Hello @Punuri Sandhya Kiranmayi ,
Thank you for reaching out to the Microsoft Q&A platform. Happy to answer your question.
The standard recommended approach for this scenario is azure site recovery Azure to Azure replication and migration, aka A2A approach. This method allows you to replicate and migrate azure disk encrypted VMs to another subscription under same tenant (Please note).
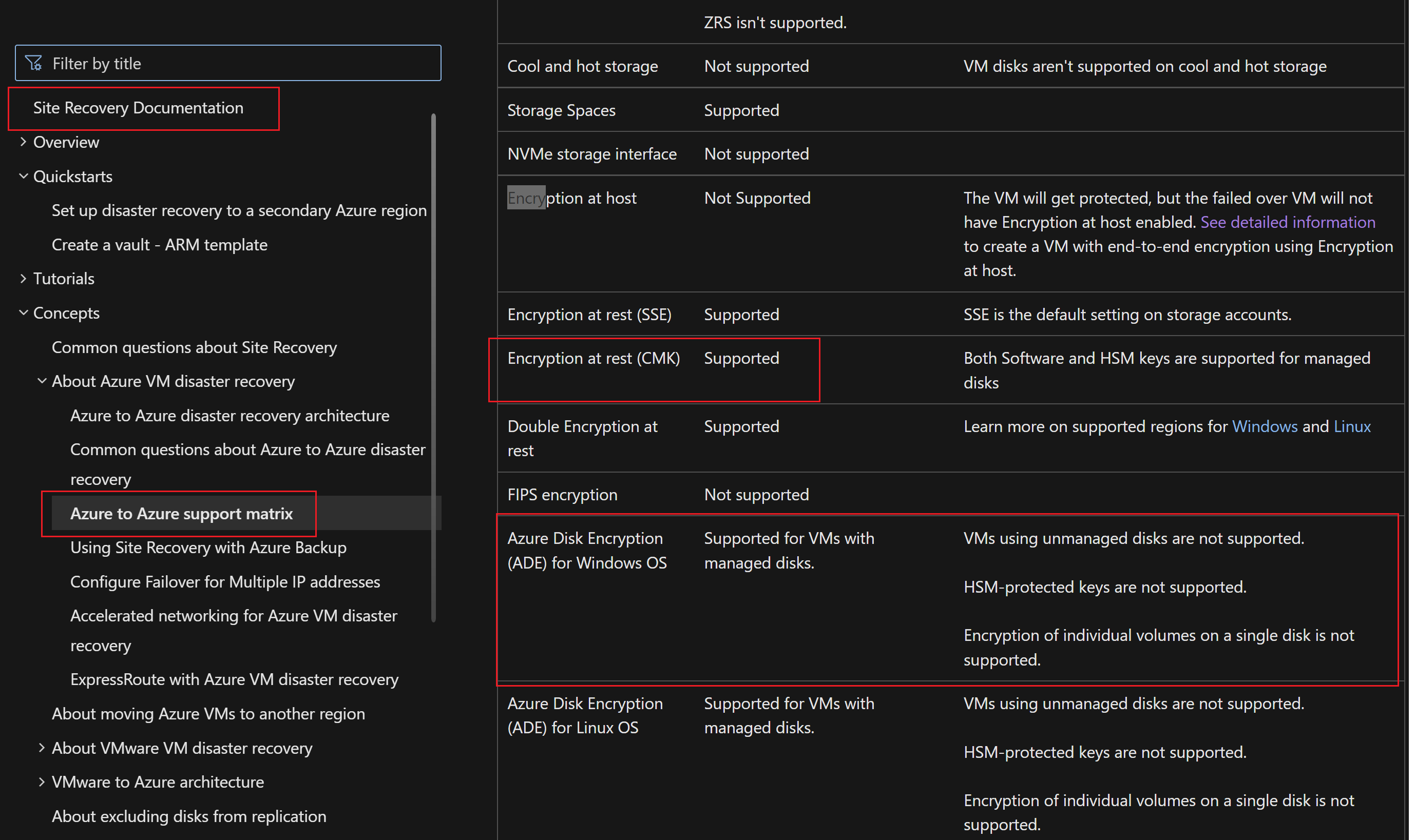
Adding support matrix and document link for your reference:
https://learn.microsoft.com/en-us/azure/site-recovery/azure-to-azure-support-matrix
How to guide :
https://learn.microsoft.com/en-us/azure/site-recovery/azure-to-azure-how-to-enable-replication-ade-vms
Important points to note:
Customizing target settings while enabling replication of VM to the target subscription.
Customize target resources:
Follow these steps to modify the Site Recovery default target settings.
Select Customize next to "Target subscription" to modify the default target subscription. Select the subscription from the list of subscriptions that are available in the Azure AD tenant.
Select Customize next to "Resource group, Network, Storage, and Availability sets" to modify the following default settings:
- For Target resource group, select the resource group from the list of resource groups in the target location of the subscription.
- For Target virtual network, select the network from a list of virtual networks in the target location.
- For Availability set, you can add availability set settings to the VM, if they're part of an availability set in the source region.
- For Target Storage accounts, select the account to use.
- Select Customize next to "Encryption settings" to modify the following default settings:
For Target disk encryption key vault, select the target disk encryption key vault from the list of key vaults in the target location of the subscription.
For Target key encryption key vault, select the target key encryption key vault from the list of key vaults in the target location of the subscription.
Option: 2
Another approach is Azure Resource Manager. However, you can't move a virtual machine that is integrated with a key vault to implement Azure Disk Encryption for Linux VMs or Azure Disk Encryption for Windows VMs. To move the VM, you must disable encryption. For details you can refer to the following document link
https://learn.microsoft.com/en-us/azure/azure-resource-manager/management/move-limitations/virtual-machines-move-limitations?tabs=azure-cli#azure-disk-encryption
Hope this helps
--please don't forget to upvote and accept as answer if the reply is helpful--
