Hi there,
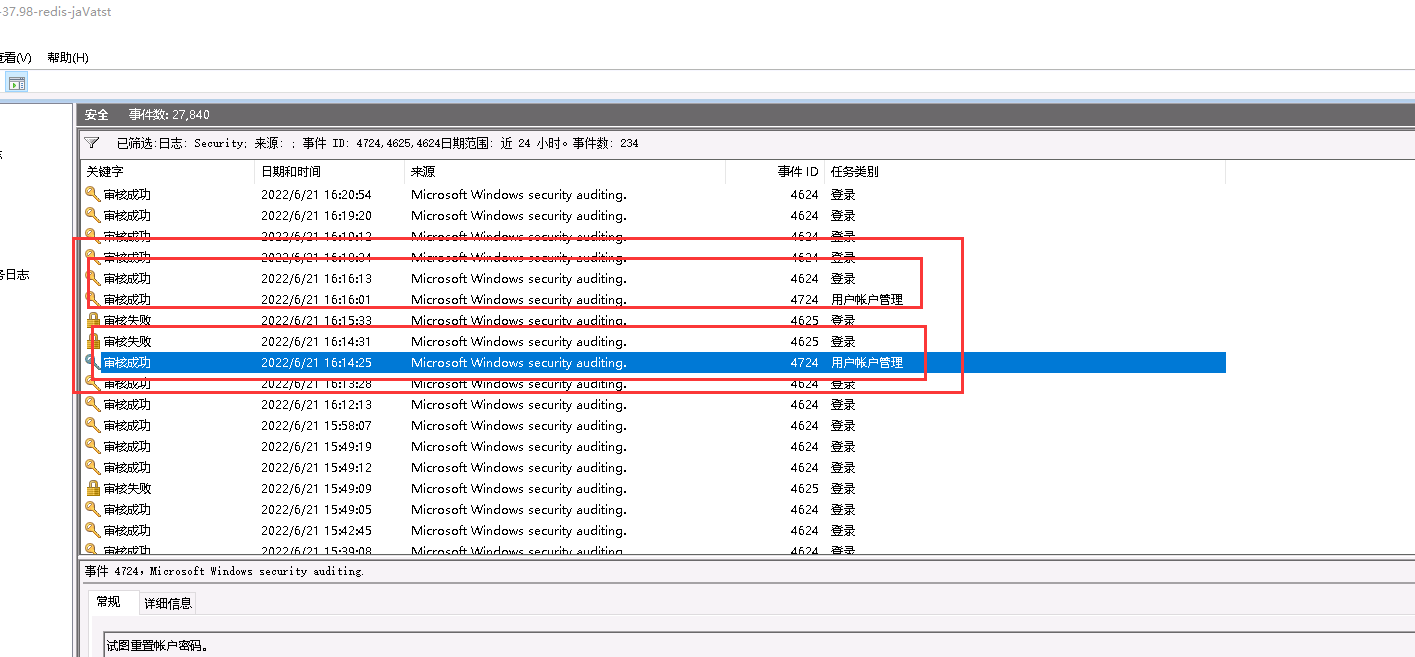
Can you see any other event ID ?
Event ID 4724 is generated every time an account attempts to reset the password for another account (both user and computer accounts). If the new password fails to meet the domain password policy (or local password policy in local user accounts) then a failure event is recorded.
This is an information event and no user action is required.
4724(S, F): An attempt was made to reset an account's password. https://learn.microsoft.com/en-us/windows/security/threat-protection/auditing/event-4724
---------------------------------------------------------------------------------------------------------------------------------------
--If the reply is helpful, please Upvote and Accept it as an answer--