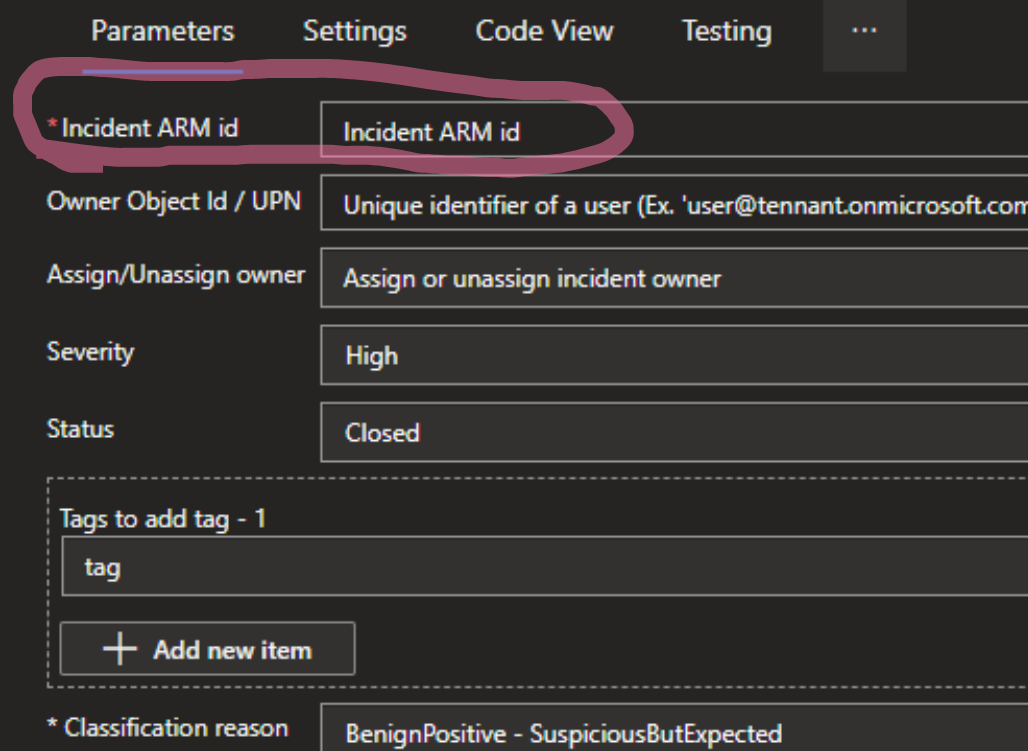
You can use the following query.
SecurityIncident
| where IncidentNumber == XXX // This line is optional, only for testing purposes
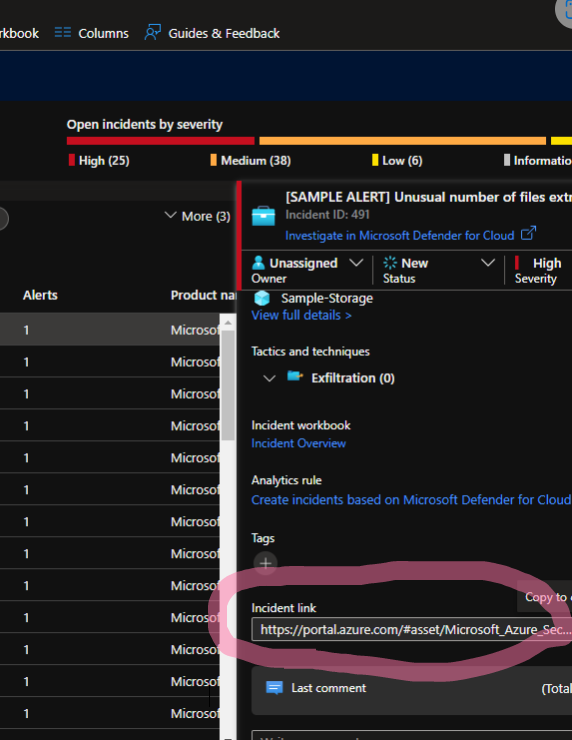
| extend IncidentUrl = tostring(IncidentUrl) // Ensure that the field is treated as a string
| extend SubstringStart = indexof(IncidentUrl, "/subscriptions") // Find the index where "/subscriptions" appears in the URL
| extend IncidentArmId = substring(IncidentUrl, SubstringStart) // Extract the substring starting from the index
| distinct IncidentArmId
| project IncidentArmId