Hello there,
Done that 4 years ago for ~4000 remote laptops.
On a high level, the task sequence looks like this:
- Prepare the windows environment for bitlocker. Be sure not to assign any configuration profiles (MEM) or GPOs (if controlled via GPO) to the endpoints just yet. Follow this post https://learn.microsoft.com/en-us/windows/security/information-protection/bitlocker/prepare-your-organization-for-bitlocker-planning-and-policies
- Using McAfee EPO, create a decryption policy - you can check this post on actions to perform: https://communitym.trellix.com/t5/ePolicy-Orchestrator-ePO/Decrypt-Laptops-via-an-policy-on-the-ePO-Server/td-p/447965
- Once a batch of laptops is decrypted (and rebooted), you can then assign the configuration profile (MEM) or GPO to the batch.
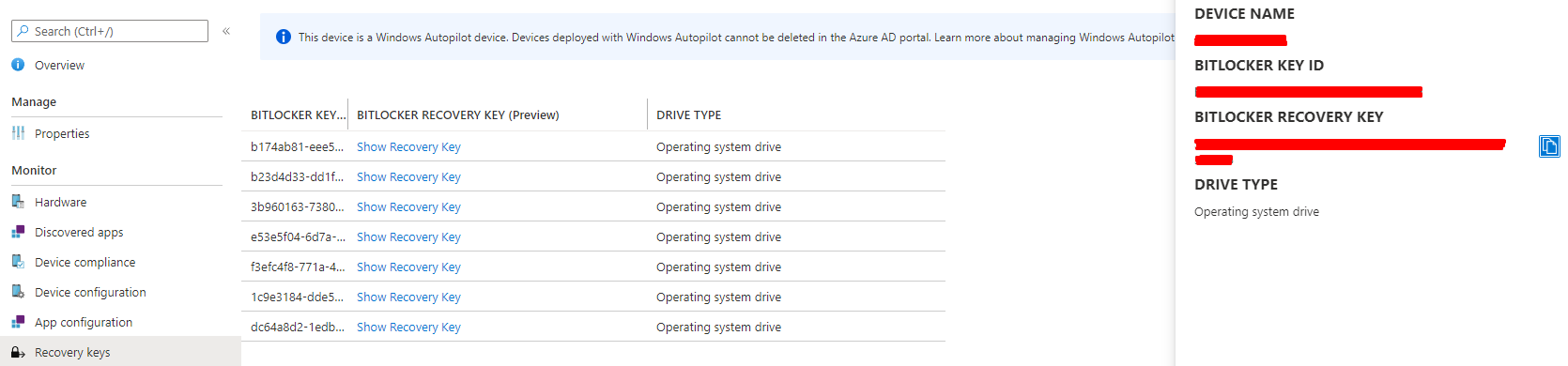
- Verify the disks are encrypted via your endpoint management utility, verify the recovery keys are synced to AD or AAD (whatever you configured).
As for speed, unfortunately you will be limited by the size of the encrypted drives and the CPU/disk speeds. This will take hours, but users can still work/use their laptops while the operation completes. Normal shutdowns (user initiated, scheduled, updated, etc) do not affect this. The decryption will be paused and resumed when the system is operational again.
Before doing this en masse, test the task sequence with few test laptops to ensure that there is nothing preventing you from completing the process.
Regards,
Rosen