Hello @GS-1345 ,
Apologies for the delay in response.
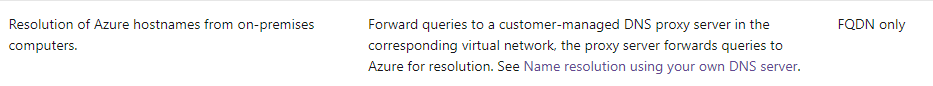
1) Ping from device to Azure VM using FQDN does not work:
In order to resolve Azure hostnames from on-premises computers, you need to forward queries to your own managed DNS proxy server in the corresponding virtual network, so that the proxy server can forward queries to Azure for resolution.
Refer : https://learn.microsoft.com/en-us/azure/virtual-network/virtual-networks-name-resolution-for-vms-and-role-instances
2) When VPN P2S is connected, you can not access to shares in remote VNet:
As mentioned here, when the connection is initiated, the VPN client adds the session credentials and the failure occurs. After the connection is established, the client is forced to use the cache credentials for Kerberos authentication. To work around the problem, disable the caching of domain credentials from the following registry subkey:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa\DisableDomainCreds - Set the value to 1
Kindly let us know if the above helps or you need further assistance on this issue.
Please "Accept the answer" if the information helped you. This will help us and others in the community as well.

