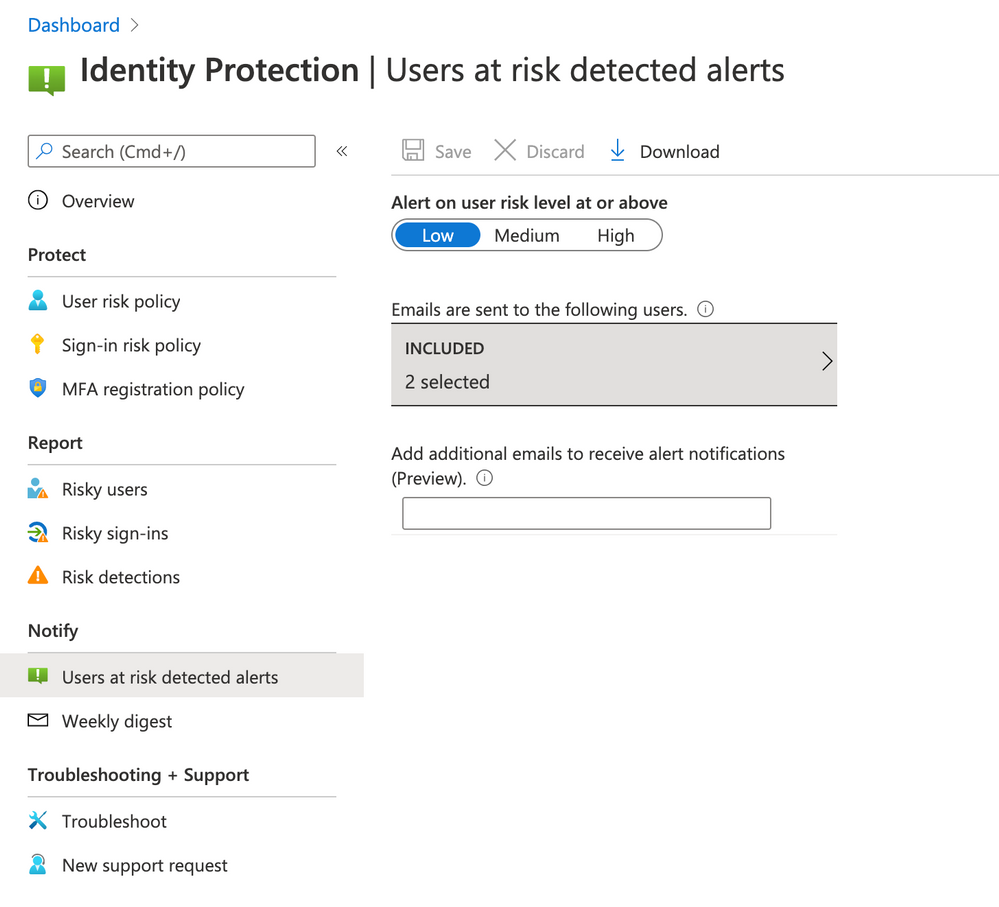
While there isn't anything built in just for risky sign-ins alone, you can set up either alerts based on user risk levels or alerts that come in a weekly digest email (which include risky sign-ins). To configure alerts based on user risk levels, you can go to Azure Active Directory > Security > Identity Protection > Users at risk detected alerts. These will be triggered based on the risk level, which is set to "high" by default.
Note that you do need a P2 Premium license to use this feature.
You can also set up weekly digest emails. These emails include the following:
New risky users detected
New risky sign-ins detected (in real time)
Links to the related reports in Identity Protection
You can do this under Azure Active Directory > Security > Identity Protection > Weekly digest.
There is also this sample powershell script you can run for identifying risky users and eliminating false positives: https://github.com/AzureAD/IdentityProtectionTools
Let me know if this helps.