Hi @Eric Vanderveer ,
Problem summary
While logging in with a particular Azure AD user, you receive the error, "The user has not been granted the requested logon type at this machine."
The account has been added to a security policy that allows it to log on locally, but it still can't log in. This happens on one Azure AD user account in particular, but does not happen on all accounts.
Troubleshooting steps
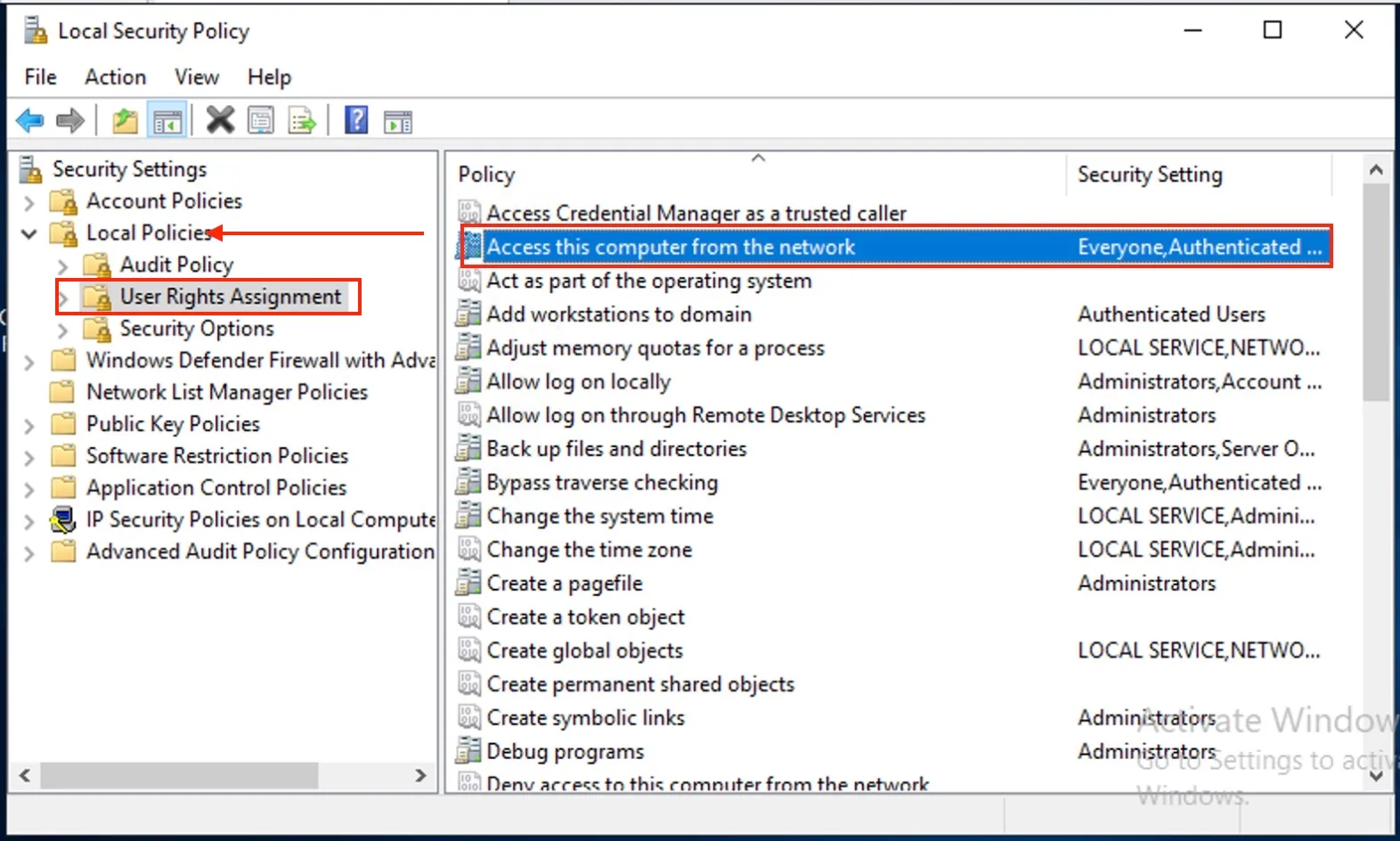
1) This error can occur if the desktop policy Access this computer from the network has been modified from the default values so that the users and groups listed in this policy no longer contain the user or group entries for the particular user logging on.
To resolve this issue, edit the Access this computer from the network local policy on the desktop to restore the "Users" access group or add one or more user and group values to provide the required access.
