Hi @Gary Reynolds ,
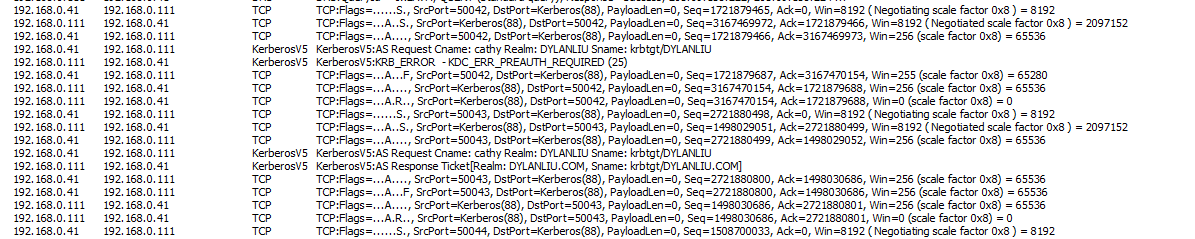
For my application, I will trigger something when the client goes through kerberos AS request,
so the different behavior of unlock screen and logon bothers me a lot.
I think your answer haven't solved my question but still thank for your reply, and here I list a real case example.
For example:
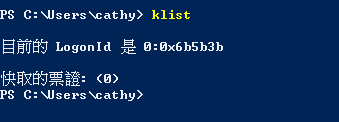
(1) If user logoff after he unlocks screen, client has no TGT
He will go through whole the kerberos event (as->tgs), so my application will trigger. But this is not what I want.
(2) If user logoff without unlocking screen, client holds TGT
He will go through kerberos event (tgs), and my application will not trigger. This is the correct operation I want.
As my understanding, AS response ticket from server contains TGT ticket(Protocol Description from Wiki), and client will cache the TGT in AS response for further service.
https://en.wikipedia.org/wiki/Kerberos_(protocol)
User logon event will cache TGT, and unlock screen will not.(They all go through whole kerberos as -> tgt)
This is the weird point I think, and I want to know the reason.