Azure AD Account perpetually linked to non-existent local AD domain
My account was born in AAD many years ago. Sometime ago I acquired a license to Windows Server and decided to work with some things on-prem rather than in the cloud. I connected to my AAD with Azure AD Connect at the time, and my accounts, I believe, successfully synced. Due to my own naivete I did not offboard the Windows Server VM before I repurposed it, and as a result, I lost access to the on-prem copy of the directory. I believe I may have opted to pseudo-convert my cloud account to be managed on-prem, though it still exists in Azure AD and the identity issuer is my .onmicrosoft.com domain / it is not directory synced.
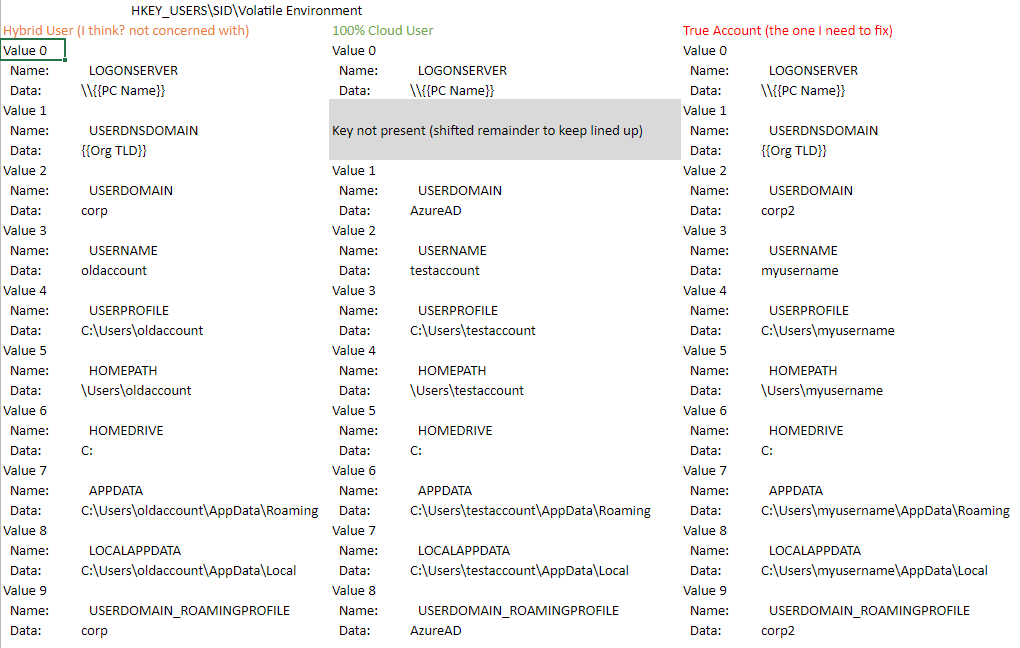
My issue which I have tried to solve a number of ways rather than ask for help out of embarassment is when logging into any physical PC with my AAD account, it does successfully link up to my cloud AD account, but there is this ghost remnant of the on-prem directory in front of my username. Effectively all of my local activity is being linked to "ghost\username" where ghost is the domain of long ago. This has made for some issues because the ghost domain does not exist and I can see in event viewer that this is the "domain" being indicated for my activities, as opposed to my proper Azure AD domain, or "AzureAD" as I think it may alternatively display.
Is there any way to correct this issue? I have created Windows VM's and linked them to my org account and they are also automatically displaying this "ghost" domain with my username. The bulk of the impact may be visual only but I do think it is causing some unnecessary errors as well.