Hi @Glenn Van Rymenant .
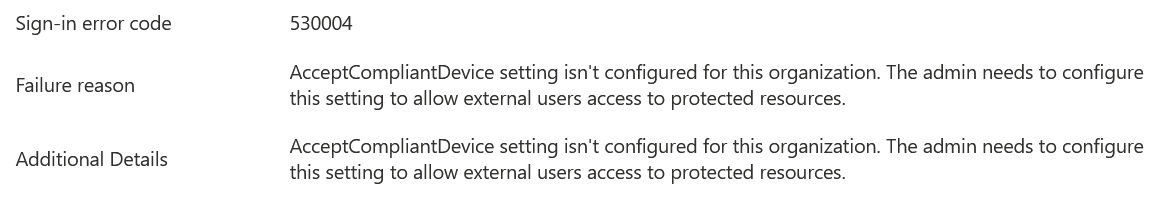
I understand the users are unable to access the tenant because they are receiving the error, "AcceptCompliantDevice setting isn't configured."
This can happen if you have a conditional access policy that requires device ID (approved client app . So, to use this feature, the user needs to have the ID registered in your directory.
The Conditional Access grant controls such as "Require approved client apps" and "Require app protection policies" need the device to be registered in the tenant. These controls can only be applied to iOS and Android devices. However, neither of these controls can be applied to B2B guest users if the user’s device is already being managed by another organization. A mobile device cannot be registered in more than one tenant at a time. If the mobile device is managed by another organization, the user will be blocked.
If this is the case, you can may need to remove the user from the Conditional Access policy.
Let me know if this helps at all.
Additional reading: Conditional Access Mobile Application Management Policies
Thanks,
Marilee