Hello @ LarsAldersAragornICTDienstverlenin-5144,
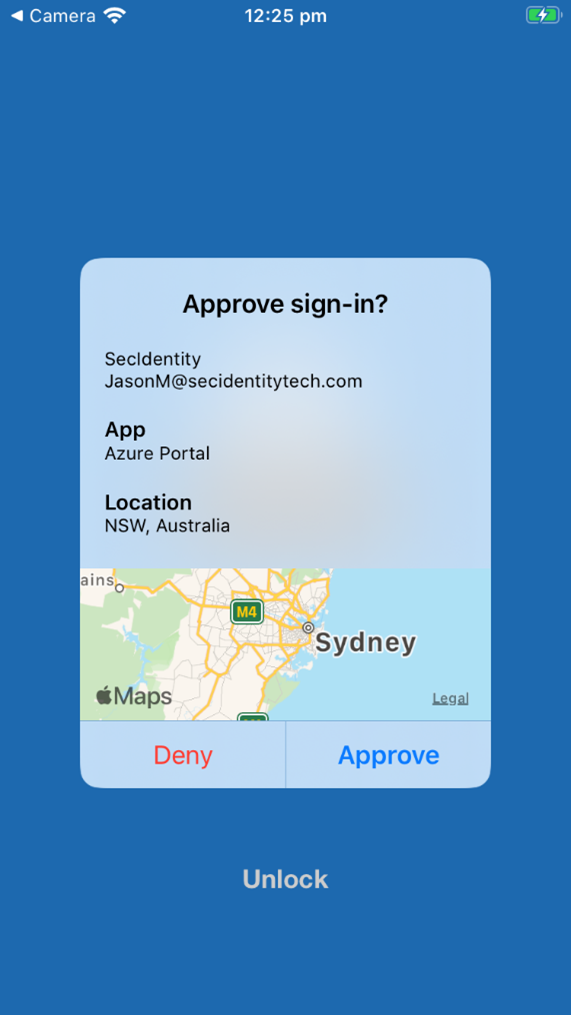
Unfortunately, additional context to Azure MFA Network Policy Server (NPS) extension is not supported since its technically not possible to do so because the RADIUS server validates users' primary authentication using the legacy protocol and initiates secondary authentication through the NPS extension on the user's behalf, thus there is no user-rich context exchanged, such as location.
Please refer to FAQ of additional context in multifactor authentication (MFA) notifications (Preview): https://learn.microsoft.com/en-us/azure/active-directory/authentication/how-to-mfa-additional-context#known-issues
-----
Please "Accept the answer" if the information helped you. This will help us and others in the community as well.