Hello @MaheshMahi-7462 ,
An account created only in azure AD would not be able to authenticate as far as I know. NTFS level permission for a account related to the account being able to use Kerberos/NTLM for access but the Azure AD account belongs to AAD identity system which does not directly support legacy auth protocols like Kerberos/NTLM. However you can use Azure file shares which uses Azure file sync to sync the files to azure. You can enable the on-prem account authentication on Azure file share provided the account is synced to azure. You can read more on the article on-premises Active Directory Domain Services authentication over SMB for Azure file shares . Azure AD and On-prem AD are different kind of authentication systems. The way they store user objects is similar but the protocols that they support are different because Azure AD is designed with modern application in mind which operate over the web hence oAuth and SAML are the protocols it supports but on-premise system does not support the same.
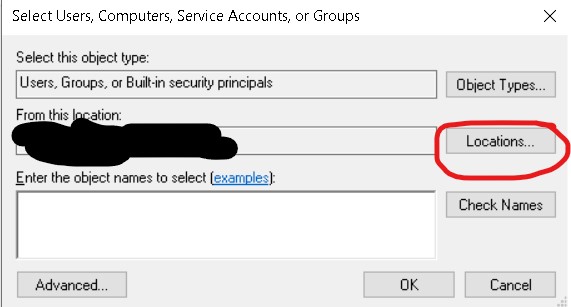
In any case when you would try to edit NTFS permission for an object , you would not see the option to select from Non-Active directory locations. the locations button will only bring up the trusted Active directory forests so you will not be able to add any azure AD only created account as the system has no way to search them .
I am not sure of the use case you have but I believe the details in this answer would give you some clarity . I don't think you can achieve this on a windows server which is hybrid joined. I have not tested the azure AD joined machine for this scenario but as far as my knowledge about on-prem AD and SMD shares go I do not think it will work. Hope the information is useful for you . In case the information in this post helps , please do accept this post as answer so that it could help other members of the community . Should you have any further queries , please feel free to let us know and we will be happy to help .
Thank you.
