Hello @MayankBargali-MSFT sorry for my late response.
What I've ended up doing was the following.
I have created key vault secrets. In those key vault secrets I store the workflow url containing the authorization secret.
As I've created the other workflows pointing to the key vault secret name instead of a hardcoded url the logic app at run time will query the key vault, retrieve the url from the workflow i want to authenticate to and use it as input. As it already contains the signature it authenticates correctly.
It's probably a workaround but it was the only way I was able to achieve success in this operation.
For those with the same problem as me here are the steps:
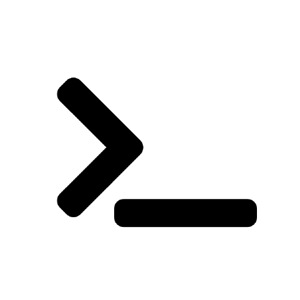
- First I have developed the workflow to obtain the secret containing the url from the keyvault
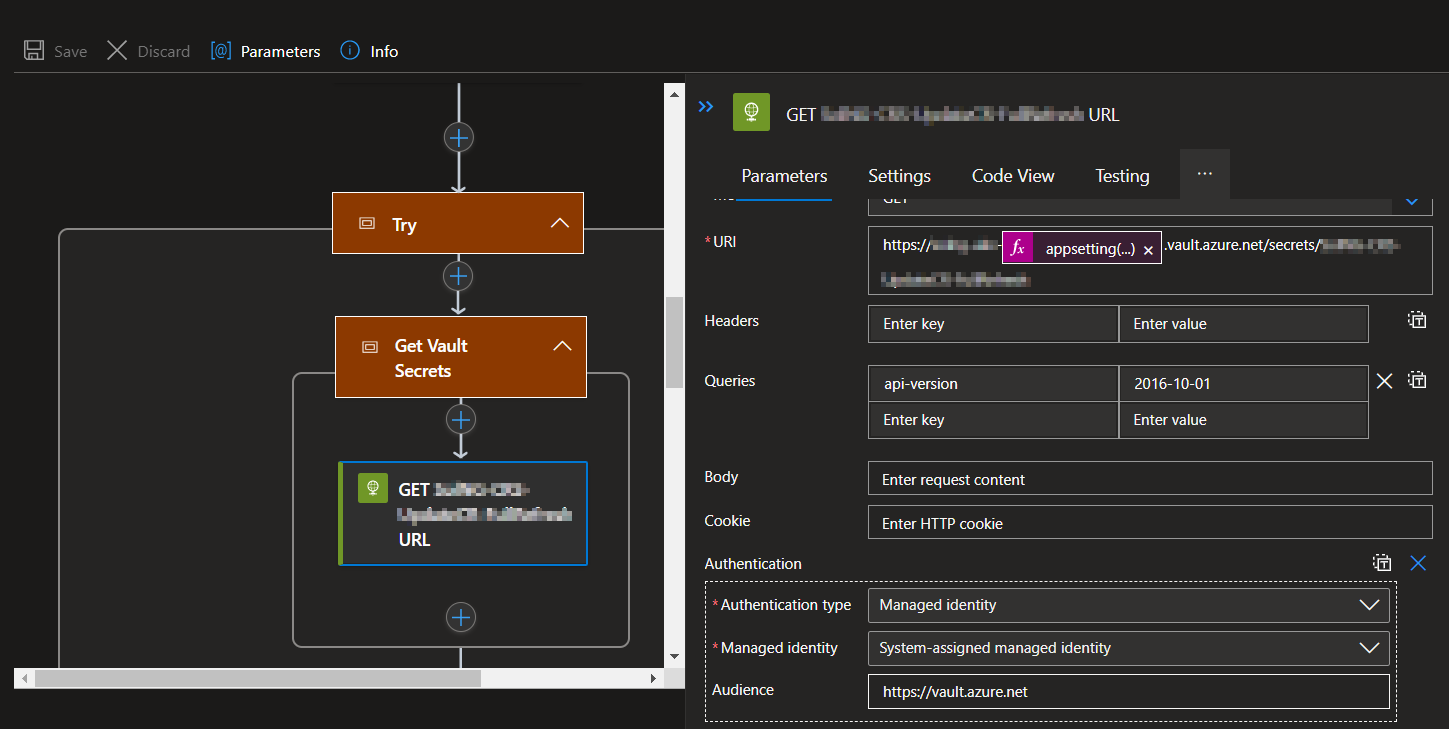
- Then it calls the url using the secret as input.
- When I have my workflows ready to deploy. I export them and put the code on Azure Devops.
- Then in a build pipeline I use the following tasks:
- task: ArchiveFiles@2
displayName: "Archive Functions"
inputs:
rootFolderOrFile: "$(Build.Repository.LocalPath)/LogicApps"
includeRootFolder: false
archiveFile: "$(Build.ArtifactStagingDirectory)/LogicApps.zip"- task: AzureFunctionApp@1
displayName: "Deploy Functions"
inputs:
azureSubscription: "${<!-- -->{ parameters.Subscription }}"
appName: "mylogicappstandard"
package: "$(Agent.BuildDirectory)/${<!-- -->{ parameters.ArtifactName}}/LogicApps.zip"
- task: AzureFunctionApp@1
- task: AzureCLI@2
displayName: 'Update Signature url in ${<!-- -->{ parameters.KeyvaultName}}'
inputs:
azureSubscription: "${<!-- -->{ parameters.Subscription }}"
scriptType: 'ps'
scriptLocation: 'inlineScript'
inlineScript: "$(Agent.BuildDirectory)/${<!-- -->{ parameters.ArtifactName}}/Scripts/Get-WorkflowUrlSignature.ps1 $(AzureSubscriptionId) ${<!-- -->{ parameters.ResourceGroup }} mylogicappstandard ${<!-- -->{ parameters.KeyvaultName}}"
- task: ArchiveFiles@2
You can find the details for the script here Get-WorkflowUrlSignature.ps1
[CmdletBinding()]
param (
[Parameter(Mandatory)][string]$SubscriptionId,
[Parameter(Mandatory)][string]$ResourceGroup,
[Parameter(Mandatory)][string]$LogicAppName,
[Parameter(Mandatory)][string]$KeyVaultName
)
$json = az rest --method get --uri "https://management.azure.com/subscriptions/$SubscriptionId/resourceGroups/$ResourceGroup/providers/Microsoft.Web/sites/$LogicAppName/hostruntime/runtime/webhooks/workflow/api/management/workflows?api-version=2018-11-01"
$workflows = $json | convertfrom-json
foreach ($workflow in $workflows.Name){
$uri ="https://management.azure.com/subscriptions/$SubscriptionId/resourceGroups/$ResourceGroup/providers/Microsoft.Web/sites/$LogicAppName/hostruntime/runtime/webhooks/workflow/api/management/workflows/$workflow/triggers/manual/listCallbackUrl?api-version=2018-11-01"
if (az rest --method post --uri $uri){
# Gets the url with signature
$sigurl = az rest --method post --uri $uri | convertfrom-json
$secret = $sigurl.value.Replace('&','"&"')
$workflowName = $workflow.Replace("_","")
#Creates or updates secret in the keyvault
Write-Output "Updating secret $workflowName in the keyvault"
az keyvault secret set --name $workflowName --vault-name $KeyVaultName --value $secret
}else{
Write-Output "The workflow $workflow does not have any trigger url"
}
}
I hope this helps other people automate the process. Please let me know if you have an easier way to do it or to query the access key or url sig.