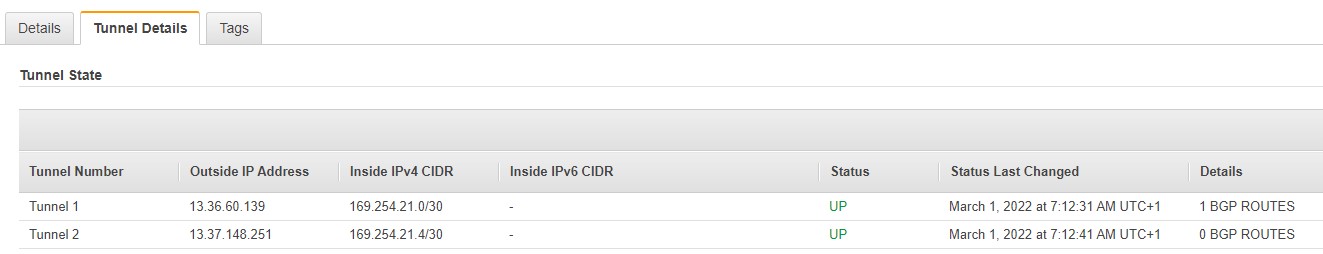
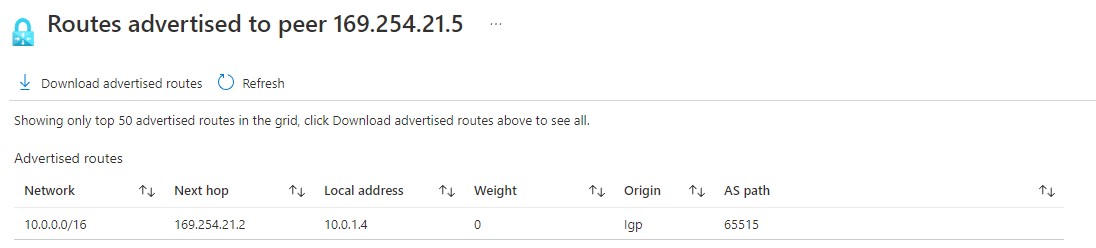
@Miroslav_ngena Thank you for reaching out to Microsoft Q&A. I understand that you are having issues with S2S VPN connection between Azure and AWS where for 2 of the redundant connections, Tunnel 2 shows 0 BGP routes.
This seems like a configuration issue to me where the BGP peer addresses may not have been configured correctly. Can you please re-check the same especially this part: https://learn.microsoft.com/en-us/azure/vpn-gateway/vpn-gateway-howto-aws-bgp#-create-connections
If possible, please share the details of your configuration either in a file or snapshots so I can verify further. Thank you!