Hi @Christophe-2684
I recommend trying the troubleshooting MFA NPS extension article and also checking the NPS Health ScripAzure-MFA-NPS-Extension-648de6bbt. NPS extension only performs secondary authentication for Radius Requests which have the "Access Accept" state. You may need to configure the NPS Extension again (though I know you mentioned you already did this).
As stated in the troubleshooting documentation, the DLL error can happen due to the following possible issues:
- The wrong tenant ID was provided while configuring the NPS extension .
- The user for which NPS rejects the requests have unicode characters in their passwords. The -
NPS does not support Unicode passwords and it can fail for that reason Try changing user's password . We have a product backlog item open for this.
- Timeout observed within any firewall that you may have within your network.
- The NPS server is not set to ignore dial-in tab access permissions set on user objects in Active Directory.
- Verify that your firewalls are open bidirectionally for traffic to and from .
During my own setup of this extension I have received this error when the request was timing too soon, when the latest version of the extension was not installed, and when there were old certificates on the server that needed to be removed.
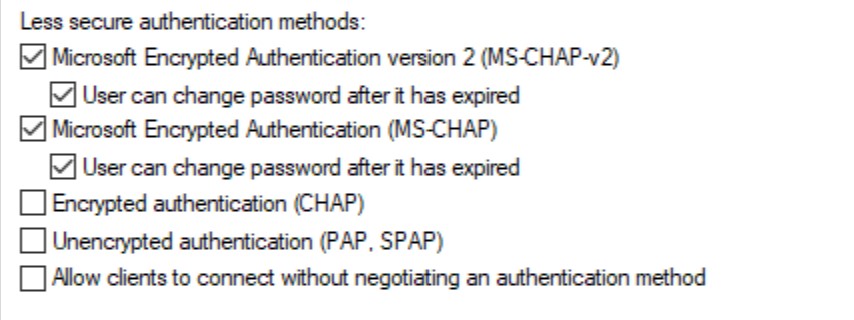
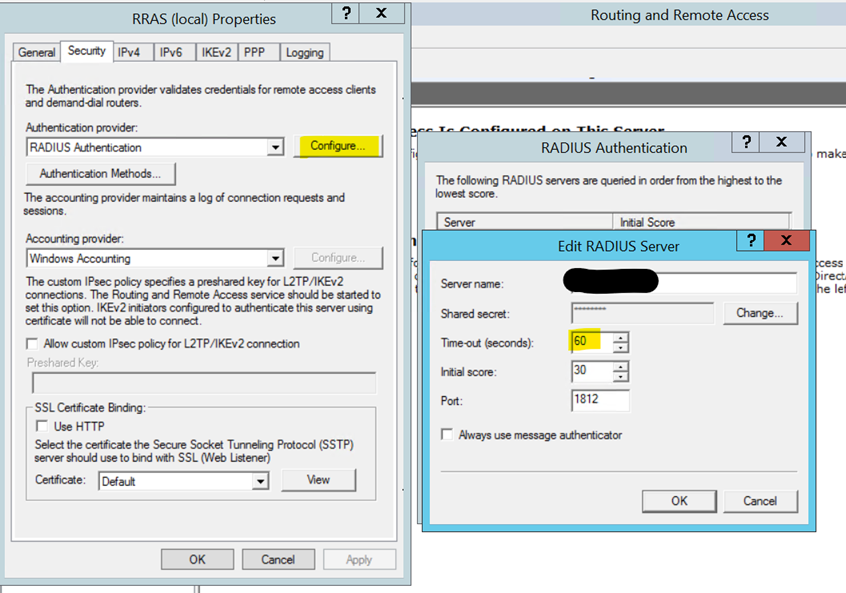
If the request is timing out too soon, make sure that it's set to at least 60 seconds to give enough time for the request to succeed. 
Make sure also you have the latest version of the extension installed. Older versions sometimes threw that DLL error. https://learn.microsoft.com/en-us/azure/active-directory/authentication/howto-mfa-nps-extension-rdg#install-the-nps-extension
Finally, make sure that there aren't any duplicate or old certificates on the server.
You can check for old certificates using:
Get-MsolServicePrincipalCredential -AppPrincipalId "app-principal-id" -ReturnKeyValues 1
Then you can remove duplicates using:
Remove-MsolServicePrincipalCredential -AppPrincipalId "app-principal-id" -KeyIds <enterkeyidhere>
See also the related discussions: https://www.reddit.com/r/AZURE/comments/a0qp5p/azure_mfa_nps_extension_for_rdgateway/
https://learn.microsoft.com/en-us/answers/questions/36056/latency-for-getting-azure-mfa-through-nps-reason-c.html
https://github.com/MicrosoftDocs/azure-docs/issues/55499