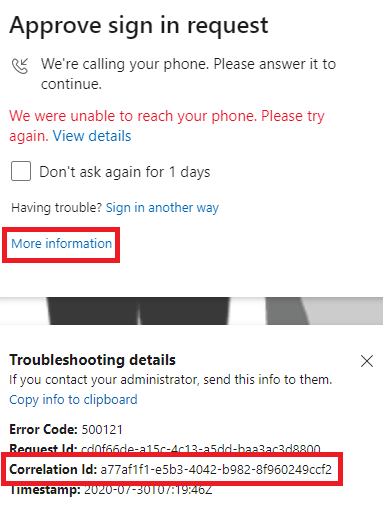
Hi @pmartynas Thanks for your response. These endpoints are by default secured with MFA and you will always be prompted for proofup (2nd factor) if you try to set ADDITIONAL SECURITY VERIFICATION via https://myaccount.microsoft.com/?ref=MeControl or https://aka.ms/mfasetup, even when MFA is not enforced on the user account. This behavior can NOT be changed.
This is to prevent any malicious user from setting his phone number to be used as second factor of authentication if he somehow managed to get access to a user account with first factor of authentication.
-----------------------------------------------------------------------------------------------------------
Please "Accept the answer" if the information helped you. This will help us and others in the community as well.