Hi @Neha ,
A deny assignment gets created when you select a blueprint lock type. This is described in the article here: https://learn.microsoft.com/en-us/azure/governance/blueprints/tutorials/protect-new-resources
You can't apply the deny assignments to existing resources, but you can add it during the creation of new ones.
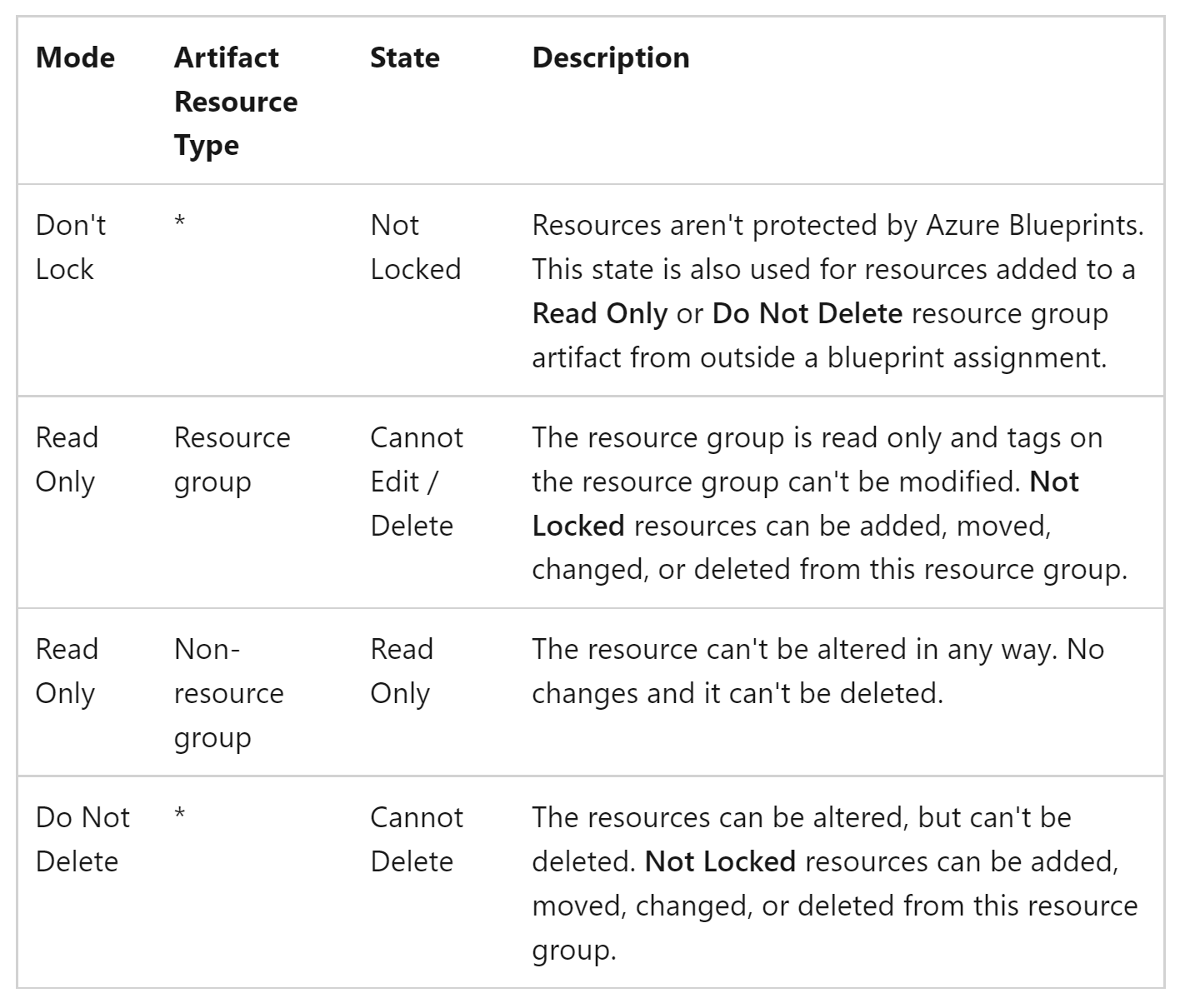
If you apply the resource locks, you can block subscription owners from editing or deleting the resource group. However, based on the existing locks you cannot block Read access or apply the same granular level of control that you can apply using regular RBAC. The table of existing Locking Modes is defined here:
If you are looking for a way to add this type of granularity you can make a feature request in the Ideas forum, though. In most cases it makes sense for subscription-level roles to have the ability to control the resources within that subscription. The resource locks are an exception as a way to prevent accidental or programmatic deletion or alteration.
-
If the information provided was helpful to you, please remember to "mark as answer" so that others searching for this information can more easily find the solution.