Remove /disable individual MFA from users that need to access virtual machines. You will still be able to protect your data by using a Conditional Access Policy in the Azure Portal. After using an ID that does not have individual MFA enabled or enforced, the web version works very well.
Virtual Desktop Via Web Browser
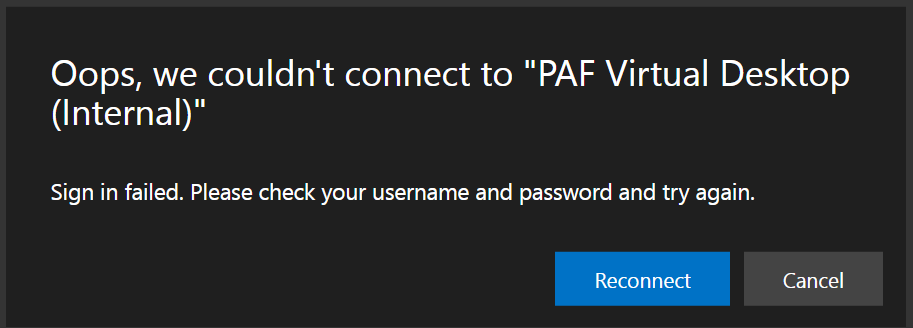
I get this message when trying to connect via a browser, but it works just fine when using the desktop app. Any thoughts on why this would be? I don't see anything from a network gateway perspective that would indicate anything being blocked.
2 answers
Sort by: Most helpful
-
-
 Prrudram-MSFT 25,166 Reputation points
Prrudram-MSFT 25,166 Reputation points2022-04-14T11:09:30.817+00:00 Hello @Philip Barr ,
Do you have Azure Virtual Desktop Screen Capture Protection(SCP) enabled? SCP only works with the windows client (MSRDC), so accessing it from another client is prevented.
Edit:
Adding the details for your understanding:
Prerequisites
The screen capture protection feature is configured on the session host level and enforced on the client. Only clients that support this feature can connect to the remote session. Following clients currently support screen capture protection:Windows Desktop client supports screen capture protection for full desktops only.
macOS client version 10.7.0 or later supports screen capture protection for both RemoteApp and full desktops.
"Suppose the user attempts to use an unsupported client to connect to the protected session host. In that case, the connection will fail with error 0x1151"Reference : https://learn.microsoft.com/en-us/azure/virtual-desktop/screen-capture-protection#prerequisites
Hope this helps!
Please do not forget to "Accept the answer" wherever the information provided helps you to help others in the community.