@@IamCoder , thank you for your question. We regret the delayed response and any inconvenience it may have caused.
Some recommendations have parameters that must be customized via Azure Policy to use them effectively. For example, to benefit from the recommendation Container images should be deployed only from trusted registries, you'll have to define your trusted registries.
If you don't enter the necessary parameters for the recommendations that require configuration, your workloads will be shown as unhealthy.
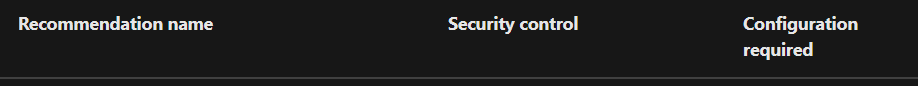
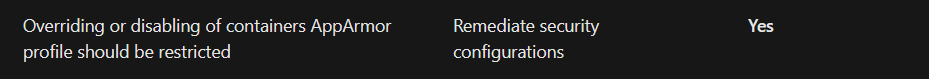
By default the Policy definition for Kubernetes cluster containers should only use allowed AppArmor profiles has an empty list specified for allowedProfiles:
...
"allowedProfiles": {
"type": "Array",
"metadata": {
"displayName": "Allowed AppArmor profiles",
"description": "The list of AppArmor profiles that containers are allowed to use. E.g. 'runtime/default;docker/default'. Provide empty list as input to block everything."
},
"defaultValue": []
},
...
So, if you are using the profile runtime/default you have to modify the security policy to add the same in the allowedProfiles array.
----------
Hope this helps.
Please "Accept as Answer" if it helped, so that it can help others in the community looking for help on similar topics.