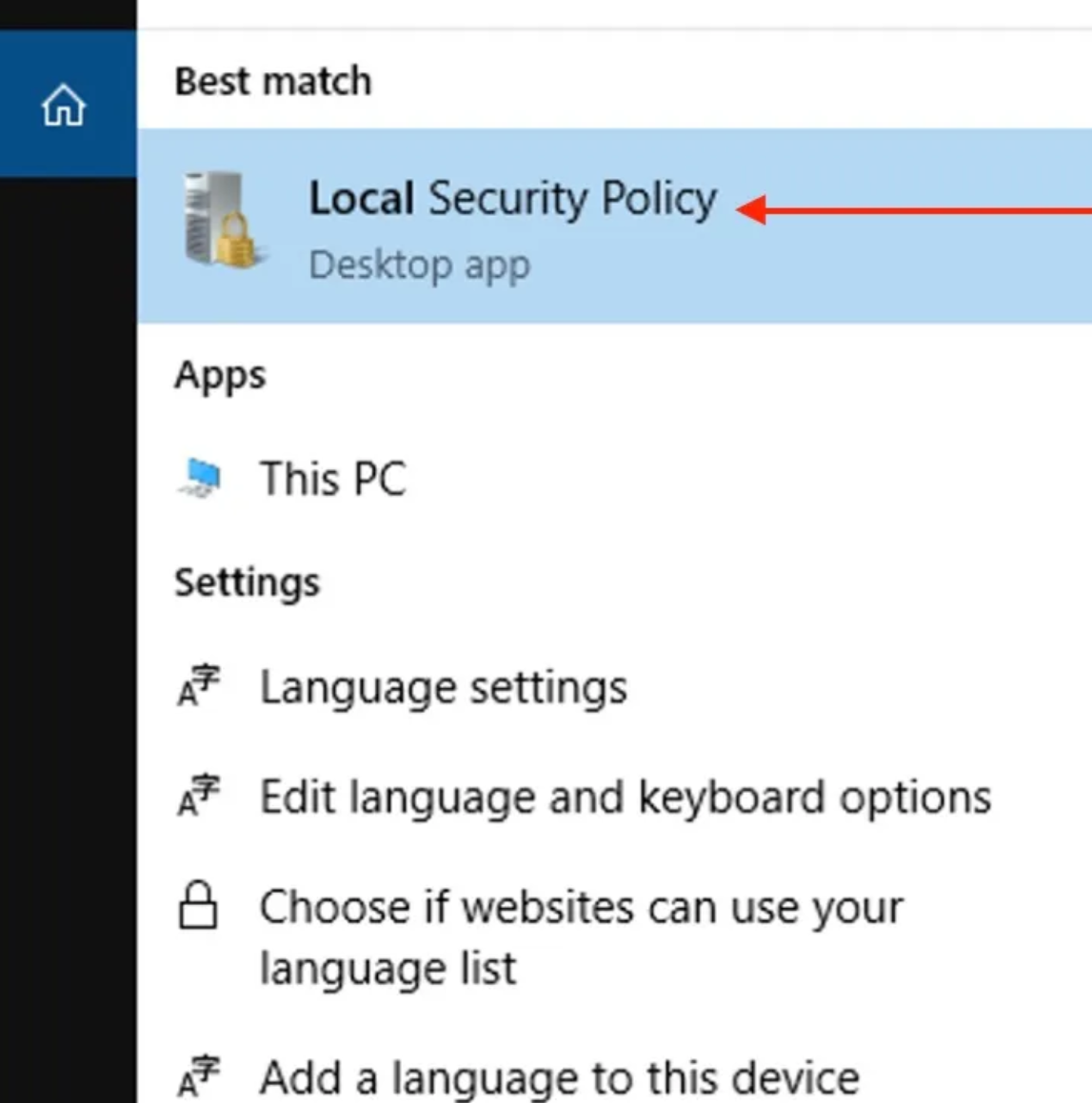
This can also be configured under Computer Configuration > Windows Settings> Security Settings > Local Policies > User Rights Assignment.
Also, ensure that "Deny logon locally" is not applied to the same user or group containing the user.
2) After adding the user to the "Allow Logon Locally" policy or default domain controller policy, ensure that gpupdate /force to ensure that the policy update has been applied.
3) If this is a Domain Controller and they're logging on via batch queue tool such as Task Scheduler, check if the user account or the group to which it belongs to is added to the Logon as a batch job Policy in the Windows Domain Controller Security Policy.
Let me know if you are still facing this issue after trying these steps.
References and additional resources:
The user has not been granted
Error 1385: The user has not been granted the requested logon type at this time
Error 1385