Hi @Florian ARGUAIROLLES ,
I understand that you are having an issue with a device that is unjoining and losing its hybrid Azure AD joined status after a user opens his session from home without a VPN.
The machine needs connectivity to a domain controller to finalize the Hybrid Azure AD Join process. This can be either through the internal network or via VPN.
If the machine was not registered properly or had not completed the hybrid join, you can run into this issue. If this is the case, you may need to un-register the device, re-register it, remove the SSL certs on the PC, and reinitiate them to fix the problem. This will need to be done while the device is on the internal network or connected via VPN.
There are additional troubleshooting steps in this guide that goes over potential hybrid join issues and how to fix them. From the guide:
Sometimes, a machine can be in an inconsistent registration state in Azure Active Directory. This can happen because:
The machine was shut down during a long time, and the Azure AD device registration certificate is expired (located in Local Machine / Certificates / Personal)
Someone manually deleted the device registration certificate
Someone manually deleted the device object in the Azure AD portal
The machine is registered in another Azure AD tenant
Another possibility is that there might be a policy in place that is blocking the user, especially if the user may have attempted a password change. You always need a VPN with Hybrid Join if the user changed the password on the corporate network and then went home.
The FAQ discusses this scenario here:
What happens if a user changes their password and tries to sign in to their Windows 10/11 hybrid Azure AD joined device outside the corporate network?
When a device does not have line of sight to the domain controller, it is unable to validate the new password. So, user needs to establish connection with the domain controller (either via VPN or being in the corporate network) before they're able to sign in to the device with their new password. Otherwise, they can only sign in with their old password because of cached sign in capability in Windows. However, the old password is invalidated by Azure AD during token requests and hence, prevents single sign-on and fails any device-based Conditional Access policies until the user authenticates with their new password in an app or browser.
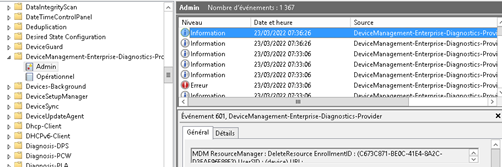
Note also that Event ID 102 will be logged when the auto enrollment task is complete, regardless of whether or not the auto enrollment succeeds.
Let me know if these steps are helpful to you and if you still run into this issue.
Additional troubleshooting steps:
Troubleshoot Hybrid Join
Manually re-register a Windows 10 or Windows Server machine in Hybrid Azure AD Join
Troubleshooting Windows 10 Group Policy-based auto-enrollment in Intune
-
If this answer helped you resolve the issue, please consider marking as answer so that others in the community with similar problems can more easily find a solution.