Hello @HASSAN BIN NASIR DAR ,
Welcome to Microsoft Q&A Platform. Thank you for reaching out & hope you are doing well.
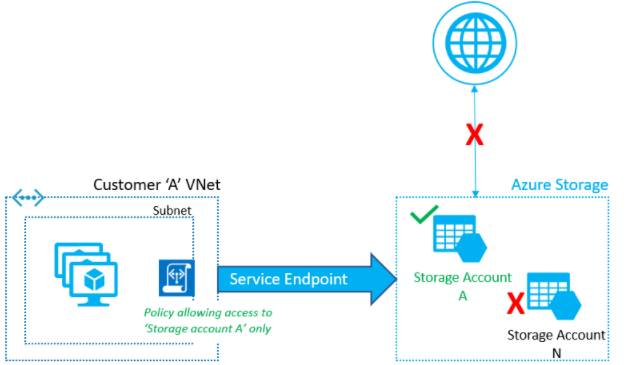
Yes, the statement you provided is true. However, there is a feature in Service endpoints to restrict virtual network traffic to specific Azure Storage accounts. You can use Virtual Network Service endpoint policies which allows you to filter egress virtual network traffic to Azure Storage accounts over service endpoint, and allow data exfiltration to only specific Azure Storage accounts. Endpoint policies provide granular access control for virtual network traffic to Azure Storage when connecting over service endpoint.
Endpoint policy allows you to add specific Azure Storage accounts to allow list, using the resourceID format. You can restrict access to
- all storage accounts in a subscription
E.g. /subscriptions/subscriptionId
2) all storage accounts in a resource group
E.g. subscriptions/subscriptionId/resourceGroups/resourceGroupName
3) an individual storage account by listing the corresponding Azure Resource Manager resourceId. This covers traffic to blobs, tables, queues, files and Azure Data Lake Storage Gen2.
E.g. /subscriptions/subscriptionId/resourceGroups/resourceGroupName/providers/Microsoft.Storage/storageAccounts/storageAccountName
By default, if no policies are attached to a subnet with endpoints, you can access all storage accounts in the service. Once a policy is configured on that subnet, only the resources specified in the policy can be accessed from compute instances in that subnet. Access to all other storage accounts will be denied.
Please refer the following doc for more information : https://learn.microsoft.com/en-us/azure/virtual-network/virtual-network-service-endpoint-policies-overview
Kindly let us know if the above helps or you need further assistance on this issue.
Please "Accept the answer" below if the information helped you. This will help us and others in the community as well.
