Hello @Belan Marek ,
Thanks for reaching out.
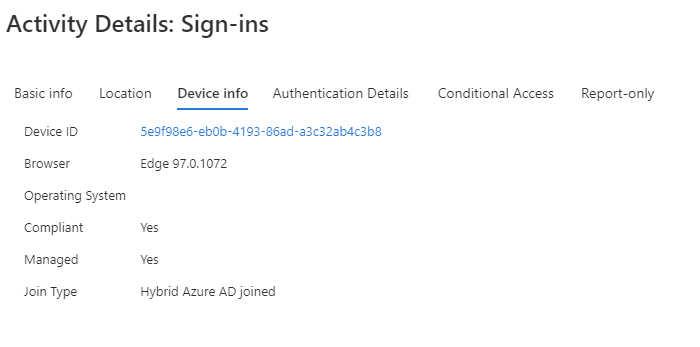
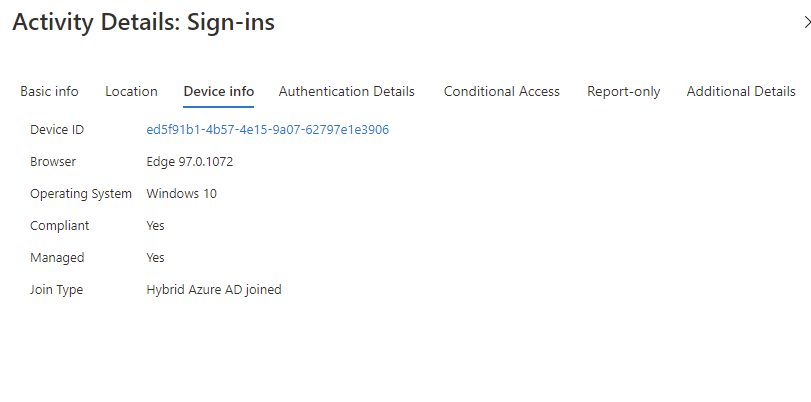
Azure Active Directory is the "consumer" of the data. It is up to the Application to offer information about the operating system, etc. Unfortunately, this appears to be a known limitation of accessing Azure cloud shell via Windows Terminal, since we can not see any operating system information.
Here is another not supported scenario with CloudShell when using the device-code OAuth flow, the require managed device grant control or a device state condition which aren’t supported.
if you would like to exclude CloudShell in these scenarios from being evaluated by the Conditional Access policy already in place (Include All Apps), I would suggest excluding "Microsoft Azure Management - APP ID: 797f4846-ba00-4fd7-ba43-dac1f8f63013" from this policy. For further information about Microsoft Azure Management, refer. Please be aware of that, not only windows terminal app, but also the other apps that rely on to Microsoft Azure Management will be affected as well.
Additionally, if you do not wish to exclude the whole app, you may try excluding certain individuals or groups. Alternatively, you may utilize Grant Access: Require Multi-Factor Authentication with this policy, users running untrusted operating systems must complete MFA before accessing cloud resources.
I fully understand that the current behavior of Windows Terminal + Azure Cloud Shell with CA required operating system may not satisfy your security concerns; therefore, please feel free to provide feedback via the following link: https://feedback.azure.com/d365community/forum/4518e8d7-0925-ec11-b6e6-000d3a4f0858.
Hope this helps.
-----
Please "Accept the answer" if the information helped you. This will help us and others in the community as well.