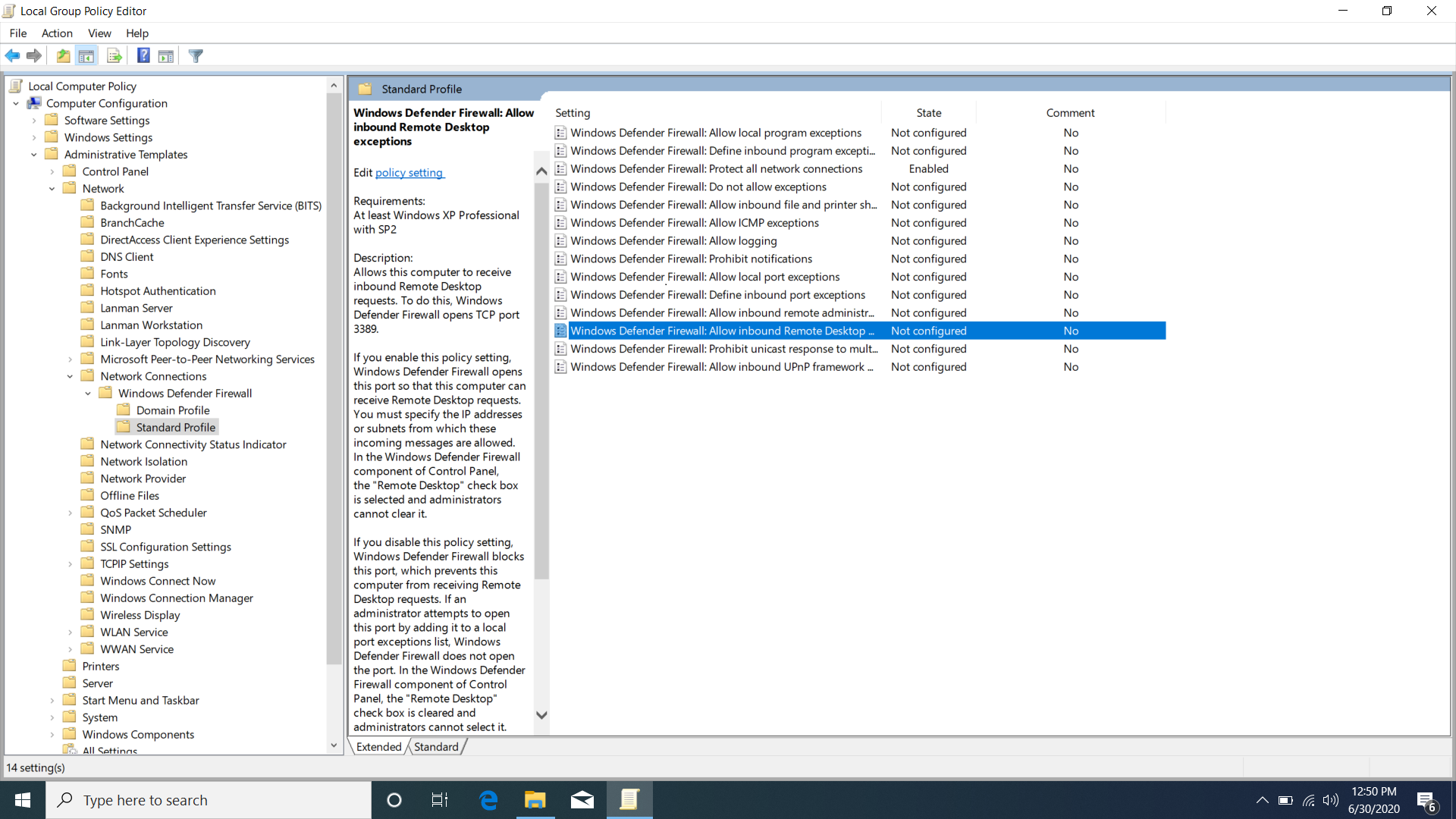
This is how I defined the local policy:
Maybe it is just my understanding that is incorrect and this actually cannot work the way that I want it to.
I also tested one more thing - I removed the laptop from the domain entirely and put it on a workgroup to see what would happen. Once I rebooted and checked the firewalls again, I noticed that they turned on as they are supposed to.
I think that this is what is happening: When the laptop is enrolled in our domain & on a private network where it cannot communicate w/ our DCs, the domain profile still overrides the local security settings even when it's not connected to our domain network (when it's connected to any other private/public network). This makes sense from a security standpoint - you wouldn't want a user to walk out of your organization and be able to configure these local polices (hence protected local admin account that is not given to users) nor have the fine-grained policies of your domain disappear. I think I am starting to understand this but I would love to read more resources and opinions from anyone with some experience. I also am looking into Microsoft's DirectAccess as we have valid enterprise licenses for Windows 10 and Server 2012 R2/2016/2019. I looked into a VPN client of some sort, but I think I may run into authentication issues doing that and I kind of do not want these laptops having a back-end way into my domain network. My hope and end goal is to add extra layers of security besides anti-virus to protect and manage mobile devices when they are not within our network. Thank you so much!